Microsoft on Friday disclosed a prospective relationship involving the Raspberry Robin USB-centered worm and an notorious Russian cybercrime team tracked as Evil Corp.
The tech large claimed it noticed the FakeUpdates (aka SocGholish) malware remaining shipped through existing Raspberry Robin infections on July 26, 2022.
Raspberry Robin, also referred to as QNAP Worm, is recognised to spread from a compromised program via contaminated USB products that contains destructive a .LNK files to other gadgets in the goal network.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The marketing campaign, which was first noticed by Pink Canary in September 2021, has been elusive in that no later-stage activity has been documented nor has there any concrete backlink tying it to a recognized risk actor or team.
The disclosure marks the initially evidence of put up-exploitation actions carried out by the danger actor upon leveraging the malware to acquire initial obtain to a Windows machine.
“The DEV-0206-associated FakeUpdates activity on influenced units has considering the fact that led to stick to-on actions resembling DEV-0243 pre-ransomware habits,” Microsoft mentioned.
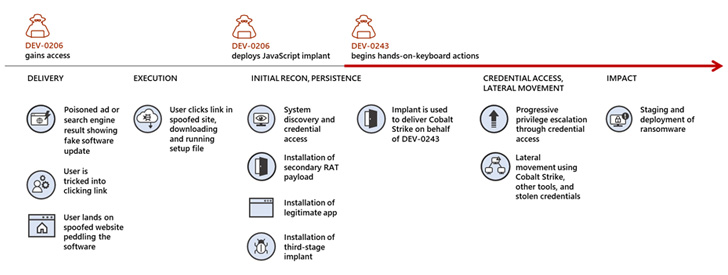
DEV-0206 is Redmond’s moniker for an first accessibility broker that deploys a malicious JavaScript framework named FakeUpdates by enticing targets into downloading pretend browser updates.
The malware, at its main, acts as a conduit for other campaigns that make use of this obtain acquired from DEV-0206 to distribute other payloads, mostly Cobalt Strike loaders attributed to DEV-0243, which is also recognized as Evil Corp.
Also named Gold Drake and Indrik Spider, the financially enthusiastic hacking team has traditionally operated the Dridex malware and has considering that switched to deploying a string of ransomware family members over the many years, including most recently LockBit.

“The use of a RaaS payload by the ‘EvilCorp’ exercise team is probably an attempt by DEV-0243 to stay clear of attribution to their team, which could discourage payment owing to their sanctioned position,” Microsoft mentioned.
It is not immediately apparent what precise connections Evil Corp, DEV-0206, and DEV-0243 might have with 1 a further.
Katie Nickels, director of intelligence at Purple Canary, claimed in a statement shared with The Hacker News that the conclusions, if proven to be correct, fills a “big gap” with Raspberry Robin’s modus operandi.
“We continue to see Raspberry Robin action, but we have not been capable to affiliate it with any distinct man or woman, enterprise, entity, or state,” Nickels stated.
“Eventually, it is too early to say if Evil Corp is liable for, or associated with, Raspberry Robin. The Ransomware-as-a-Company (RaaS) ecosystem is a intricate one, wherever various prison teams companion with one an additional to reach a range of targets. As a end result, it can be complicated to untangle the interactions amongst malware families and observed action.”
Uncovered this short article exciting? Abide by THN on Fb, Twitter and LinkedIn to read much more exclusive content material we submit.
Some components of this short article are sourced from:
thehackernews.com


 Ransomware: Sometimes you need to pay to make it go away
Ransomware: Sometimes you need to pay to make it go away