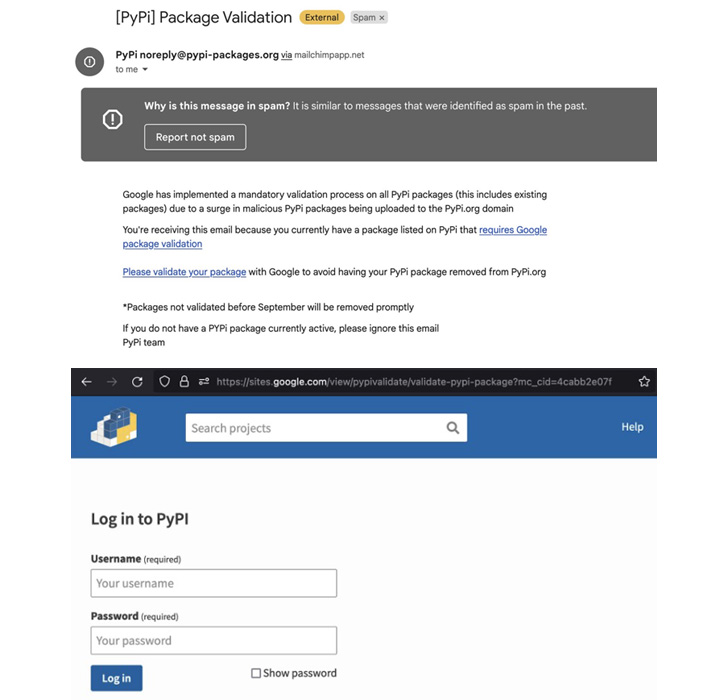
More specifics have emerged about the operators guiding the first-known phishing campaign especially aimed at the Python Package deal Index (PyPI), the formal third-party application repository for the programming language.
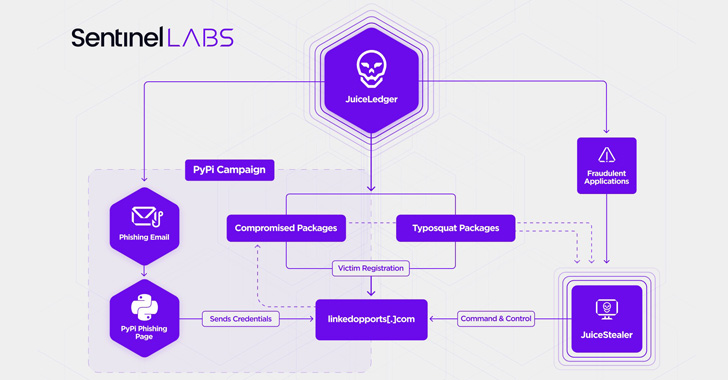
Connecting it to a threat actor tracked as JuiceLedger, cybersecurity agency SentinelOne, alongside with Checkmarx, explained the group as a rather new entity that surfaced in early 2022.
First “small-key” campaigns are mentioned to have concerned the use of rogue Python installer programs to provide a .NET-based mostly malware called JuiceStealer that is engineered to siphon passwords and other delicate data from victims’ web browsers.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The attacks acquired a considerable facelift very last thirty day period when the JuiceLedger actors targeted PyPi bundle contributors in a phishing campaign, ensuing in the compromise of a few deals with malware.
“The supply chain attack on PyPI package contributors appears to be an escalation of a marketing campaign started before in the year which in the beginning targeted prospective victims by bogus cryptocurrency buying and selling programs,” SentinelOne researcher Amitai Ben Shushan Ehrlich said in a report.
The goal is presumably to infect a broader audience with the infostealer by a blend of trojanized and typosquat deals, the cybersecurity company included.

The growth adds to expanding concerns encompassing the security of the open up supply ecosystem, prompting Google to just take measures to announce financial benefits for finding flaws in its tasks offered in the public area.
With account takeover attacks getting a common an infection vector for attackers on the lookout to poison software program provide chains, PyPI has started imposing a obligatory two-factor authentication (2FA) requirement for jobs deemed “critical.”
“JuiceLedger seems to have advanced quite swiftly from opportunistic, little-scale bacterial infections only a couple of months ago to conducting a provide chain attack on a significant software distributor,” SentinelOne stated.
Uncovered this short article fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to browse more distinctive articles we publish.
Some parts of this short article are sourced from:
thehackernews.com

 The Ultimate Security Blind Spot You Don’t Know You Have
The Ultimate Security Blind Spot You Don’t Know You Have