Microsoft has shared aspects of a now-patched flaw in Apple macOS that could be abused by menace actors with root accessibility to bypass security enforcements and complete arbitrary steps on influenced equipment.
Especially, the flaw – dubbed Migraine and tracked as CVE-2023-32369 – could be abused to get all-around a essential security evaluate called Method Integrity Protection (SIP), or “rootless,” which limitations the steps the root person can conduct on safeguarded information and folders.
“The most straight-forward implication of a SIP bypass is that […] an attacker can build files that are protected by SIP and consequently undeletable by common suggests,” Microsoft scientists Jonathan Bar Or, Michael Pearse, and Anurag Bohra said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Even even worse, it could be exploited to obtain arbitrary kernel code execution and even accessibility delicate information by replacing databases that regulate Transparency, Consent, and Management (TCC) insurance policies.
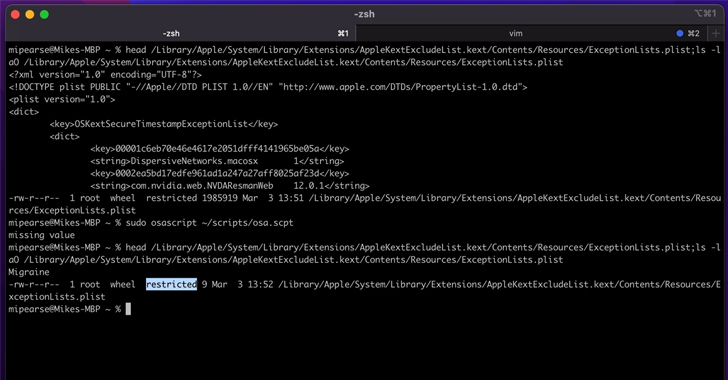
The bypass is made feasible by leveraging a designed-in macOS device termed Migration Assistant to activate the migration method by way of an AppleScript which is created to ultimately launch an arbitrary payload.
This, in transform, stems from the point that systemmigrationd – the daemon utilized to handle machine transfer – will come with the com.apple.rootless.put in.heritable entitlement, making it possible for all its little one procedures, like bash and perl, to bypass SIP checks.
As a outcome, a menace actor already with code execution abilities as root could trigger systemmigrationd to operate perl, which could then be used to run a destructive shell script as the migration course of action is underway.
Following liable disclosure, the vulnerability was resolved by Apple as portion of updates (macOS Ventura 13.4, macOS Monterey 12.6.6, and macOS Huge Sur 11.7.7) delivered on May possibly 18, 2023.
The iPhone maker described CVE-2023-32369 as a logic issue that could enable a malicious app to modify secured areas of the file system.
Migraine is the most up-to-date addition to the checklist of macOS security bypasses that have been documented underneath the names Shrootless (CVE-2021-30892, CVSS rating: 5.5), powerdir (CVE-2021-30970, CVSS rating: 5.5), and Achilles (CVE-2022-42821, CVSS score: 5.5).
Forthcoming WEBINAR Zero Rely on + Deception: Learn How to Outsmart Attackers!
Learn how Deception can detect sophisticated threats, prevent lateral motion, and increase your Zero Believe in system. Sign up for our insightful webinar!
Conserve My Seat!.ad-button,.advertisement-label,.ad-label:followingexhibit:inline-block.advert_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px solid #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-leading-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-measurement:13pxmargin:20px 0font-weight:600letter-spacing:.6pxcolor:#596cec.advert-label:soon afterwidth:50pxheight:6pxcontent:”border-prime:2px strong #d9deffmargin: 8px.advert-titlefont-dimension:21pxpadding:10px 0font-fat:900textual content-align:leftline-top:33px.advert-descriptiontextual content-align:leftfont-size:15.6pxline-top:26pxmargin:5px !importantcolor:#4e6a8d.advert-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-size:15pxcolor:#fff!importantborder:0line-peak:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
“The implications of arbitrary SIP bypasses are really serious, as the prospective for malware authors is considerable,” the researchers stated.
“Bypassing SIP could direct to significant consequences, these as increasing the possible for attackers and malware authors to productively put in rootkits, develop persistent malware, and broaden the attack surface for supplemental techniques and exploits.”
The findings appear as Jamf Threat Labs disclosed facts of a sort confusion flaw in the macOS kernel that could be weaponized by a rogue app set up on the gadget to execute arbitrary code with kernel privileges.
Labeled ColdInvite (aka CVE-2023-27930), the flaw “can be exploited to leverage the co-processor in purchase to attain go through/create privileges to the kernel, allowing for a undesirable actor to get closer to noticing their best objective of totally compromising the gadget.”
Observed this article exciting? Adhere to us on Twitter and LinkedIn to examine extra exceptional content we article.
Some parts of this write-up are sourced from:
thehackernews.com

 6 Steps to Effectively Threat Hunting: Safeguard Critical Assets and Fight Cybercrime
6 Steps to Effectively Threat Hunting: Safeguard Critical Assets and Fight Cybercrime