Cybersecurity researchers have disclosed a new backdoor plan capable of thieving user login credentials, system data and executing arbitrary instructions on Linux systems.
The malware dropper has been dubbed “Facefish” by Qihoo 360 NETLAB crew owing its abilities to supply distinctive rootkits at distinct moments and the use of Blowfish cipher to encrypt communications to the attacker-managed server.
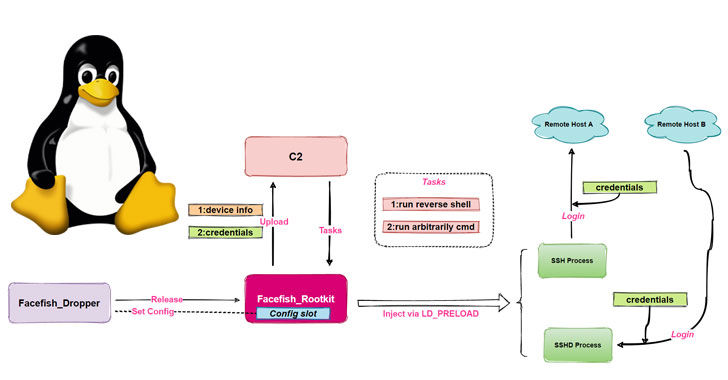
“Facefish consists of 2 pieces, Dropper and Rootkit, and its most important functionality is determined by the Rootkit module, which will work at the Ring 3 layer and is loaded making use of the LD_PRELOAD element to steal user login qualifications by hooking ssh/sshd software similar features, and it also supports some backdoor features,” the scientists said.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The NETLAB investigate builds on a past evaluation posted by Juniper Networks on April 26, which documented an attack chain concentrating on Regulate Web Panel (CWP, formerly CentOS Web Panel) to inject an SSH implant with details exfiltration capabilities.
Facefish goes by means of a multi-phase infection system, which commences with a command injection in opposition to the CWP to retrieve a dropper (“sshins”) from a distant server, which then releases a rootkit that in the long run requires cost of accumulating and transmitting delicate information back again to the server, in addition to awaiting further recommendations issued by the command-and-management (C2) server.
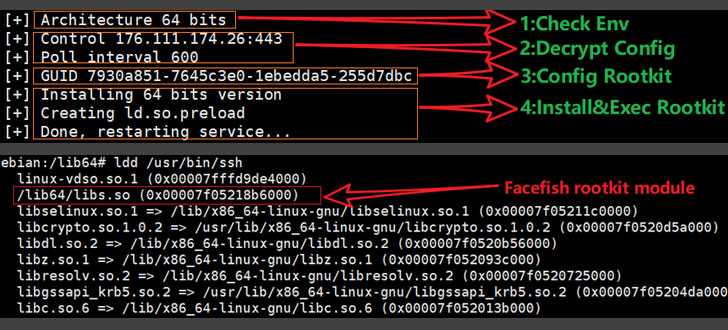
For its part, the dropper arrives with its personal set of tasks, chief amid being detecting the runtime atmosphere, decrypting a configuration file to get C2 facts, configuring the rootkit, and commencing the rootkit by injecting it into the protected shell server method (sshd).
Rootkits are specially unsafe as they make it possible for attackers to acquire elevated privileges in the technique, permitting them to interfere with core functions performed by the underlying working method. This potential of rootkits to camouflage into the fabric of the working program provides attackers a significant level of stealth and evasion.
Facefish also employs a advanced conversation protocol and encryption algorithm, employing guidelines commencing with 0x2XX to trade general public keys and BlowFish for encrypting interaction data with the C2 server. Some of the C2 commands sent by the server are as follows –
- 0x300 – Report stolen credential info
- 0x301 – Collect information of “uname” command
- 0x302 – Run reverse shell
- 0x310 – Execute any procedure command
- 0x311 – Send the result of bash execution
- 0x312 – Report host data
NETLAB’s findings come from an examination of an ELF sample file it detected in February 2021. Other indicators of compromise connected with the malware can be accessed listed here.
Uncovered this article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read more distinctive written content we submit.
Some components of this write-up are sourced from:
thehackernews.com

 What is an SOC audit?
What is an SOC audit?