The maintainers of the NGINX web server job have issued mitigations to handle security weaknesses in its Lightweight Directory Obtain Protocol (LDAP) Reference Implementation.
“NGINX Open Supply and NGINX Moreover are not them selves afflicted, and no corrective action is essential if you do not use the reference implementation,” Liam Crilly and Timo Stark of F5 Networks stated in an advisory posted Monday.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
NGINX explained that the reference implementation, which utilizes LDAP to authenticate customers, is impacted only below three problems if the deployments require –
- Command-line parameters to configure the Python-primarily based reference implementation daemon
- Unused, optional configuration parameters, and
- Particular team membership to carry out LDAP authentication
Ought to any of the aforementioned ailments be satisfied, an attacker could likely override the configuration parameters by sending specially crafted HTTP request headers and even bypass group membership demands to force LDAP authentication to thrive even when the falsely authenticated consumer does’t belong to the group.
As countermeasures, the project maintainers have encouraged people to ensure that special figures are stripped from the username subject in the login type presented in the course of authentication and update acceptable configuration parameters with an empty value (“”).
The maintainers also pressured that the LDAP reference implementation mainly “describes the mechanics of how the integration is effective and all of the elements demanded to validate the integration” and that “it is not a production‑grade LDAP answer.”
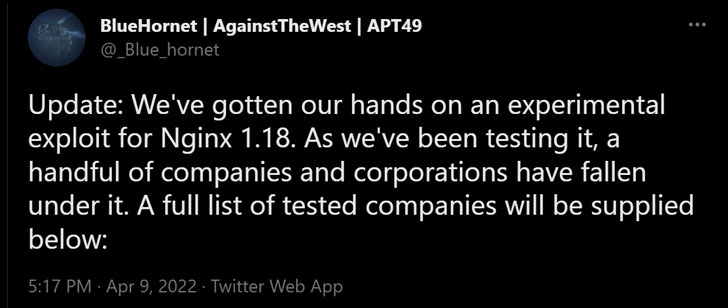
The disclosure will come right after details of the issue emerged in the community domain more than the weekend when a hacktivist group identified as BlueHornet reported it had “gotten our hands on an experimental exploit for NGINX 1.18.”
Observed this article attention-grabbing? Comply with THN on Facebook, Twitter and LinkedIn to examine more special articles we put up.
Some areas of this post are sourced from:
thehackernews.com



 Finding Attack Paths in Cloud Environments
Finding Attack Paths in Cloud Environments