The attack infrastructure made use of to focus on Cisco in the Might 2022 incident was also employed from an tried compromise of an unnamed workforce administration answers keeping corporation a month earlier in April 2022.
Cybersecurity company Sentire, which disclosed the findings, raised the likelihood that the intrusions could be the do the job of a felony actor identified as mx1r, who is explained to be a member of the Evil Corp affiliate cluster dubbed UNC2165.
Evil Corp, the progenitors of the infamous Dridex banking trojan, have, above the a long time, refined their modus operandi to operate a sequence of ransomware operations to sidestep sanctions imposed by the U.S. Treasury in December 2019.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

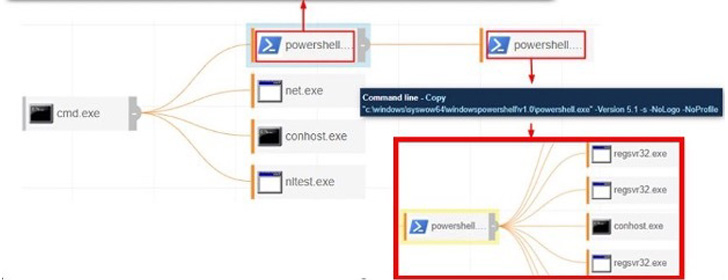
First access to the company’s IT network was built feasible by employing stolen Digital Private Network (VPN) qualifications, followed by leveraging off-the-shelf applications for lateral movement and attaining further access into the victim’s setting.
“Working with Cobalt Strike, the attackers were equipped to achieve an original foothold and hands-on-steps had been quick and swift from the time of original access to when the attacker was able to register their individual Digital Machine on the victim’s VPN network,” eSentire observed.
mx1r’s ties to UNC2165 stems from overlaps in methods and tactics with that of UNC2165, such as staging a Kerberoasting attack versus the Lively Listing service and the use of Distant Desktop Protocol (RDP) access for propagating within just the company’s network.
The connections notwithstanding, the Cobalt Strike “HiveStrike” infrastructure utilised to mount the attack is stated to match that of a Conti ransomware affiliate earlier regarded to deploy Hive and Yanluowang strains, the latter of which has because posted information stolen from the Cisco breach in late May well 2022 to its facts leak web page.

The networking equipment maker attributed the incident to an original obtain broker (IAB) with backlinks to a few different collectives: UNC2447, LAPSUS$, and Yanluowang ransomware.
“It appears unlikely — but not not possible — that Conti would lend its infrastructure to Evil Corp,” eSentire mentioned. In light-weight of UNC2165’s modern pivot to LockBit ransomware, the corporation claimed “it is extra plausible that the Evil Corp affiliate/UNC2165 could be doing the job with a single of Conti’s new subsidiaries.”
“It really is also achievable that first access was brokered by an Evil Corp affiliate but in the end marketed off to Hive operators and its affiliate marketers,” it even more additional.
Found this posting interesting? Adhere to THN on Fb, Twitter and LinkedIn to read through more distinctive content we publish.
Some areas of this posting are sourced from:
thehackernews.com


 Standards Body Publishes Guidelines for IoT Security Testing
Standards Body Publishes Guidelines for IoT Security Testing