A prolific North Korean state-sponsored hacking group has been tied to a new ongoing espionage campaign aimed at exfiltrating delicate details from companies in the defense sector.
Attributing the attacks with significant self-assurance to the Lazarus Team, the new findings from Kaspersky sign an enlargement of the APT actor’s methods by going outside of the common gamut of fiscally-inspired crimes to fund the cash-strapped routine.
This broadening of its strategic interests occurred in early 2020 by leveraging a software referred to as ThreatNeedle, scientists Vyacheslav Kopeytsev and Seongsu Park stated in a Thursday create-up.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
At a large level, the marketing campaign leverages a multi-move method that begins with a very carefully crafted spear-phishing attack foremost ultimately to the attackers getting distant regulate above the equipment.
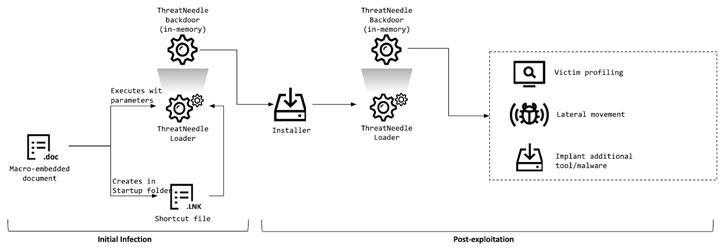
ThreatNeedle is shipped to targets by using COVID-themed e-mails with malicious Microsoft Term attachments as initial infection vectors that, when opened, operate a macro that contains destructive code created to download and execute added payloads on the infected program.
The up coming-phase malware capabilities by embedding its malicious capabilities inside a Windows backdoor that delivers functions for first reconnaissance and deploying malware for lateral movement and info exfiltration.
“The moment put in, ThreatNeedle is ready to get hold of full command of the victim’s product, this means it can do anything from manipulating files to executing obtained commands,” Kaspersky security scientists reported.
Kaspersky found overlaps among ThreatNeedle and a different malware family termed Manuscrypt that has been utilised by Lazarus Team in past hacking strategies against the cryptocurrency and cell online games industries, besides uncovering connections with other Lazarus clusters these types of as AppleJeus, DeathNote, and Bookcode.
Interestingly, Manuscrypt was also deployed in a Lazarus Group operation previous month, which included targeting the cybersecurity neighborhood with possibilities to collaborate on vulnerability investigation, only to infect victims with malware that could trigger the theft of exploits made by the scientists for perhaps undisclosed vulnerabilities, therefore making use of them to stage even further attacks on vulnerable targets of their preference.
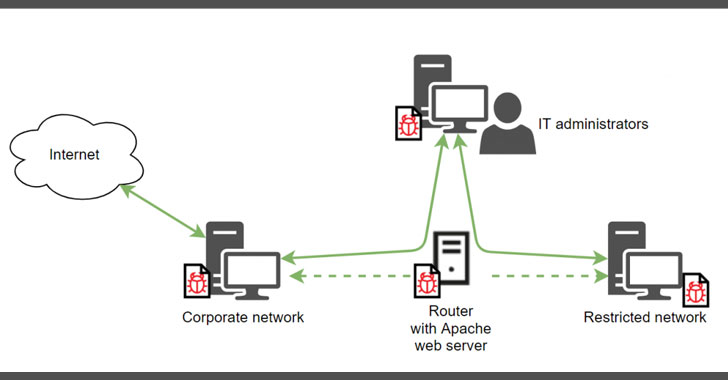
Most likely the most about of the advancement is a method adopted by the attackers to bypass network segmentation protections in an unnamed company network by “gaining obtain to an internal router machine and configuring it as a proxy server, enabling them to exfiltrate stolen data from the intranet network to their distant server.”
The cybersecurity agency mentioned businesses in extra than a dozen countries have been influenced to day.
At the very least just one of the spear-phishing emails referenced in the report is penned in Russian, when a different information came with a destructive file attachment named “Boeing_AERO_GS.docx,” potentially implying a U.S. target.
Earlier this thirty day period, three North Korean hackers linked with the armed forces intelligence division of North Korea were indicted by the U.S. Justice Office for allegedly using component in a legal conspiracy that tried to extort $1.3 billion in cryptocurrency and funds from banking companies and other companies about the earth.
“In new yrs, the Lazarus team has targeted on attacking monetary institutions around the entire world,” the scientists concluded. “Having said that, starting in early 2020, they focused on aggressively attacking the defense market.”
“Whilst Lazarus has also previously used the ThreatNeedle malware applied in this attack when targeting cryptocurrency companies, it is currently getting actively utilized in cyberespionage attacks.”
Discovered this article fascinating? Adhere to THN on Facebook, Twitter and LinkedIn to read through much more distinctive material we put up.
Some parts of this short article are sourced from:
thehackernews.com

 Npower Ditches App After Credential Stuffing Attacks
Npower Ditches App After Credential Stuffing Attacks