A new wave of phishing campaigns has been observed spreading a earlier documented malware called SVCReady.
“The malware is noteworthy for the uncommon way it is delivered to concentrate on PCs — utilizing shellcode concealed in the houses of Microsoft Workplace documents,” Patrick Schläpfer, a danger analyst at HP, claimed in a complex write-up.
SVCReady is mentioned to be in its early stage of advancement, with the authors iteratively updating the malware numerous periods last thirty day period. Initial indicators of exercise date back again to April 22, 2022.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
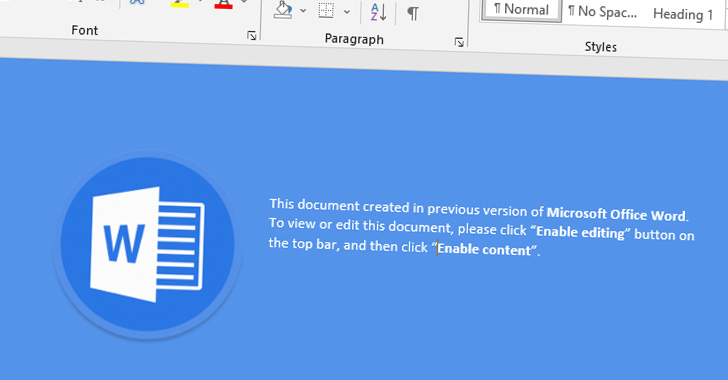
An infection chains involve sending Microsoft Word doc attachments to targets by means of email that comprise VBA macros to activate the deployment of destructive payloads.

But where by this marketing campaign stands aside is that instead of using PowerShell or MSHTA to retrieve next-stage executables from a distant server, the macro runs shellcode stored in the document attributes, which subsequently drops the SVCReady malware.
In addition to attaining persistence on the contaminated host by means of a scheduled job, the malware comes with the means to assemble technique info, seize screenshots, operate shell commands, as effectively as download and execute arbitrary files.
This also included delivering RedLine Stealer as a observe-up payload in one particular occasion on April 26 immediately after a device was initially compromised with SVCReady.

HP claimed it determined overlaps in between the file names of the entice files and the photos contained in the files used to distribute SVCReady and all those used by an additional team called TA551 (aka Hive0106 or Shathak), but it can be not right away clear if the same risk actor is behind the most up-to-date campaign.
“It is feasible that we are viewing the artifacts remaining by two different attackers who are using the exact equipment,” Schläpfer famous. “Nevertheless, our results display that identical templates and possibly doc builders are currently being utilized by the actors driving the TA551 and SVCReady strategies.”
Identified this posting interesting? Adhere to THN on Fb, Twitter and LinkedIn to browse far more special material we post.
Some parts of this short article are sourced from:
thehackernews.com

 Cyber-Attack Surface “Spiralling Out of Control”
Cyber-Attack Surface “Spiralling Out of Control”