A new information and facts-stealing malware named Mystic Stealer has been discovered to steal facts from about 40 different web browsers and about 70 web browser extensions.
Initially advertised on April 25, 2023, for $150 for each thirty day period, the malware also targets cryptocurrency wallets, Steam, and Telegram, and employs in depth mechanisms to resist analysis.
“The code is seriously obfuscated building use of polymorphic string obfuscation, hash-based import resolution, and runtime calculation of constants,” InQuest and Zscaler researchers stated in an examination posted final week.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
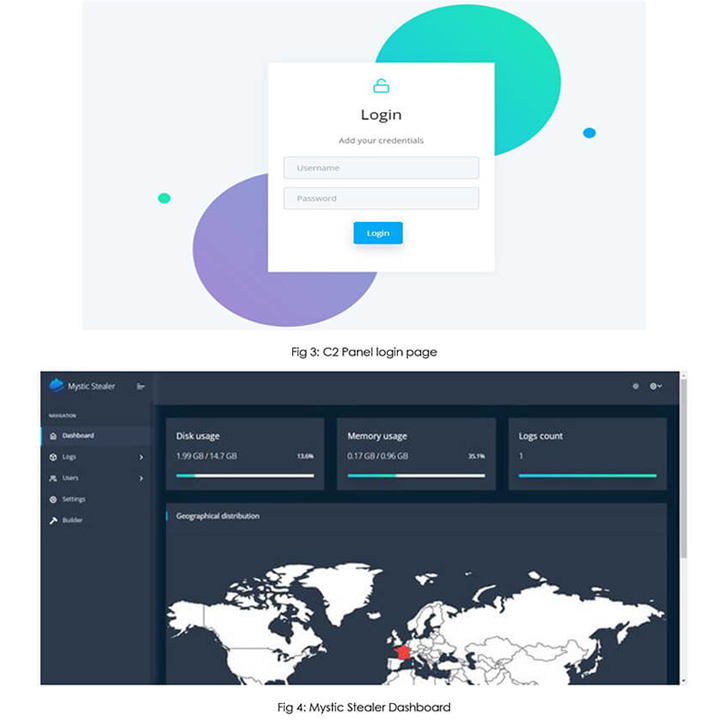
Mystic Stealer, like a lot of other crimeware solutions that are available for sale, focuses on pilfering details and is implemented in the C programming language. The handle panel has been produced applying Python.
Updates to the malware in May well 2023 include a loader component that enables it to retrieve and execute upcoming-phase payloads fetched from a command-and-control (C2) server, creating it a a lot more formidable danger.
C2 communications are reached applying a custom made binary protocol more than TCP. As many as 50 operational C2 servers have been discovered to day. The control panel, for its element, serves as the interface for buyers of the stealer to entry data logs and other configurations.
Cybersecurity company Cyfirma, which posted a concurrent evaluation of Mystic, claimed, “the author of the merchandise brazenly invites solutions for added improvements in the stealer” through a committed Telegram channel, indicating energetic endeavours to court docket the cybercriminal community.
“It looks clear that the developer of Mystic Stealer is seeking to generate a stealer on par with the recent tendencies of the malware house though attempting to focus on anti-evaluation and defense evasion,” the researchers said.

The findings come as infostealers have emerged as a very hot commodity in the underground economic system, often serving as the precursor by facilitating the collection of qualifications to empower initial access into concentrate on environments.
Set differently, stealers are utilised as a basis by other cybercriminals to start economically determined strategies that use ransomware and facts extortion aspects.
The spike in popularity notwithstanding, off-the-shelf stealer malware are not currently being promoted at reasonably priced price ranges to charm to a wider audience, they are also evolving to turn into a lot more deadly, packing in advanced methods to fly beneath the radar.
The ever-evolving and volatile character of the stealer universe is very best exemplified by the continual introduction of new strains this sort of as Album Stealer, Bandit Stealer, Devopt, Fractureiser, and Rhadamanthys in latest months.
In a even further indicator of menace actor’s makes an attempt to evade detection, data stealers and remote access trojans have been noticed packaged in just crypters like AceCryptor, ScrubCrypt (aka BatCloak), and Snip3.
The growth also comes as HP Wolf Security thorough a March 2023 ChromeLoader campaign codenamed Shampoo which is engineered to install a malicious extension in Google Chrome and steal sensitive data, redirect searches, and inject advertisements into a victim’s browser session.
Upcoming WEBINAR🔐 Mastering API Security: Comprehension Your True Attack Area
Uncover the untapped vulnerabilities in your API ecosystem and acquire proactive methods to ironclad security. Be part of our insightful webinar!
Join the Session.wn-button,.wn-label,.wn-label:immediately aftershow:inline-block.check_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px strong #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-top-left-radius:25px-moz-border-radius-topleft:25px-webkit-border-bottom-ideal-radius:25px-moz-border-radius-bottomright:25px.wn-labelfont-dimension:13pxmargin:20px 0font-bodyweight:600letter-spacing:.6pxcolor:#596cec.wn-label:soon afterwidth:50pxheight:6pxcontent:”border-top:2px stable #d9deffmargin: 8px.wn-titlefont-dimensions:21pxpadding:10px 0font-pounds:900textual content-align:leftline-height:33px.wn-descriptiontextual content-align:leftfont-dimension:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.wn-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-fat:500letter-spacing:.2px
“Consumers encountered the malware mostly from downloading unlawful material, this sort of as movies (Cocaine Bear.vbs), video video games, or other,” security researcher Jack Royer stated. “These internet websites trick victims into operating a destructive VBScript on their PCs that triggers the an infection chain.”
The VBScript then proceeds to start PowerShell code able of terminating all existing Chrome windows and opening a new session with the unpacked rogue extension using the “–load-extension” command line argument.
It also follows the discovery of a new modular malware trojan christened Pikabot that has the means to execute arbitrary instructions and inject payloads that are presented by a C2 server, such as Cobalt Strike.
The implant, lively since early 2023, has been uncovered to share resemblances with QBot with regard to distribution procedures, campaigns, and malware behaviors, while there is no conclusive proof connecting the two families.
“Pikabot is a new malware relatives that implements an comprehensive established of anti-analysis approaches and gives prevalent backdoor abilities to load shellcode and execute arbitrary 2nd-stage binaries,” Zscaler stated.
Identified this posting fascinating? Stick to us on Twitter and LinkedIn to read more distinctive written content we publish.
Some elements of this report are sourced from:
thehackernews.com


 Researchers Discover New Sophisticated Toolkit Targeting Apple macOS Systems
Researchers Discover New Sophisticated Toolkit Targeting Apple macOS Systems