Microsoft has revised its mitigation actions for the recently disclosed and actively exploited zero-working day flaws in Trade Server soon after it was located that they could be trivially bypassed.
The two vulnerabilities, tracked as CVE-2022-41040 and CVE-2022-41082, have been codenamed ProxyNotShell thanks to similarities to an additional established of flaws identified as ProxyShell, which the tech giant resolved past calendar year.
In-the-wild attacks abusing the shortcomings have chained the two flaws to attain remote code execution on compromised servers with elevated privileges, leading to the deployment of web shells.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The Windows maker, which is yet to release a deal with for the bugs, has acknowledged that a solitary condition-sponsored danger actor could have been weaponizing the flaws considering that August 2022 in minimal focused attacks.

To minimize the risk of exploitation, the business also shared short term workarounds that are built to limit recognized attack styles by a rule in the IIS Supervisor.
Having said that, according to security researcher Jang (@testanull), the URL sample can be quickly circumvented, with senior vulnerability analyst Will Dormann noting that the block mitigations are “unnecessarily exact, and therefore inadequate.”
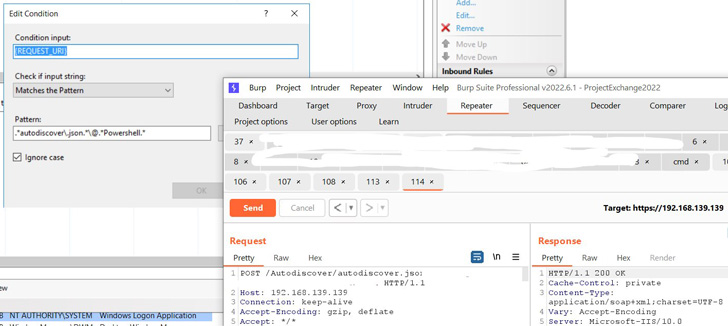
Microsoft has because revised the URL Rewrite rule (also offered as a standalone PowerShell script) to consider this into account –
- Open IIS Supervisor
- Pick Default Web Web site
- In the Attribute Check out, click URL Rewrite
- In the Steps pane on the ideal-hand side, click on Insert Rule(s)…
- Choose Request Blocking and simply click Alright
- Include the string “.*autodiscover.json.*Powershell.*” (excluding offers)
- Pick out Normal Expression underneath Making use of
- Select Abort Ask for below How to block and then click on Alright
- Develop the rule and find the rule with the sample: .*autodiscover.json.*Powershell.* and click Edit under Conditions
- Change the Problem input from URL to Request_URI
It’s not instantly apparent when Microsoft plans to press a patch for the two vulnerabilities, but it truly is achievable that they could be transported as section of Patch Tuesday updates subsequent 7 days on Oct 11, 2022.
Uncovered this report fascinating? Stick to THN on Fb, Twitter and LinkedIn to browse additional exclusive content material we write-up.
Some pieces of this posting are sourced from:
thehackernews.com


 Russian Hacker Arrested in India for Reportedly Helping Students Cheat in JEE-Main Exam
Russian Hacker Arrested in India for Reportedly Helping Students Cheat in JEE-Main Exam