Pictured: a developing at Microsoft Company headquarters in Redmond, Washington. (Coolcaesar/CC BY-SA 4.0via Wikimedia Commons)
Microsoft Teams is susceptible to the exact same phishing dangers, impersonation cons and privacy violations as email is, but lots of customers naïvely treat this and other workplace communications platforms with inherent have confidence in. As a outcome, they frequently share delicate facts far too freely or click on back links and open up attachments that in an email they could ignore, warns a new report.
Above the previous 12 months, the rapid adoption and elevated usage of platforms these kinds of as Groups, Slack or Google Hangouts because of to COVID-19 has only improved the chance that a rising amount of cybercriminals will check out to acquire benefit of this misplaced believe in.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“As employees transfer away from email and use messaging platforms… malicious actors have followed them. With a deficiency of instruction and awareness of threats, people are eager to share more on company messaging platforms, as they consider other end users can be trustworthy,” said Chris Hazelton, director of security solutions at Lookout.
As a result, it is up to companies to be certain that their personnel are correctly properly trained in the liable use of these applications.
Introduced currently, the Microsoft Teams Security Report was authored by cloud email security corporation Avanan, a Microsoft partner that analyzed almost 200 business clients around a two-thirty day period span in a quest to seek out out vulnerabilities, exploits and attacks relevant to Groups usage.
 Gil Friedrich, CEO of Avanan
Gil Friedrich, CEO of Avanan
Gil Friedrich, CEO of Avanan, advised SC Media in an job interview that when adversaries target prospective victims, there is a notable big difference among email and Groups. With email, any person can instantly arrive at out to any acknowledged email addresses of option, but a Teams information requires that the sender and recipient are aspect of the very same team account or channel. But people should not assume this helps make them harmless, as this is not as terrific of an obstacle as it seems.
The dilemma is that team accounts can rapidly come to be large and unwieldly with a number of 3rd-party associates all on the very same channel. And if just just one user among these partners is compromised and finally impersonated, then all users of that channel can possibly be tricked.
“And so you must be additional mindful in people environments with facts you share as very well as that with the things you download, etc., simply because you cannot really control the security of your associates,” claimed Friedrich to SC Media.
Indeed, a person of the most substantial discoveries by Avanan scientists was an actual malware attack directed from an unnamed economical business that was functioning with a third-party partner group with whom it communicated by way of a shared Teams channel. Evidently, the associate experienced just one of its accounts compromised for a yr.
Cleverly, the malicious actors didn’t immediately power the issue and attack. As a substitute, they carried out reconnaissance, gathered intel and strategically waited for an organic chance to mail a destructive file. Only right after the hackers noticed a request for files, did they strike, sending a destructive zip file that purportedly contained the asked for documents. In reality, the zip file in fact incorporated a Remote Entry Trojan that allows desktop checking and regulate.
“In order to evade detection in this new medium, hackers would relatively hold out for when they can make the greatest affect with the least probable detection,” the report suggests. For that rationale, a Teams-dependent phishing marketing campaign may exhibit a lot more strategic patience on the element of the attacker than an email-primarily based phishing marketing campaign.
Friedrich said that Avanan blocked the attack, and the financial business at minimum briefly expelled outside corporations from its Teams channel, restricting it to internal communications.
But how was the preliminary third-party compromise completed in the first location? In accordance to the report, there are numerous strategies to hijack or steal one’s Group account credentials. For starters, Teams uses the similar credentials as Microsoft 365. So if someone’s Microsoft 365 qualifications are stolen, so are his or her Teams qualifications. Additionally, Avanan uncovered viral destructive GIF picture of a cat that was uploaded to Groups and shared with customers. Clicking on it would let malicious hackers to harvest a user’s session token, and then impersonate that personal.
The Avanan report also notes how some companies allow exterior people to join a group and build an account employing any random identity and photograph they so pick out – a characteristic that could consequence in an impersonation scam. In truth, the aforementioned financial establishment attackers leveraged this pretty element, disguising themselves as a respectable user.
Importantly, the examine also noted that Teams customers can pose a threat to them selves even without the interference of an attacker. For occasion, some customers share very sensitive details by way of Groups with buyers who are equally inside of and outside of their fast businesses – thereby jogging the risk of data decline or even privacy violations.
“Users might believe that many others in a team can be reliable, believing users are vetted prior to staying additional. This can guide to leakage of company data that would not usually be shared,” claimed Hazelton.
“Teams [the product]… has the inherent ability to mislead customers that all many others are on the same aspect. The psychology of information security performs a role in this article,” stated Mark Kedgley, main technology officer at New Net Systems. “Collaboration demands a particular stage of believe in, which is normally founded by administration directives (‘We are going to cooperate with organization XYZ the NDA is now in place’), which provides to the misleading. The need to differentiate concerning every company partnership and what sort of information and facts can be shared is also often diminished as staff members is not effectively trained.”
In one particular scenario, a hospital buyer of Avanan that uses Teams was uncovered to liberally share patients’ healthcare facts with hundreds of stop customers via the system. “Medical team typically know the security procedures and risk of sharing facts through email, but disregard those people when it arrives to Groups. In their mind, anything can be despatched,” the report states.
For instance, “medical details, methods and loved ones circumstances of a insignificant, was shared jointly with her identify and social security selection,” the report suggests. And although the use of Groups may help medical professionals talk promptly to make lifetime-conserving selections, it still demonstrates they may well will need extra steering on use of the system.
“When providers use Teams, they suppose it is inner and unmonitored. Appropriately, the conclude-consumer habits we discovered throughout this assessment noticed totally free sharing of all knowledge. Conclusion-customers freely share documents, data, spreadsheets and delicate data, typically with out considering,” the report claims. “There’s anything really informal, nearly instantaneous” about several of these conversations, stated Friedrich.
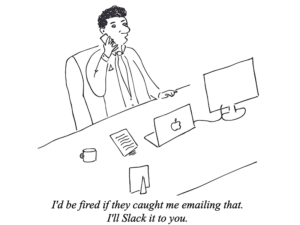 Original cartoon courtesy of Avanan.
Original cartoon courtesy of Avanan.
Certainly, Groups is constructed for swift conversation between events with a shared curiosity. Since of that, hyperlinks in chats are not scanned. Documents are scanned as they’re saved to OneDrive, but only for known malware signatures and not in genuine time – so in that sense it’s a lot easier to sneak in malware undetected. (Introducing Microsoft ATP defense assists, though this as well can be bypassed by identified attackers.) “The way all-around it is to teach your users to be additional thorough with that content and just to know that this is how this platform behaves,” defined Friedrich.
Malware, impersonation and lateral attackers ended up identified as the most common threats affecting Teams users. Furthermore, Avanan scientists basis a zero-click on cross-web page scripting vulnerability that Microsoft repaired final December. In addition to improved teaching and schooling, industry experts had solutions for how organizations can lower the risk of this kind of threats.
“More target on minimum privilege is wanted as it’s even now too widespread for buyers to operate with local admin rights,” stated Kedgley. Moreover, corporations ought to stick to “config hardening assistance from the CIS or STIG playbooks.” Email and office environment apps deliver a total bunch of hardened options to beat malware and phishing, but as well several organizations make use of them. Transform regulate and vulnerability management as main security controls need to be in spot as properly.
“Organizations want to add security in the cloud and across all the endpoints: laptops, telephones, and tablets – wherever these discussions are using position,” reported Hazelton. “This will allow companies to establish phishing attacks as they transpire, and immediately respond when malware is launched by means of a messaging platform.”
Friedrich reported Microsoft was a cooperative husband or wife in the course of the examine. “They have all the interest to make [Teams] as secure as possible for their customers. So we got a whole lot of assistance from from their engineering workforce,” such as having highly developed obtain to the Teams API.
Microsoft did not promptly react to requests for comment.
Some pieces of this article are sourced from:
www.scmagazine.com


 DarkSide decryptor unlocks systems without ransom payment – for now
DarkSide decryptor unlocks systems without ransom payment – for now