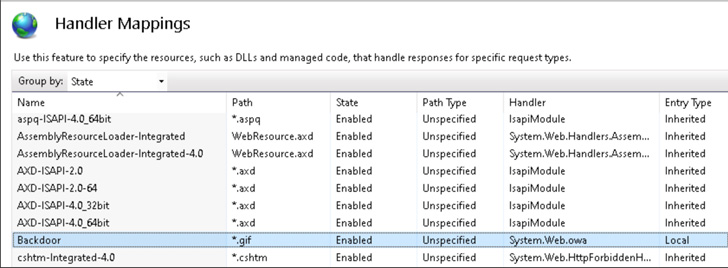
Risk actors are significantly abusing Internet Details Services (IIS) extensions to backdoor servers as a means of establishing a “long lasting persistence mechanism.”
That is according to a new warning from the Microsoft 365 Defender Investigation Team, which explained that “IIS backdoors are also more difficult to detect due to the fact they typically reside in the exact directories as legitimate modules made use of by goal apps, and they abide by the similar code composition as clean up modules.”
Attack chains taking this strategy begin with weaponizing a critical vulnerability in the hosted software for preliminary access, utilizing this foothold to drop a script web shell as the 1st stage payload.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

This web shell then gets the conduit for putting in a rogue IIS module to give remarkably covert and persistent accessibility to the server, in addition to monitoring incoming and outgoing requests as well as jogging remote commands.
Without a doubt, before this month, Kaspersky researchers disclosed a marketing campaign undertaken by the Gelsemium team, which was located having gain of the ProxyLogon Exchange Server flaws to start a piece of IIS malware named SessionManager.
In another established of attacks noticed by the tech big among January and Could 2022, Trade servers were being qualified with web shells by suggests of an exploit for the ProxyShell flaws, which ultimately led to the deployment of a backdoor identified as “FinanceSvcModel.dll” but not before a time period of reconnaissance.

“The backdoor experienced designed-in ability to execute Trade management functions, these kinds of as enumerating put in mailbox accounts and exporting mailboxes for exfiltration,” security researcher Hardik Suri stated.
To mitigate these attacks, it really is recommended to implement the hottest security updates for server elements as shortly as feasible, maintain antivirus and other protections enabled, evaluate delicate roles and groups, and prohibit access by practicing the theory of minimum-privilege and keeping great credential hygiene.
Identified this post intriguing? Abide by THN on Fb, Twitter and LinkedIn to read a lot more exceptional content material we article.
Some components of this short article are sourced from:
thehackernews.com


 Novel Malware Hijacks Facebook Business Accounts
Novel Malware Hijacks Facebook Business Accounts