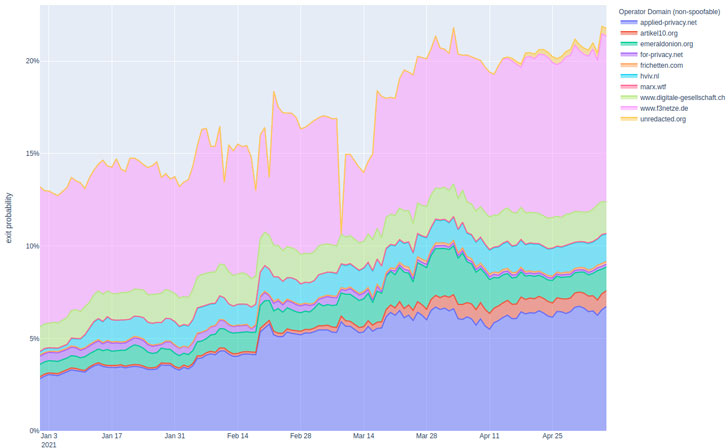
An mysterious danger actor managed to command extra than 27% of the full Tor network exit potential in early February 2021, a new examine on the dark web infrastructure unveiled.
“The entity attacking Tor users is actively exploiting tor consumers due to the fact over a yr and expanded the scale of their attacks to a new document degree,” an impartial security researcher who goes by the title nusenu claimed in a write-up posted on Sunday. “The ordinary exit fraction this entity managed was above 14% through the past 12 months.”
It can be the latest in a collection of endeavours carried out to convey to light-weight malicious Tor action due to the fact December 2019. The attacks, which are stated to have started in January 2020, have been 1st documented and exposed by the exact same researcher in August 2020.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Tor is open up-resource software program for enabling nameless conversation on the Internet. It obfuscates the source and destination of a web ask for by directing network targeted traffic as a result of a collection of relays in get to mask a user’s IP handle and location and use from surveillance or visitors examination. While middle relays commonly take care of getting visitors on the Tor network and move it together, an exit relay is the ultimate node that Tor site visitors passes by before it reaches its place.
Exit nodes on the Tor network have been subverted in the previous to inject malware these as OnionDuke, but this is the initial time a solitary unknown actor has managed to handle this sort of a big portion of Tor exit nodes.
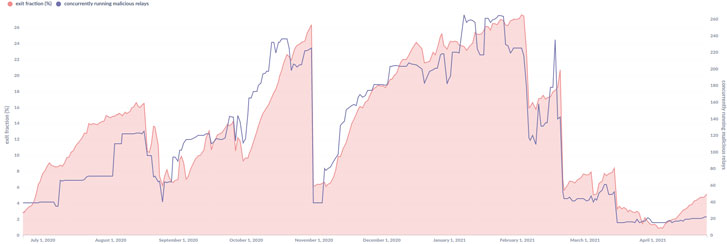
The hacking entity maintained 380 malicious Tor exit relays at its peak in August 2020, just before the Tor directory authorities intervened to cull the nodes from the network, following which the exercise after again crested early this year, with the attacker making an attempt to add over 1,000 exit relays in the first 7 days of Could. All the destructive Tor exit relays detected in the course of the next wave of the attacks have since been eradicated.
The primary purpose of the attack, in accordance to nusenu, is to carry out “person-in-the-center” attacks on Tor buyers by manipulating site visitors as it flows as a result of its network of exit relays. Specially, the attacker appears to perform what is actually termed SSL stripping to downgrade website traffic heading to Bitcoin mixer companies from HTTPS to HTTP in an attempt to substitute bitcoin addresses and redirect transactions to their wallets instead of the person-furnished bitcoin tackle.
“If a user frequented the HTTP variation (i.e. the unencrypted, unauthenticated model) of one of these websites, they would protect against the internet site from redirecting the user to the HTTPS version (i.e. the encrypted, authenticated version) of the site,” the maintainers of Tor Project explained last August. “If the consumer did not see that they hadn’t finished up on the HTTPS model of the web page (no lock icon in the browser) and proceeded to ship or acquire delicate details, this details could be intercepted by the attacker.”
To mitigate such attacks, the Tor Challenge outlined a number of suggestions, which includes urging web-site directors to empower HTTPS by default and deploy .onion websites to prevent exit nodes, adding it’s functioning on a “in depth fix” to disable plain HTTP in Tor Browser.
“The risk of staying the target of malicious action routed by way of Tor is unique to each business,” the U.S. Cybersecurity Security and Infrastructure Security Agency (CISA) explained in an advisory in July 2020. “An group must decide its particular person risk by assessing the chance that a risk actor will goal its units or details and the probability of the threat actor’s accomplishment given present mitigations and controls.”
“Businesses really should appraise their mitigation decisions against threats to their organization from highly developed persistent threats (APTs), reasonably sophisticated attackers, and very low-proficient particular person hackers, all of whom have leveraged Tor to have out reconnaissance and attacks in the past,” the company additional.
Uncovered this short article exciting? Stick to THN on Facebook, Twitter and LinkedIn to read additional exceptional information we publish.
Some elements of this post are sourced from:
thehackernews.com

 Russian hackers are exploiting these 11 flaws to attack businesses
Russian hackers are exploiting these 11 flaws to attack businesses