Industrial and authorities companies, like enterprises in the military-industrial complex and analysis laboratories, are the targets of a new malware botnet dubbed PseudoManyscrypt that has contaminated around 35,000 Windows computer systems this yr on your own.
The title will come from its similarities to the Manuscrypt malware, which is aspect of the Lazarus APT group’s attack toolset, Kaspersky researchers reported, characterizing the operation as a “mass-scale spyware attack marketing campaign.” The Russian cybersecurity business stated it very first detected the series of intrusions in June 2021.
At minimum 7.2% of all pcs attacked by the malware are portion of industrial manage methods (ICS) used by businesses in engineering, developing automation, strength, producing, development, utilities, and drinking water management sectors that are positioned primarily in India, Vietnam, and Russia. Close to a third (29.4%) of non-ICS pcs are located in Russia (10.1%), India (10%), and Brazil (9.3%).

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

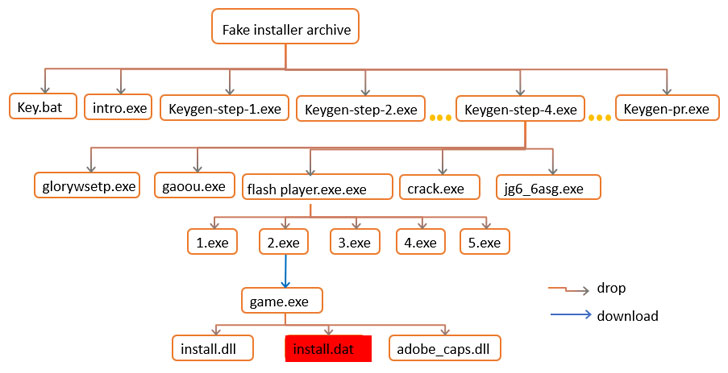
“The PseudoManuscrypt loader helps make its way on to person programs by using a MaaS platform that distributes malware in pirated software program installer archives,” the Kaspersky ICS CERT workforce claimed. “A person unique case of the PseudoManuscrypt downloader’s distribution is its set up by using the Glupteba botnet.”
Coincidentally, Glupteba’s functions have also taken a sizeable hit when Google previously this thirty day period disclosed that it acted to dismantle the botnet’s infrastructure and pursued litigation towards two Russian nationals, who are alleged to have managed the malware together with 15 other unnamed folks.
Among the cracked installers that are applied to gasoline the botnet represent Windows 10, Microsoft Business, Adobe Acrobat, Garmin, Call of Obligation, SolarWinds Engineer’s Toolset, and even Kaspersky’s individual antivirus resolution. The pirated computer software installations are driven by a strategy identified as search poisoning in which the attackers create malicious internet websites and use look for engine optimization (Search engine optimisation) techniques to make them clearly show up prominently in look for success.
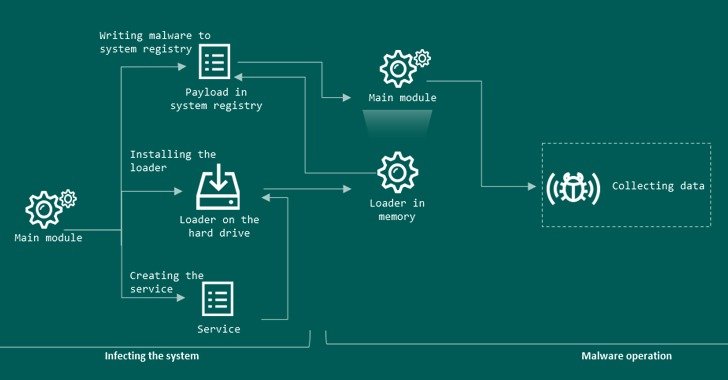
As soon as put in, PseudoManuscrypt will come with an array of intrusive abilities that makes it possible for the attackers to complete manage of the contaminated system. This is made up of disabling antivirus remedies, thieving VPN link information, logging keystrokes, recording audio, capturing screenshots and videos of the screen, and intercepting info saved in the clipboard.
Kaspersky famous it has discovered 100 distinctive variations of the PseudoManuscrypt loader, with the earliest take a look at variants courting again to March 27, 2021. Elements of the trojan have been borrowed from commodity malware like Fabookie and a KCP protocol library utilized by the China-dependent APT41 team.
The malware samples analyzed by the ICS CERT also highlighted feedback composed in Chinese and have been located specifying Chinese as the most well-liked language, but these clues by yourself have been inconclusive to make an assessment about the malware’s operators or their origins. Also unclear are the top targets of the campaign, increasing thoughts as to regardless of whether the attacks are economically motivated or state-backed.
“The large variety of engineering personal computers attacked, together with techniques used for 3D and physical modeling, the advancement and use of digital twins raises the issue of industrial espionage as one of the achievable goals of the campaign,” the researchers explained.
Observed this posting exciting? Follow THN on Fb, Twitter and LinkedIn to browse far more exceptional content we post.
Some sections of this article are sourced from:
thehackernews.com


 How to Prevent Customer Support Help Desk Fraud Using VPN and Other Tools
How to Prevent Customer Support Help Desk Fraud Using VPN and Other Tools