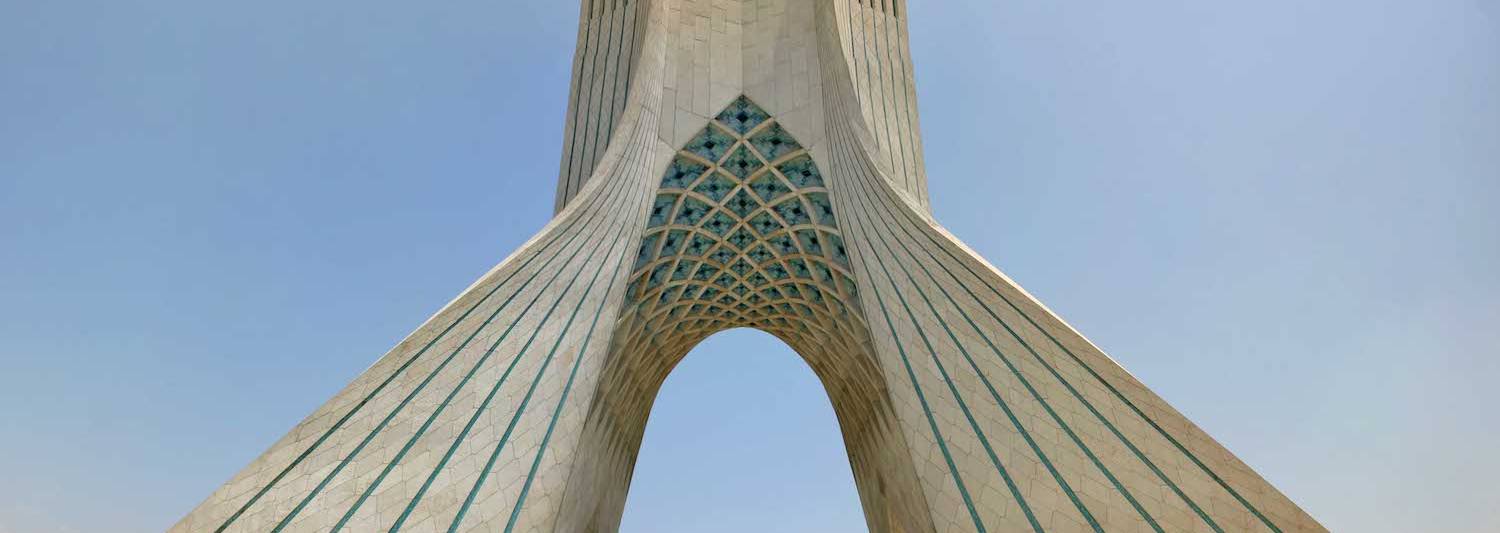
The Azadi Tower in Tehran, Iran. (Christiaan Triebert, CC BY 2. https://creativecommons.org/licenses/by/2., by means of Wikimedia Commons)
In late 2020, a well-regarded hacker team thought to be sponsored by the Iranian federal government started out a credential harvesting marketing campaign focusing on United States and Israeli professional medical staff, according to new exploration from Proofpoint.
Scientists attribute the campaign, which it has dubbed “BadBlood,” to Charming Kitten, also known as Phosphorous or, in Proofpoint’s parlance, TA453.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Sherrod DeGrippo, senior director of menace study and detection at Proofpoint, noted that the selection of targets is an interesting attribute of the marketing campaign.
“TA453 usually concentrates on focusing on dissidents, teachers, diplomats, and journalists. BadBlood shifted focusing on to medical exploration (genetics, oncology, and neurology) and perhaps patient-relevant info,” she advised SC Media by way of email.
Proofpoint has no conclusive sense of what the drive was for the campaign.
“As collaboration for clinical investigation is usually performed informally more than email,” mentioned DeGrippo, “this marketing campaign may possibly show that a subset of TA453 operators have an intelligence requirement to obtain certain professional medical details linked to genetic, oncology, or neurology study. Alternatively, this marketing campaign may well display an interest in the individual info of the qualified healthcare personnel or an purpose to use the recipients’ accounts in more phishing strategies.”
BadBlood leveraged phishing lures related to Israeli nuclear weapon capabilities despatched from a faux Gmail account purporting to belong to Daniel Zajfman, an Israeli physicist and president of the Weizmann Institute of Science. According to DeGrippo, it is common for TA453 to use political lures, which includes types about nuclear proliferation, even when targeting unrelated sectors. The lure e-mails joined to a spoofed Microsoft OneDrive web page, which then collected login details.
Proofpoint connected the campaign to TA453 as a result of the use of consistent infrastructure and very similar lures. The seller does not independently attribute the group to Iran, although the report notes that the United States and several market teams, such as Microsoft, have manufactured the relationship in the past.
“TA453 routinely tries to get the email qualifications of people today that could possess information aligned with the [Islamic Revolutionary Guard’s] selection priorities,” claimed DeGrippo.
According to the report, the BadBlood name was preferred “based on the healthcare concentration and ongoing geopolitical tensions amongst Iran and Israel.”
Some elements of this write-up are sourced from:
www.scmagazine.com

 Decided to move on from your NGAV/EDR? A Guide for Small Security Teams to What’s Next
Decided to move on from your NGAV/EDR? A Guide for Small Security Teams to What’s Next