Graphic for illustration
Cybersecurity scientists on Tuesday disclosed details about an handle bar spoofing vulnerability impacting a number of cellular browsers, these as Apple Safari and Opera Contact, leaving the door open up for spear-phishing attacks and delivering malware.
Other impacted browsers include things like UCWeb, Yandex Browser, Bolt Browser, and RITS Browser.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The flaws have been uncovered by Pakistani security researcher Rafay Baloch in the summer of 2020 and jointly noted by Baloch and cybersecurity agency Speedy7 in August just before they were being dealt with by the browser makers above the earlier few weeks.
UCWeb and Bolt Browser stay unpatched as but, when Opera Mini is envisioned to receive a repair on November 11, 2020.
The issue stems from using malicious executable JavaScript code in an arbitrary site to drive the browser to update the tackle bar though the web site is nonetheless loading to another address of the attacker’s choice.
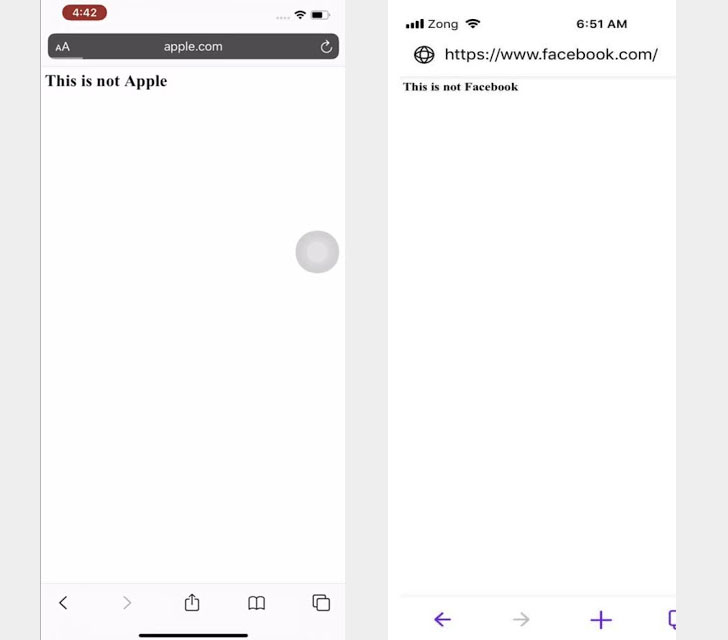 Unique PoC demo
Unique PoC demo
“The vulnerability happens because of to Safari preserving address bar of the URL when requested around an arbitrary port, the set interval purpose reloads bing.com:8080 every 2 milliseconds and that’s why user is unable to recognize the redirection from the primary URL to spoofed URL,” Rafay Baloch said in complex examination.
“What tends to make this vulnerability extra successful in Safari by default does not expose port quantity in URL until and until eventually concentrate is established by using cursor.”
Put in another way an attacker can set up a malicious website and lure the goal into opening the link from a spoofed email or text message, thus main an unsuspecting recipient into downloading malware or risk having their credentials stolen.
The research also observed the macOS version of Safari to be susceptible to the very same bug, which in accordance to Swift7 has been dealt with in a Significant Sur macOS update produced previous week.
This is not the 1st time these types of vulnerability has been noticed in Safari. Again in 2018, Baloch disclosed a related kind of deal with bar spoofing flaw that induced the browser to preserve the deal with bar and to load the written content from the spoofed site through a JavaScript-induced timing delay.
“With at any time rising sophistication of spear phishing attacks, exploitation of browser-primarily based vulnerabilities these types of as tackle bar spoofing might exacerbate the accomplishment of spear-phishing attacks and hence demonstrate to be very deadly,” Baloch said.
“1st and foremost, it is effortless to persuade the victim into thieving qualifications or distributing malware when the deal with bar factors to a dependable site and supplying no indicators forgery, next because the vulnerability exploits a unique element in a browser, it can evade many anti-phishing strategies and options.”
Located this article interesting? Abide by THN on Fb, Twitter and LinkedIn to examine additional unique material we article.
Some sections of this short article are sourced from:
thehackernews.com


 SC Media aces phishing test (whew!), but average score was only 52%
SC Media aces phishing test (whew!), but average score was only 52%