Cybersecurity researchers have in-depth a new marketing campaign that very likely targets entities in Southeast Asia with a earlier unrecognized Linux malware that’s engineered to permit distant entry to its operators, in addition to amassing qualifications and purpose as a proxy server.
The malware spouse and children, dubbed “FontOnLake” by Slovak cybersecurity agency ESET, is claimed to feature “very well-made modules” that are consistently remaining upgraded with new features, indicating an energetic progress period. Samples uploaded to VirusTotal issue to the probability that the pretty to start with intrusions utilizing this danger have been happening as early as May possibly 2020.
Avast and Lacework Labs are monitoring the similar malware under the moniker HCRootkit.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The sneaky nature of FontOnLake’s instruments in combination with state-of-the-art structure and reduced prevalence advise that they are used in focused attacks,” ESET researcher Vladislav Hrčka claimed. “To collect knowledge or carry out other destructive action, this malware household takes advantage of modified respectable binaries that are altered to load more elements. In truth, to conceal its existence, FontOnLake’s presence is always accompanied by a rootkit. These binaries are commonly utilised on Linux units and can moreover serve as a persistence system.”
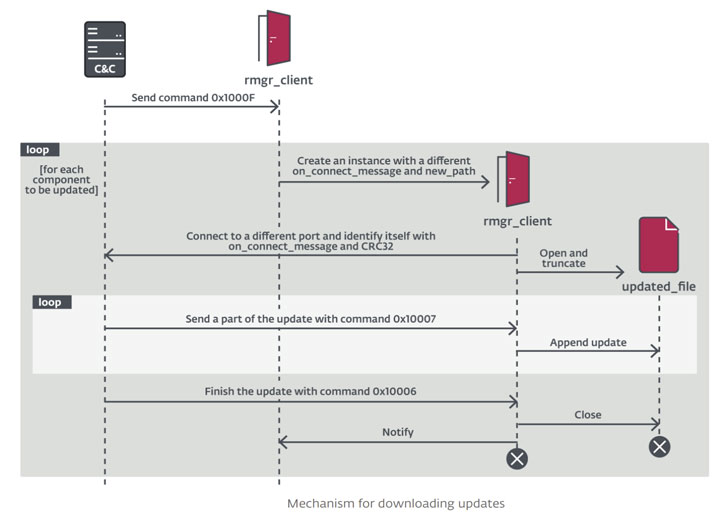
FontOnLake’s toolset involves 3 factors that consist of trojanized variations of legit Linux utilities that are employed to load kernel-manner rootkits and consumer-method backdoors, all of which connect with a person a further employing digital information. The C++-dependent implants by themselves are developed to check techniques, secretly execute instructions on networks, and exfiltrate account credentials.
A next permutation of the backdoor also comes with abilities to act as a proxy, manipulate data files, download arbitrary files, even though a 3rd variant, apart from incorporating attributes from the other two backdoors, is outfitted to execute Python scripts and shell commands.
ESET stated it located two distinctive versions of the Linux rootkit that’s dependent on an open up-resource task identified as Suterusu and share overlaps in functionality, together with hiding procedures, data files, network connections, and by itself, although also staying in a position to have out file functions, and extract and execute the person-method backdoor.

It really is at the moment not recognized how the attackers achieve original accessibility to the network, but the cybersecurity company pointed out that the menace actor powering the attacks is “overly cautious” to avoid leaving any tracks by relying on diverse, unique command-and-regulate (C2) servers with different non-typical ports. All the C2 servers observed in the VirusTotal artifacts are no extended active.
“Their scale and highly developed design suggest that the authors are effectively versed in cybersecurity and that these equipment may be reused in potential strategies,” Hrčka said. “As most of the features are created just to cover its presence, relay conversation, and present backdoor obtain, we feel that these equipment are employed largely to keep an infrastructure which serves some other, not known, destructive applications.”
Discovered this post exciting? Follow THN on Fb, Twitter and LinkedIn to study a lot more exceptional written content we article.
Some areas of this post are sourced from:
thehackernews.com

 How to become a cyber security expert
How to become a cyber security expert