Ivanti, the firm behind Pulse Protected VPN appliances, has released a security advisory for a high severity vulnerability that could make it possible for an authenticated distant attacker to execute arbitrary code with elevated privileges.
“Buffer Overflow in Windows File Resource Profiles in 9.X lets a remote authenticated person with privileges to look through SMB shares to execute arbitrary code as the root consumer,” the company mentioned in an inform posted on May well 14. “As of version 9.1R3, this authorization is not enabled by default.”
The flaw, discovered as CVE-2021-22908, has a CVSS rating of 8.5 out of a greatest of 10 and impacts Pulse Link Safe variations 9.0Rx and 9.1Rx. In a report detailing the vulnerability, the CERT Coordination Center said the issue stems from the gateway’s capacity to link to Windows file shares through a variety of CGI endpoints that could be leveraged to carry out the attack.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“When specifying a very long server title for some SMB operations, the ‘smbclt’ application may perhaps crash thanks to either a stack buffer overflow or a heap buffer overflow, depending on how lengthy of a server name is specified,” CERT/CC comprehensive in a vulnerability observe revealed on Monday, including it was ready to induce the susceptible code by targeting the CGI script ‘/dana/fb/smb/wnf.cgi.’
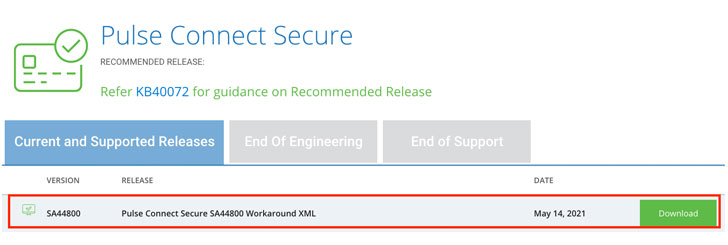
Pulse Protected shoppers are proposed to enhance to PCS Server variation 9.1R.11.5 when it becomes obtainable. In the interim, Ivanti has released a workaround file (‘Workaround-2105.xml’) that can be imported to disable the Windows File Share Browser element by including the susceptible URL endpoints to a blocklist and therefore activate essential mitigations to shield against this vulnerability.
It bears noting that consumers operating PCS versions 9.1R11.3 or down below would have to have to import a diverse file named ‘Workaround-2104.xml,’ necessitating that the PCS method is functioning 9.1R11.4 prior to implementing the safeguards in ‘Workaround-2105.xml.’
Though Ivanti has proposed turning off Windows File Browser on the Admin UI by disabling the possibility ‘Files, Window [sic]’ for specific user roles, CERT/CC uncovered the techniques were inadequate to secure in opposition to the flaw during its testing.
“The susceptible CGI endpoints are nonetheless reachable in methods that will trigger the ‘smbclt’ application to crash, irrespective of irrespective of whether the ‘Files, Windows’ person purpose is enabled or not,” it noted.
“An attacker would have to have a valid DSID and ‘xsauth’ worth from an authenticated person to efficiently get to the susceptible code on a PCS server that has an open up Windows File Access plan.”
The disclosure of a new flaw arrives months right after the Utah-based IT software firm patched a number of critical security vulnerabilities in Pulse Connect Secure products, which include CVE-2021-22893, CVE-2021-22894, CVE-2021-22899, and CVE-2021-22900, the 1st of which was uncovered to be actively exploited in the wild by at minimum two distinct menace actors.
Found this posting fascinating? Abide by THN on Fb, Twitter and LinkedIn to browse additional exclusive material we article.
Some parts of this article are sourced from:
thehackernews.com


 New Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
New Bluetooth Flaws Let Attackers Impersonate Legitimate Devices