As the investigation into the SolarWinds supply-chain attack carries on, cybersecurity scientists have disclosed a third malware strain that was deployed into the establish setting to inject the backdoor into the company’s Orion network checking platform.
Termed “Sunspot,” the backdoor provides to a expanding list of earlier disclosed malicious program this kind of as Sunburst and Teardrop.
“This hugely sophisticated and novel code was built to inject the Sunburst destructive code into the SolarWinds Orion Platform with no arousing the suspicion of our application improvement and build groups,” SolarWinds’ new CEO Sudhakar Ramakrishna explained.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Although preliminary evidence discovered that operators behind the espionage campaign managed to compromise the software package create and code signing infrastructure of SolarWinds Orion system as early as October 2019 to provide the Sunburst backdoor, the most recent conclusions reveal a new timeline that establishes the to start with breach of SolarWinds network on September 4, 2019 — all carried out with an intent to deploy Sunspot.
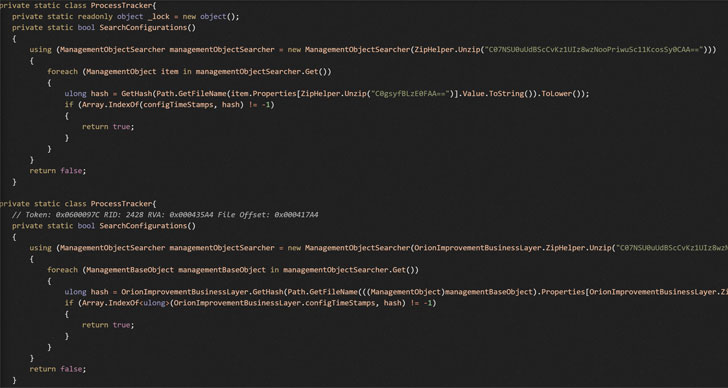
“Sunspot monitors running procedures for all those included in compilation of the Orion product and replaces one of the supply files to contain the Sunburst backdoor code,” Crowdstrike researchers explained in a Monday assessment.
Crowdstrike is monitoring the intrusion under the moniker “StellarParticle.”
At the time set up, the malware (“taskhostsvc.exe”) grants by itself debugging privileges and sets about its task of hijacking the Orion build a workflow by checking operating computer software processes on the server, only to change a supply code file in the build listing with a malicious variant to inject Sunburst whilst Orion is staying crafted.
The subsequent Oct 2019 version of the Orion System launch appears to have contained modifications built to exam the perpetrators’ capability to insert code into our builds,” Ramakrishna said, echoing former experiences from ReversingLabs.
The development will come as Kaspersky researchers discovered what seems to be a initial possible link concerning Sunburst and Kazuar, a malware relatives linked to Russia’s Turla state-sponsored cyber-espionage outfit.
The cybersecurity company, on the other hand, refrained from drawing as well lots of inferences from the similarities, in its place suggesting that the overlaps might have been intentionally extra to mislead attribution.
Whilst the overlaps are considerably from a cigarette smoking gun tying the hack to Russia, U.S. federal government officers previous 7 days formally pinned the Solorigate operation on an adversary “possible Russian in origin.”
Uncovered this write-up exciting? Observe THN on Facebook, Twitter and LinkedIn to read far more distinctive content material we post.
Some elements of this report are sourced from:
thehackernews.com

 ‘I’ll Teams you’: Employees assume security of links, file sharing via Microsoft comms platform
‘I’ll Teams you’: Employees assume security of links, file sharing via Microsoft comms platform