A range of destructive samples have been created for the Windows Subsystem for Linux (WSL) with the objective of compromising Windows devices, highlighting a sneaky system that will allow the operators to stay below the radar and thwart detection by preferred anti-malware engines.
The “unique tradecraft” marks the to start with occasion exactly where a danger actor has been observed abusing WSL to install subsequent payloads.
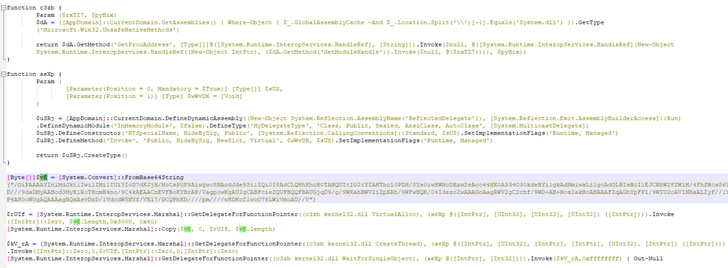
“These documents acted as loaders functioning a payload that was both embedded inside the sample or retrieved from a distant server and was then injected into a running method utilizing Windows API phone calls,” scientists from Lumen Black Lotus Labs claimed in a report revealed on Thursday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Windows Subsystem for Linux, introduced in August 2016, is a compatibility layer that’s built to operate Linux binary executables (in ELF format) natively on the Windows system without having the overhead of a conventional virtual machine or twin-boot set up.
The earliest artifacts date again to May well 3, 2021, with a collection of Linux binaries uploaded each and every two to three weeks until August 22, 2021. Not only are the samples created in Python 3 and transformed into an ELF executable with PyInstaller, but the files are also orchestrated to obtain shellcode from a remote command-and-control server and employ PowerShell to have out stick to-on pursuits on the infected host.
This secondary “shellcode” payload is then injected into a functioning Windows procedure working with Windows API calls for what Lumen explained as “ELF to Windows binary file execution,” but not ahead of the sample makes an attempt to terminate suspected antivirus goods and examination applications managing on the machine. What’s extra, the use of regular Python libraries tends to make some of the variants interoperable on the two Windows and Linux.
“Therefore considerably, we have identified a restricted range of samples with only one particular publicly routable IP handle, indicating that this activity is pretty minimal in scope or likely nonetheless in progress,” the researchers claimed. “As the the moment unique boundaries involving operating programs go on to grow to be much more nebulous, danger actors will just take benefit of new attack surfaces.”
Uncovered this post exciting? Stick to THN on Fb, Twitter and LinkedIn to study much more special content we post.
Some areas of this report are sourced from:
thehackernews.com


 Romance Scammers Make $133m in First Half of 2021
Romance Scammers Make $133m in First Half of 2021