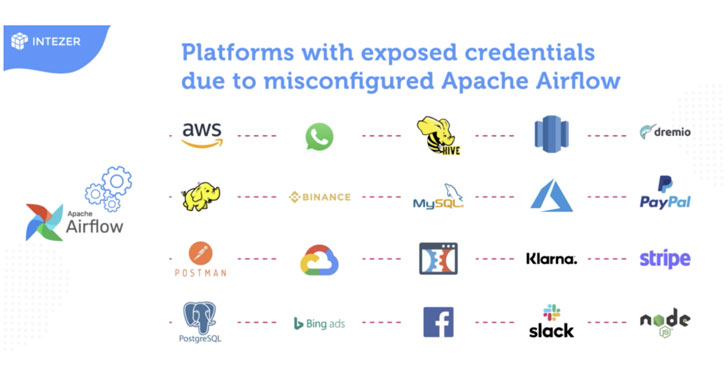
Cybersecurity researchers on Monday discovered misconfigurations throughout more mature versions of Apache Airflow circumstances belonging to a variety of superior-profile organizations throughout different sectors, resulting in the publicity of delicate credentials for well-known platforms and expert services these types of as Amazon Web Providers (AWS), Binance, Google Cloud Platform (GCP), PayPal, Slack, and Stripe.
“These unsecured occasions expose delicate data of businesses across the media, finance, producing, details technology (IT), biotech, e-commerce, overall health, electrical power, cybersecurity, and transportation industries,” Intezer mentioned in a report shared with The Hacker Information.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
At first introduced in June 2015, Apache Airflow is an open-source workflow administration platform that permits programmatic scheduling and monitoring of workflows on AWS, GCP, Microsoft Azure, and other third-party companies. It really is also 1 of the most well-known activity orchestration instruments, adopted by Luigi, Kubeflow, and MLflow.
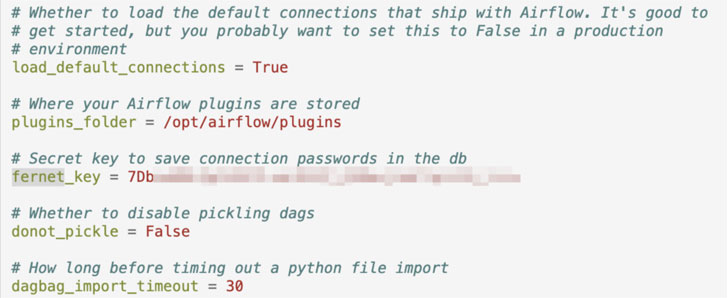
Some of the most common insecure coding methods uncovered by Intezer include things like the use of challenging-coded databases passwords in Python DAG code or variables, plaintext credentials in the “Extra” field of connections, and cleartext keys in configuration information (airflow.cfg).
Main among the the issues linked with misconfigured Airflow instances is the publicity of qualifications that could be abused by risk actors to attain obtain to accounts and databases, providing them the ability to spread laterally or final result in knowledge leakage, not to point out guide to violation of details protection regulations and give an perception into an organization’s instruments and packages, which could afterwards be exploited to phase offer-chain attacks.

“If a significant amount of passwords are seen, a risk actor can also use this knowledge to detect designs and prevalent terms to infer other passwords,” Intezer scientists said. “These can be leveraged in dictionary or brute-drive-design and style attacks from other platforms.”
Even much more relating to is also the likelihood that malware can be introduced on the exposed output environments by leveraging the Variables feature to modify the container image variables to place to a distinct impression that contains unauthorized code.
Apache Airflow, for its part, has remediated a whole lot of security issues with model 2.. that was released in December 2020, building it critical that people of the program update to the most up-to-date variation and undertake safe coding procedures to avert passwords from remaining exposed.
Located this article interesting? Stick to THN on Fb, Twitter and LinkedIn to read through extra exceptional written content we post.
Some elements of this report are sourced from:
thehackernews.com

 4.6 million Neiman Marcus customers’ data compromised in a breach
4.6 million Neiman Marcus customers’ data compromised in a breach