The Iranian condition-sponsored menace actor regarded as MuddyWater has been attributed to a new swarm of attacks focusing on Turkey and the Arabian Peninsula with the purpose of deploying remote accessibility trojans (RATs) on compromised systems.
“The MuddyWater supergroup is hugely enthusiastic and can use unauthorized entry to perform espionage, mental home theft, and deploy ransomware and damaging malware in an enterprise,” Cisco Talos researchers Asheer Malhotra, Vitor Ventura, and Arnaud Zobec explained in a report published now.
The group, which has been lively considering that at least 2017, is recognized for its attacks on numerous sectors that support additional advance Iran’s geopolitical and national security goals. In January 2022, the U.S. Cyber Command attributed the actor to the country’s Ministry of Intelligence and Security (MOIS).

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

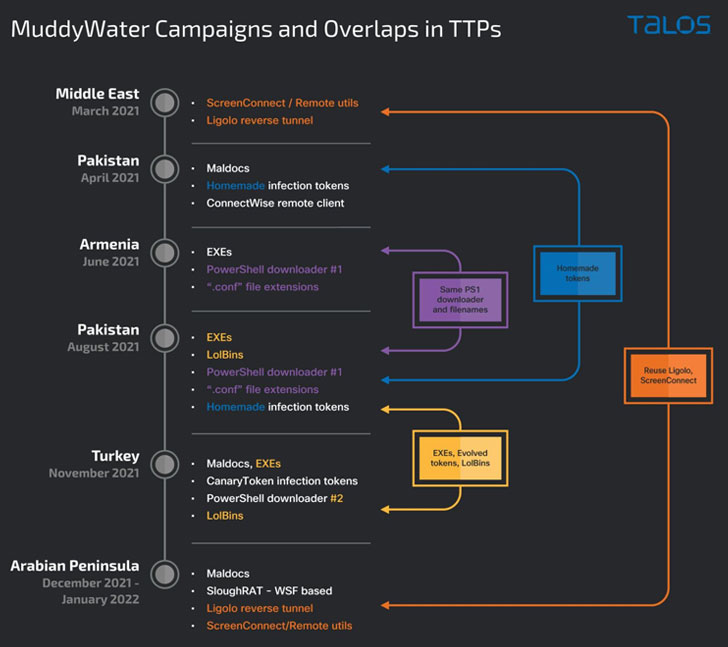
MuddyWater is also believed to be a “conglomerate of many groups operating independently alternatively than a one risk actor team,” the cybersecurity business extra, making it an umbrella actor in the vein of Winnti, a China-based mostly highly developed persistent menace (APT).
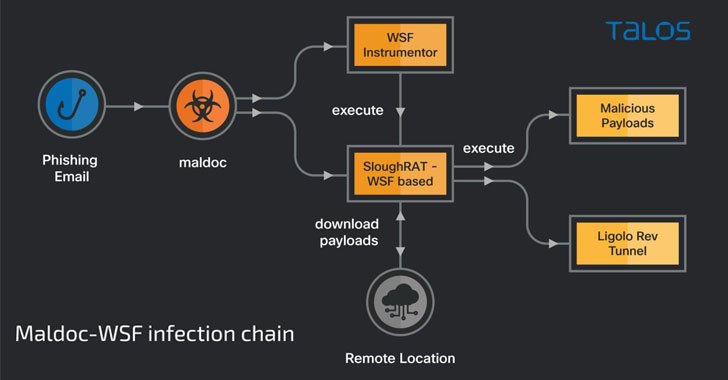
The latest strategies carried out by the hacking crew entail the use of malware-laced files delivered by way of phishing messages to deploy a distant accessibility trojan named SloughRAT (aka Canopy by CISA) capable of executing arbitrary code and instructions obtained from its command-and-command (C2) servers.
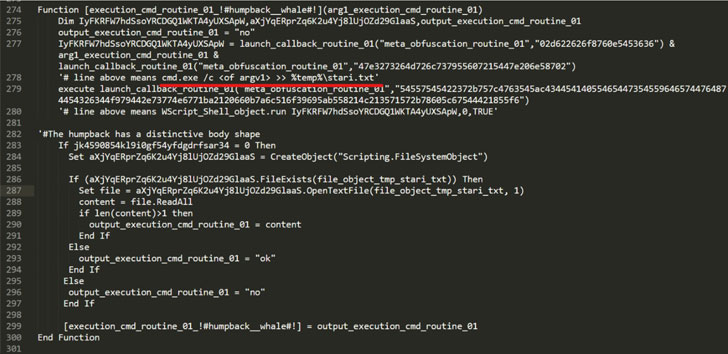
The maldoc, an Excel file made up of a destructive macro, triggers the an infection chain to drop two Windows Script Files (.WSF) on the endpoint, the 1st just one of them performing as the instrumentor to invoke and execute the next-phase payload.
Also found are two supplemental script-based mostly implants, one written in Visual Standard and the other coded in JavaScript, each of which are engineered to down load and run malicious commands on the compromised host.
On top of that, the most current set of intrusions marks a continuation of a November 2021 campaign that struck Turkish non-public companies and governmental institutions with PowerShell-primarily based backdoors to get data from its victims, even as it reveals overlaps with yet another marketing campaign that took area in March 2021.
The commonalities in methods and techniques adopted by the operators have lifted the probability that these attacks are “distinctive, yet similar, clusters of action,” with the campaigns leveraging a “broader TTP-sharing paradigm, standard of coordinated operational teams,” the researchers famous.
A next phishing attack sequence among December 2021 and January 2022 concerned the deployment of VBS-centered malicious downloaders applying scheduled duties created by the adversary, enabling the execution of payloads retrieved from a distant server. The benefits of the command are subsequently exfiltrated back again to the C2 server.
“Even though they share sure strategies, these strategies also denote individuality in the way they had been done, indicating the existence of numerous sub-teams beneath the Muddywater umbrella — all sharing a pool of practices and instruments to choose and opt for from,” the researchers concluded.
Discovered this report fascinating? Observe THN on Fb, Twitter and LinkedIn to read through extra exceptional written content we write-up.
Some areas of this article are sourced from:
thehackernews.com


 Best paying tech jobs of 2022
Best paying tech jobs of 2022