Folks in the Pakistan region have been qualified using two rogue Android apps obtainable on the Google Participate in Retailer as element of a new targeted campaign.
Cybersecurity firm Cyfirma attributed the marketing campaign with average confidence to a threat actor recognised as DoNot Group, which is also tracked as APT-C-35 and Viceroy Tiger.
The espionage exercise consists of duping Android smartphone homeowners into downloading a system that’s used to extract call and site info from unwitting victims.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The motive at the rear of the attack is to get info by means of the stager payload and use the collected information and facts for the next-phase attack, using malware with much more destructive capabilities,” the firm mentioned.
DoNot Staff is a suspected India-nexus risk actor that has a status for carrying out attacks in opposition to different international locations in South Asia. It has been active considering that at least 2016.
Although an Oct 2021 report from Amnesty Worldwide linked the group’s attack infrastructure to an Indian cybersecurity business termed Innefu Labs, Group-IB, in February 2023, reported it recognized overlaps involving DoNot Group and SideWinder, a different suspected Indian hacking crew.

Attack chains mounted by the group leverage spear-phishing emails that contains decoy files and documents as lures to distribute malware. In addition, the threat actor is regarded to use malicious Android apps that masquerade as legit utilities in their target attacks.
These apps, when set up, activate trojan behavior in the track record and can remotely handle the victim’s process, apart from pilfering private information and facts from the contaminated devices.
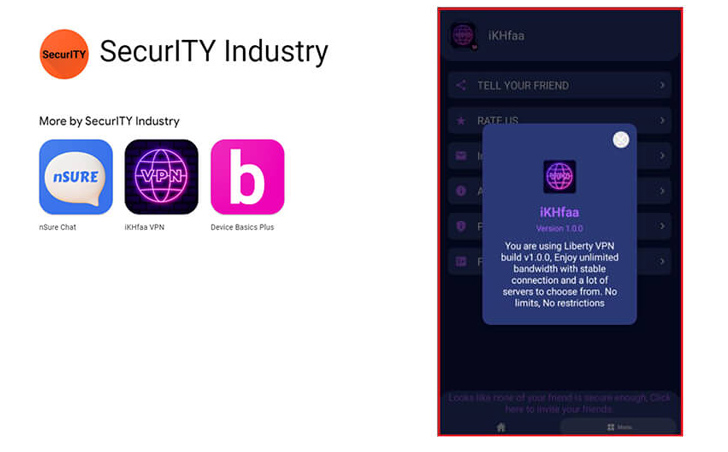
The newest set of purposes found by Cyfirma originate from a developer named “SecurITY Business” and pass off as VPN and chat applications, with the latter nonetheless accessible for download from the Enjoy Retail outlet –
- iKHfaa VPN (com.securityapps.ikhfaavpn) – 10+ downloads
- nSure Chat (com.nSureChat.application) – 100+ downloads
The VPN application, which reuses resource code taken from the genuine Liberty VPN solution, is no lengthier hosted on the official application storefront, while proof shows that it was offered as not too long ago as June 12, 2023.
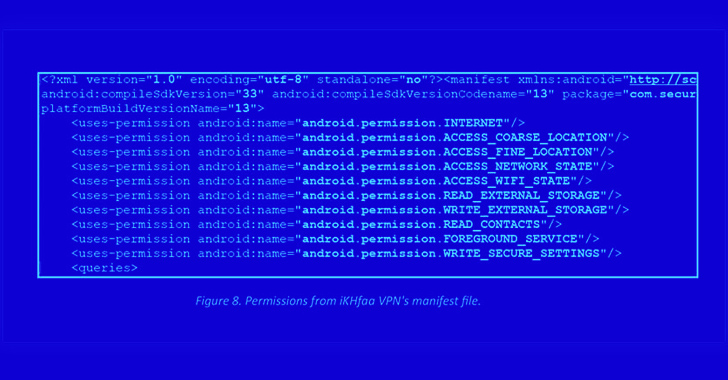
The lower download counts is an indicator that the apps are staying utilised as part of a hugely targeted operation, a hallmark of nation-point out actors. Both applications are configured to trick the victims into granting them invasive permissions to obtain their make contact with lists and precise destinations.
Minor is recognized about the victims targeted using the rogue applications barring the simple fact that they are primarily based in Pakistan. It can be thought that consumers may perhaps have been approached by way of messages on Telegram and WhatsApp to lure them into putting in the applications.
By utilizing the Google Perform Retailer as a malware distribution vector, the solution abuses the implicit believe in positioned by people on the on the net application marketplace and lends it an air of legitimacy. It’s, therefore, critical that apps are thoroughly scrutinized prior to downloading them.
“It seems that this Android malware was exclusively designed for data collecting,” Cyfirma explained. “By gaining access to victims’ speak to lists and locations, the risk actor can strategize potential attacks and use Android malware with superior options to concentrate on and exploit the victims.”
Identified this write-up exciting? Adhere to us on Twitter and LinkedIn to study more special articles we put up.
Some sections of this post are sourced from:
thehackernews.com

 New Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions
New Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions