Cybersecurity scientists on Wednesday disclosed a previously undocumented backdoor probably intended and made by the Nobelium innovative persistent danger (APT) at the rear of last year’s SolarWinds provide chain attack, becoming a member of the risk actor’s at any time-expanding arsenal of hacking tools.
Moscow-headquartered firm Kaspersky codenamed the malware “Tomiris,” contacting out its similarities to one more second-phase malware applied during the marketing campaign, SUNSHUTTLE (aka GoldMax), targeting the IT administration computer software provider’s Orion system. Nobelium is also acknowledged by the monikers UNC2452, SolarStorm, StellarParticle, Dark Halo, and Iron Ritual.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
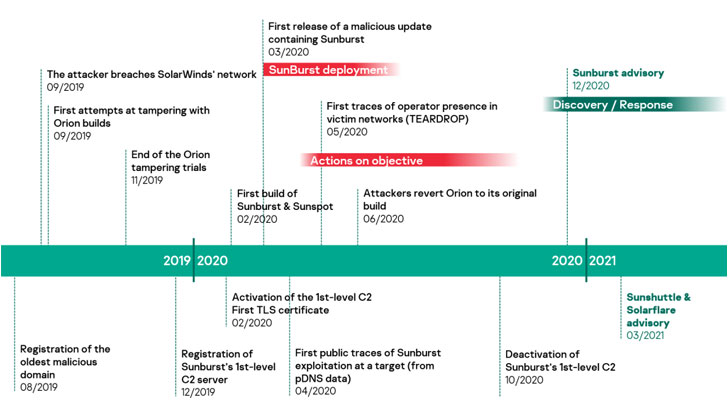
“Although provide-chain attacks have been now a documented attack vector leveraged by a selection of APT actors, this unique marketing campaign stood out owing to the excessive carefulness of the attackers and the superior-profile character of their victims,” Kaspersky scientists claimed. “Proof gathered so far implies that Dark Halo expended six months within Orion It is networks to best their attack and make guaranteed that their tampering of the construct chain would not cause any adverse outcomes.”
Microsoft, which comprehensive SUNSHUTTLE in March 2021, explained the strain as a Golang-based mostly malware that acts as a command-and-management backdoor, establishing a safe link with an attacker-controlled server to fetch and execute arbitrary instructions on the compromised machine as nicely as exfiltrate files from the procedure to the server.
The new Tomiris backdoor, uncovered by Kaspersky in June this year from samples dating back to February, is also prepared in Go and deployed via a effective DNS hijacking attack during which targets attempting to access the login website page of a corporate email company have been redirected to a fraudulent area set up with a lookalike interface intended to trick the site visitors into downloading the malware beneath the guise of a security update.
The attacks are considered to have been mounted in opposition to numerous govt corporations in an unnamed CIS member state.
“The most important goal of the backdoor was to build a foothold in the attacked procedure and to obtain other destructive parts,” the scientists said, in addition to locating a range of similarities ranging from the encryption plan to the similar spelling problems that collectively hint at the “possibility of common authorship or shared growth tactics.”

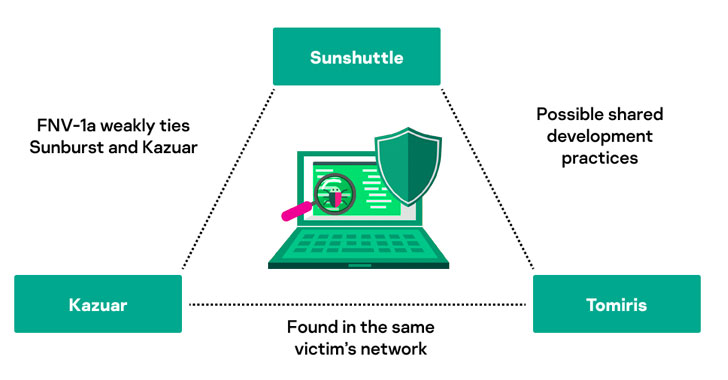
This is not the initial time overlaps have been discovered involving diverse applications set to use by the menace actor. Previously this calendar year, Kaspersky’s evaluation of Sunburst disclosed a number of shared characteristics involving the malware and Kazuar, a .NET-dependent backdoor attributed to the Turla group. Interestingly, the cybersecurity organization explained it detected Tomiris in networks exactly where other machines ended up infected with Kazuar, incorporating pounds to prospective clients that the 3 malware households could be connected to each and every other.
Possessing explained that, the scientists pointed out it could also be a circumstance of a fake flag attack, wherein threat actors deliberately reproduce the methods and strategies adopted by a recognised adversary in an attempt to mislead attribution.
The revelation comes times after Microsoft took the wraps of a passive and highly targeted implant dubbed FoggyWeb that was used by the Nobelium team to provide supplemental payloads and steal sensitive facts from Energetic Listing Federation Services (Advertisement FS) servers.
Located this post attention-grabbing? Observe THN on Fb, Twitter and LinkedIn to go through more exclusive written content we post.
Some components of this write-up are sourced from:
thehackernews.com

 Cybersecurity Firm Group-IB’s CEO Arrested Over Treason Charges in Russia
Cybersecurity Firm Group-IB’s CEO Arrested Over Treason Charges in Russia