Microsoft has shared specialized facts about a now-fastened, actively exploited critical security vulnerability affecting SolarWinds Serv-U managed file transfer support that it has attributed with “high assurance” to a danger actor functioning out of China.
In mid-July, the Texas-centered firm remedied a distant code execution flaw (CVE-2021-35211) that was rooted in Serv-U’s implementation of the Protected Shell (SSH) protocol, which could be abused by attackers to operate arbitrary code on the contaminated technique, such as the skill to install destructive plans and check out, modify, or delete delicate data.
“The Serv-U SSH server is subject to a pre-auth distant code execution vulnerability that can be conveniently and reliably exploited in the default configuration,” Microsoft Offensive Analysis and Security Engineering workforce claimed in a detailed compose-up describing the exploit.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“An attacker can exploit this vulnerability by connecting to the open up SSH port and sending a malformed pre-auth link ask for. When successfully exploited, the vulnerability could then enable the attacker to set up or run plans, this sort of as in the case of the qualified attack we formerly documented,” the researchers added.
Though Microsoft connected the attacks to DEV-0322, a China-dependent collective citing “observed victimology, ways, and techniques,” the firm has now exposed that the distant, pre-auth vulnerability stemmed from the fashion the Serv-U procedure managed entry violations with out terminating the system, thereby generating it straightforward to pull off stealthy, dependable exploitation tries.
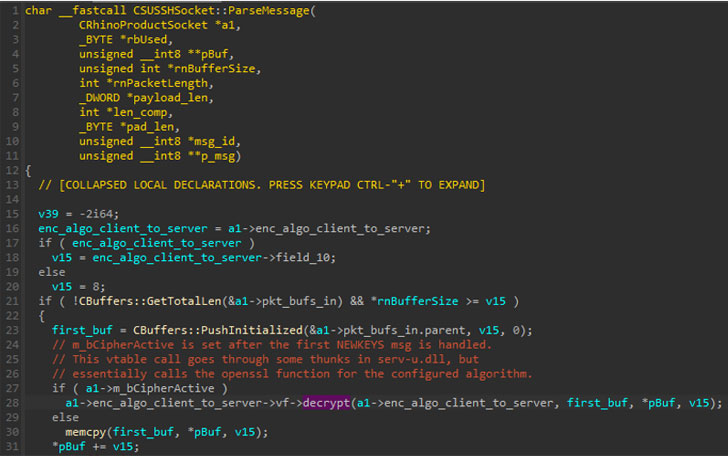
“The exploited vulnerability was triggered by the way Serv-U to begin with developed an OpenSSL AES128-CTR context,” the scientists explained. “This, in switch, could let the use of uninitialized information as a function pointer in the course of the decryption of successive SSH messages.”
“Consequently, an attacker could exploit this vulnerability by connecting to the open SSH port and sending a malformed pre-auth connection ask for. We also found that the attackers ended up most likely using DLLs compiled without the need of address room layout randomization (ASLR) loaded by the Serv-U course of action to aid exploitation,” the scientists added.
ASLR refers to a protection mechanism that is made use of to enhance the issue of executing a buffer overflow attack by randomly arranging the handle room positions where by process executables are loaded into memory.
Microsoft, which disclosed the attack to SolarWinds, said it advised enabling ASLR compatibility for all binaries loaded in the Serv-U procedure. “ASLR is a critical security mitigation for expert services which are uncovered to untrusted distant inputs, and demands that all binaries in the approach are appropriate in purchase to be effective at avoiding attackers from using hardcoded addresses in their exploits, as was achievable in Serv-U,” the scientists explained.
If just about anything, the revelations highlight the variety of strategies and resources applied by risk actors to breach corporate networks, which include piggybacking on legit software program.
Again in December 2020, Microsoft disclosed that a different espionage group may perhaps have been using gain of the IT infrastructure provider’s Orion software package to fall a persistent backdoor called Supernova on contaminated devices. Cybersecurity organization Secureworks linked the intrusions to a China-linked risk actor named Spiral.
Uncovered this article exciting? Comply with THN on Fb, Twitter and LinkedIn to read far more exceptional articles we publish.
Some parts of this short article are sourced from:
thehackernews.com


 U.S. Cyber Command Warns of Ongoing Attacks Exploiting Atlassian Confluence Flaw
U.S. Cyber Command Warns of Ongoing Attacks Exploiting Atlassian Confluence Flaw