A menace actor presumed to be of Chinese origin has been joined to a series of 10 attacks concentrating on Mongolia, Russia, Belarus, Canada, and the U.S. from January to July 2021 that include the deployment of a remote obtain trojan (RAT) on contaminated methods, in accordance to new research.
The intrusions have been attributed to an innovative persistent risk named APT31 (FireEye), which is tracked by the cybersecurity local community beneath the monikers Zirconium (Microsoft), Judgement Panda (CrowdStrike), and Bronze Vinewood (Secureworks).


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The team is a “China-nexus cyber espionage actor concentrated on acquiring information that can deliver the Chinese governing administration and point out-owned enterprises with political, economic, and navy pros,” according to FireEye.
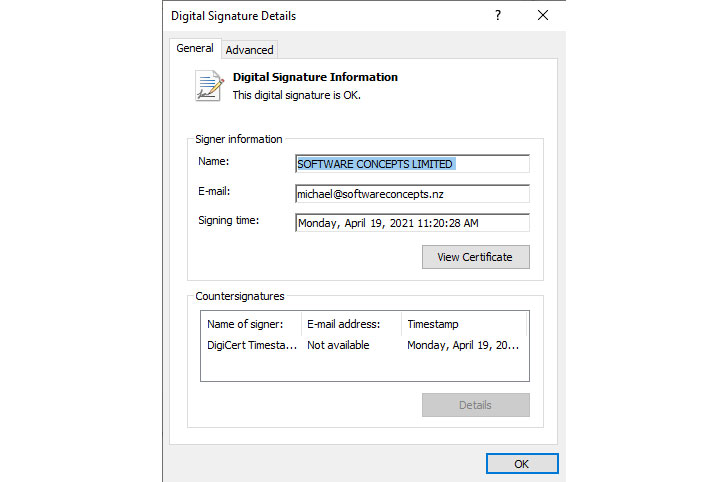
Favourable Systems, in a publish-up revealed Tuesday, uncovered a new malware dropper that was utilised to aid the attacks, such as the retrieval of subsequent-stage encrypted payloads from a distant command-and-handle server, which are subsequently decoded to execute the backdoor.
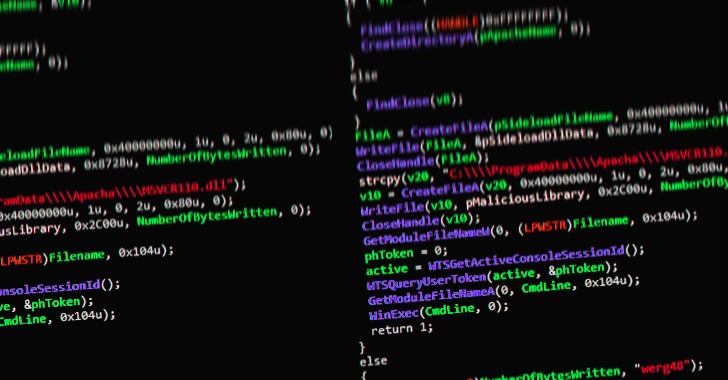
The malicious code comes with the capability to down load other malware, perhaps placing affected victims at more risk, as properly as accomplish file operations, exfiltrate delicate facts, and even delete by itself from the compromised machine.
“The code for processing the [self-delete] command is significantly intriguing: all the designed documents and registry keys are deleted applying a bat-file,” Positive Technologies researchers Denis Kuvshinov and Daniil Koloskov claimed.

Also deserving of particular notice is the malware’s similarities to that of a trojan named DropboxAES RAT that was set to use by the same risk group last 12 months and relied on Dropbox for its command-and-handle (C2) communications, with various overlaps observed in the tactics and mechanisms made use of to inject the attack code, achieve persistence, and the mechanism employed to delete the espionage resource.
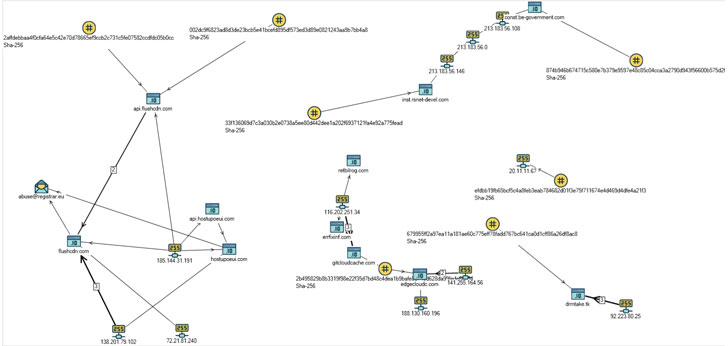
“The unveiled similarities with before variations of malicious samples described by scientists, this kind of as in 2020, propose that the team is increasing the geography of its pursuits to nations around the world wherever its expanding activity can be detected, Russia in particular,” the researchers concluded.
Located this posting intriguing? Comply with THN on Fb, Twitter and LinkedIn to study a lot more exceptional content material we article.
Some elements of this short article are sourced from:
thehackernews.com

 Google bundles Android and web authentication APIs under one banner
Google bundles Android and web authentication APIs under one banner