Many vulnerabilities have been disclosed in Checkmk IT Infrastructure monitoring software that could be chained collectively by an unauthenticated, distant attacker to totally choose in excess of affected servers.
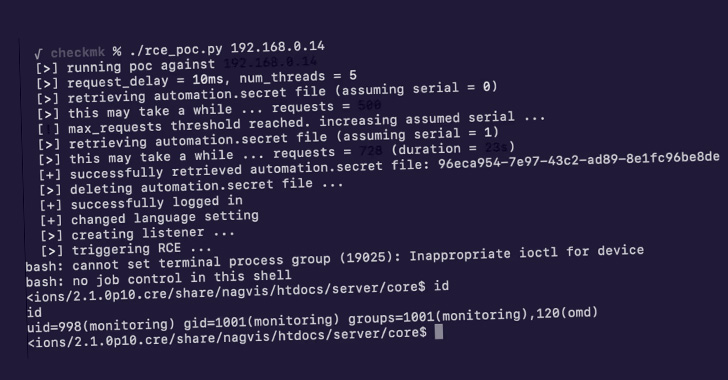
“These vulnerabilities can be chained collectively by an unauthenticated, distant attacker to acquire code execution on the server operating Checkmk variation 2.1.0p10 and lessen,” SonarSource researcher Stefan Schiller said in a specialized examination.
Checkmk’s open up resource edition of the checking resource is based on Nagios Main and offers integrations with NagVis for the visualization and generation of topological maps of infrastructures, servers, ports, and processes.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
According to its Munich-primarily based developer tribe29 GmbH, its Business and Uncooked editions are used by around 2,000 customers, together with Airbus, Adobe, NASA, Siemens, Vodafone, and many others.
The four vulnerabilities, which consist of two Critical and two Medium severity bugs, are as follows –
- A code injection flaw in watolib’s auth.php (CVSS rating: 9.1)
- An arbitrary file browse flaw in NagVis (CVSS score: 9.1)
- A command injection flaw Checkmk’s Livestatus wrapper and Python API (CVSS score: 6.8), and
- A server-aspect ask for forgery (SSRF) flaw in the host registration API (CVSS score: 5.)
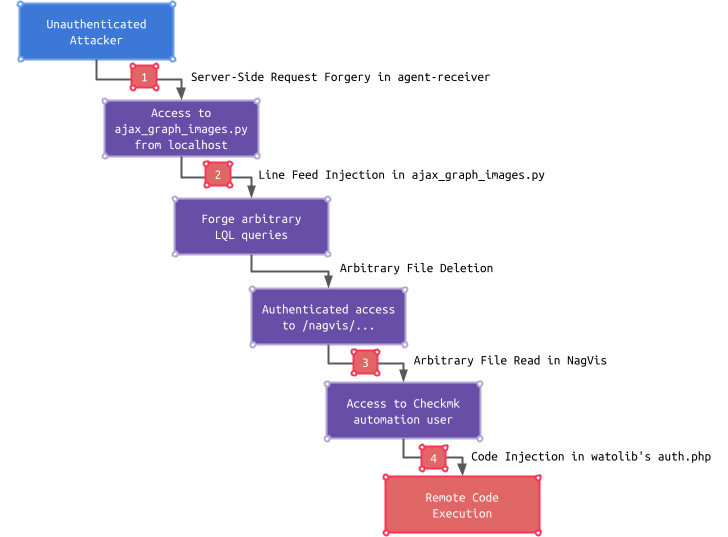
Though these shortcomings on their very own have a constrained effect, an adversary can chain the issues, commencing with the SSRF flaw to access an endpoint only reachable from localhost, using it to bypass authentication and read through a configuration file, ultimately gaining entry to the Checkmk GUI.

“This entry can even more be turned into remote code execution by exploiting a Code Injection vulnerability in a Checkmk GUI subcomponent identified as watolib, which generates a file named auth.php needed for the NagVis integration,” Schiller described.
Subsequent dependable disclosure on August 22, 2022, the 4 vulnerabilities have been patched in Checkmk version 2.1.0p12 introduced on September 15, 2022.
The findings stick to the discovery of many flaws in other checking methods like Zabbix and Icinga considering the fact that the begin of the year, which could have been exploited to compromise the servers by running arbitrary code.
Found this write-up appealing? Follow THN on Fb, Twitter and LinkedIn to read a lot more distinctive material we put up.
Some components of this short article are sourced from:
thehackernews.com

 These Android Apps with a Million Play Store Installations Redirect Users to Malicious Sites
These Android Apps with a Million Play Store Installations Redirect Users to Malicious Sites