An sophisticated persistent threat group with inbound links to Iran has up to date its malware toolset to incorporate a novel PowerShell-centered implant named PowerLess Backdoor, in accordance to new analysis published by Cybereason.
The Boston-headquartered cybersecurity organization attributed the malware to a hacking group identified as Charming Kitten (aka Phosphorous, APT35, or TA453), while also contacting out the backdoor’s evasive PowerShell execution.
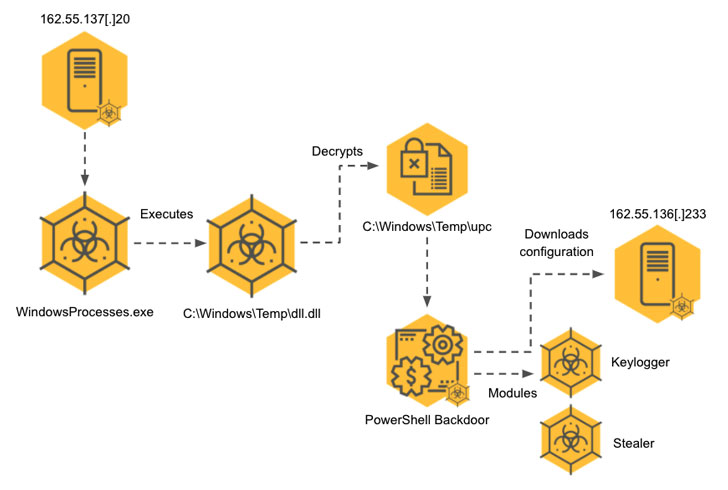
“The PowerShell code operates in the context of a .NET software, so not launching ‘powershell.exe’ which allows it to evade security products and solutions,” Daniel Frank, senior malware researcher at Cybereason, stated. “The toolset analyzed includes really modular, multi-staged malware that decrypts and deploys added payloads in a number of stages for the sake of equally stealth and efficacy.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The threat actor, which is active given that at least 2017, has been powering a collection of campaigns in current decades, which include individuals wherein the adversary posed as journalists and students to deceive targets into setting up malware and stealing categorised info.
Previously this month, Verify Place Exploration disclosed specifics of an espionage operation that concerned the hacking team exploiting the Log4Shell vulnerabilities to deploy a modular backdoor dubbed CharmPower for abide by-on attacks.
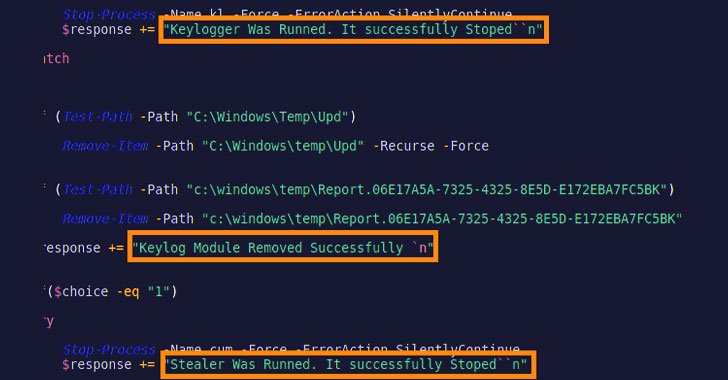
The most up-to-date refinements to its arsenal, as spotted by Cybereason, constitutes an completely new toolset that encompasses the PowerLess Backdoor, which is able of downloading and executing added modules this sort of as a browser information-stealer and a keylogger.
Also possibly connected to the similar developer of the backdoor are a amount of other malware artifacts, counting an audio recorder, an before variant of the data stealer, and what the researchers suspect to be an unfinished ransomware variant coded in .NET.
Also, infrastructure overlaps have been discovered among the Phosphorus team and a new ransomware pressure known as Memento, which initially emerged in November 2021 and took the unusual step of locking files inside password-shielded archives, followed by encrypting the password and deleting the initial information, following their makes an attempt to encrypt the files specifically have been blocked by endpoint defense.
“The action of Phosphorus with regard to ProxyShell took position in about the identical time body as Memento,” Frank explained. “Iranian danger actors were also noted to be turning to ransomware for the duration of that interval, which strengthens the hypothesis that Memento is operated by an Iranian threat actor.”
Identified this report fascinating? Abide by THN on Fb, Twitter and LinkedIn to go through more exclusive information we submit.
Some pieces of this short article are sourced from:
thehackernews.com


 FBI: Olympic Athletes Should Leave Devices at Home
FBI: Olympic Athletes Should Leave Devices at Home