The danger actors guiding the LockBit ransomware-as-a-services (RaaS) scheme have extorted $91 million next hundreds of attacks from numerous U.S. businesses considering the fact that 2020.
Which is according to a joint bulletin published by the U.S. Cybersecurity and Infrastructure Security Company (CISA), Federal Bureau of Investigation (FBI), the Multi-Point out Information Sharing and Analysis Heart (MS-ISAC), and other partner authorities from Australia, Canada, France, Germany, New Zealand, and the U.K.
“The LockBit ransomware-as-a-service (RaaS) attracts affiliate marketers to use LockBit for conducting ransomware attacks, ensuing in a big web of unconnected threat actors conducting wildly various attacks,” the businesses stated.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
LockBit, which initial burst on to the scene in late 2019, has continued to be disruptive and prolific, focusing on as lots of as 76 victims in May well 2023 alone, for every studies shared by Malwarebytes last week. The Russia-linked cartel has claimed accountability for at the very least 1,653 ransomware attacks to day.

The cybercrime operation has attacked a wide array of critical infrastructure sectors, such as financial solutions, food items and agriculture, education, electrical power, authorities and unexpected emergency expert services, health care, manufacturing, and transportation.
LockBit has gained three sizeable upgrades so significantly: LockBit Crimson (June 2021), LockBit Black (March 2022), and LockBit Inexperienced (January 2023), the last of which is based on leaked resource code from the now-disbanded Conti gang.
The ransomware strain has due to the fact been adapted to goal Linux, VMware ESXi, and Apple macOS methods, reworking it into an ever-evolving menace. The RaaS operation is also notable for paying people today to get tattoos of its insignia and instituting the initial-at any time bug bounty system.
The business enterprise model consists of the main builders leasing out their warez to affiliate marketers who carry out the genuine ransomware deployment and extortion. But in a twist, the group enables the affiliates to acquire ransom payments ahead of sending a slash to the key crew.
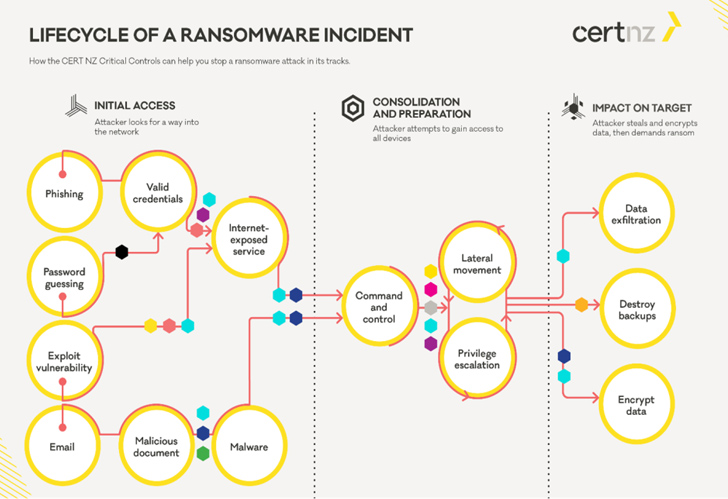
Attack chains involving LockBit have leveraged a short while ago disclosed flaws in Fortra GoAnywhere Managed File Transfer (MFT) and PaperCut MF/NG servers as nicely as other known bugs in Apache Log4j2, F5 Large-IP and Significant-IQ, and Fortinet gadgets to obtain original obtain.
Also employed by the affiliate marketers are around three dozen freeware and open-resource applications that make it possible for for network reconnaissance, remote accessibility and tunneling, credential dumping, and file exfiltration. The intrusions have been discovered to more abuse authentic purple group application this kind of as Metasploit and Cobalt Strike.
“LockBit has been prosperous by way of its innovation and continual improvement of the group’s administrative panel (i.e., a simplified, position-and-click on interface making ransomware deployment accessible to all those with decrease degrees of complex ability), affiliate supporting features, and continuous revision of TTPs,” the businesses explained.
Future WEBINAR🔐 Mastering API Security: Knowing Your Accurate Attack Surface
Uncover the untapped vulnerabilities in your API ecosystem and choose proactive measures in the direction of ironclad security. Sign up for our insightful webinar!
Sign up for the Session.wn-button,.wn-label,.wn-label:immediately afterscreen:inline-block.check out_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px sound #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-proper-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-measurement:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.wn-label:right afterwidth:50pxheight:6pxcontent:”border-best:2px strong #d9deffmargin: 8px.wn-titlefont-dimensions:21pxpadding:10px 0font-body weight:900textual content-align:leftline-height:33px.wn-descriptiontextual content-align:leftfont-dimension:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-sizing:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
The improvement will come as CISA issued a Binding Operational Directive 23-02, instructing federal companies to secure network gadgets like firewalls, routers, and switches that are uncovered to the general public internet in just 14 times of discovery and take methods to minimize the attack area.
“As well normally, risk actors are capable to use network products to gain unrestricted obtain to organizational networks, in change main to total-scale compromise,” CISA Director, Jen Easterly, stated. “Demanding appropriate controls and mitigations […] is an significant stage in minimizing risk to the federal civilian business.”
The advisories also stick to a new advisory highlighting threats to Baseboard Management Controller (BMC) implementations that could possibly help risk actors to establish a “beachhead with pre-boot execution probable.”
“Hardened qualifications, firmware updates, and network segmentation solutions are often disregarded, primary to a susceptible BMC,” CISA and the U.S. National Security Agency (NSA) famous in a joint warn.
“On top of that, a malicious actor could disable security methods such as the trustworthy platform module (TPM) or UEFI secure boot, manipulate data on any hooked up storage media, or propagate implants or disruptive instructions across a network infrastructure.”
Located this posting fascinating? Abide by us on Twitter and LinkedIn to browse much more special articles we submit.
Some components of this article are sourced from:
thehackernews.com


 Chinese Hackers Exploit VMware Zero-Day to Backdoor Windows and Linux Systems
Chinese Hackers Exploit VMware Zero-Day to Backdoor Windows and Linux Systems