Telecommunications and IT company providers in the Middle East and Asia are currently being specific by a beforehand undocumented Chinese-talking menace team dubbed WIP19.
The espionage-relevant attacks are characterised by the use of a stolen electronic certification issued by a Korean company termed DEEPSoft to indication malicious artifacts deployed throughout the an infection chain to evade detection.
“Practically all operations executed by the threat actor had been done in a ‘hands-on keyboard’ vogue, throughout an interactive session with compromised devices,” SentinelOne researchers Joey Chen and Amitai Ben Shushan Ehrlich stated in a report this 7 days.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“This intended the attacker gave up on a steady [command-and-control] channel in exchange for stealth.”
WIP, quick for work-in-development, is the moniker assigned by SentinelOne to emerging or hitherto unattributed action clusters, similar to the UNC####, DEV-####, and TAG-## designations given by Mandiant, Microsoft, and Recorded Potential.
The cybersecurity firm also pointed out that find portions of the destructive factors employed by WIP19 had been authored by a Chinese-talking malware creator dubbed WinEggDrop, who has been lively considering the fact that 2014.
WIP19 is said to share inbound links to a further team codenamed Operation Shadow Pressure owing to overlaps in the use of WinEggDrop-authored malware, stolen certificates, and tactical overlaps.
That said, SentinelOne pointed out, “it is unclear no matter whether this is a new iteration of procedure ‘Shadow Force’ or only a distinctive actor employing comparable TTPs.”
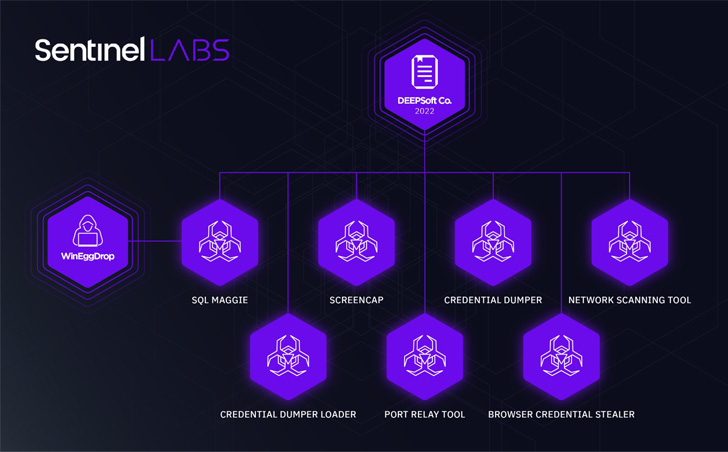
Intrusions mounted by the adversarial collective rely on a bespoke toolset that consists of a mix of a credential dumper, network scanner, browser stealer, keystroke logger and display recorder (ScreenCap), and an implant known as SQLMaggie.
SQLMaggie was also the topic of an in-depth examination by German cybersecurity organization DCSO CyTec previously this month, contacting out its ability to break into Microsoft SQL servers and leverage the access to operate arbitrary instructions by means of SQL queries.

An evaluation of telemetry knowledge even further revealed the presence of SQLMaggie in 285 servers spread across 42 nations, mainly South Korea, India, Vietnam, China, Taiwan, Russia, Thailand, Germany, Iran, and the U.S.
The actuality that the attacks are precision targeted and minimal in volume, not to mention have singled out the telecom sector, indicates that the main motive at the rear of the campaign may perhaps be to gather intelligence.
The findings are but yet another indication of how China-aligned hacking groups are at as soon as sprawling and fluid owing to the reuse of the malware between a number of risk actors.
“WIP19 is an example of the larger breadth of Chinese espionage exercise experienced in critical infrastructure industries,” SentineOne researchers explained.
“The existence of responsible quartermasters and popular developers enables a landscape of hard-to-recognize danger groups that are making use of identical tooling, generating danger clusters tricky to distinguish from the defenders stage of check out.”
Identified this report intriguing? Adhere to THN on Fb, Twitter and LinkedIn to read much more special material we article.
Some elements of this article are sourced from:
thehackernews.com


 #DTX2022: How to Scam Someone Using Social Media Phishing
#DTX2022: How to Scam Someone Using Social Media Phishing