The threat actors at the rear of RomCom RAT are leveraging a network of bogus sites promoting rogue variations of common program at the very least considering that July 2022 to infiltrate targets.
Cybersecurity organization Craze Micro is monitoring the action cluster less than the identify Void Rabisu, which is also recognised as Tropical Scorpius (Device 42) and UNC2596 (Mandiant).
“These entice web sites are most possible only meant for a compact range of targets, hence generating discovery and examination a lot more tough,” security scientists Feike Hacquebord, Stephen Hilt, Fernando Merces, and Lord Alfred Remorin claimed.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
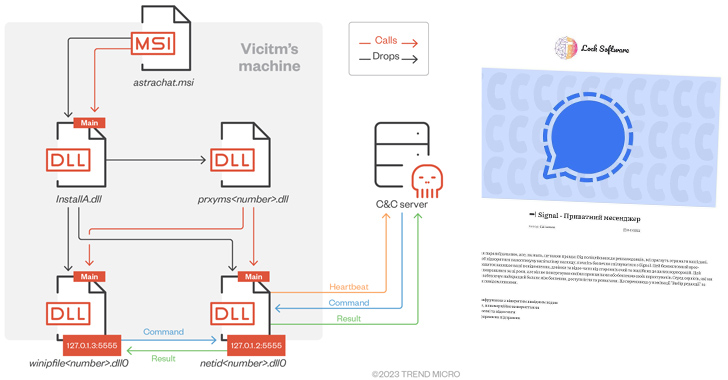
Some of the impersonated applications spotted so considerably consist of AstraChat, Devolutions’ Remote Desktop Manager, Gimp, GoTo Conference, KeePass, OpenAI ChatGPT, Sign, Veeam Backup & Replication, and WinDirStat.
RomCom RAT was to start with chronicled by Palo Alto Networks Unit 42 in August 2022, linking it to a fiscally motivated group deploying Cuba Ransomware (aka COLDDRAW). It can be well worth noting that there is no proof to suggest that the ransomware gang has any connection or affiliation with the Republic of Cuba.
The distant entry trojan has since been applied greatly in attacks concentrating on Ukrainian point out bodies and armed forces systems by way of spoofed variations of authentic software. Other isolated targets have been found in the Americas and Asia.
Void Rabisu has also been noticed abusing Google Ads to trick users into browsing the entice web-sites as aspect of narrowly qualified attacks, generating it the most up-to-date addition in a extended checklist of threat actors acquiring new avenues for getting first obtain into victims’ units.

“RomCom utilised spear-phishing against a member of a European parliament in March 2022, but qualified a European protection business in October 2022 with a Google Adverts ad that led to an intermediary landing website that would redirect to a RomCom entice site,” Pattern Micro claimed.
This points to the adversary mixing its targeting methodology to encompass methods linked with equally cybercrime actors and country-point out groups.
The change in RomCom RAT’s utilization as a backdoor for focused intrusions has been complemented by major enhancements to the malware that scales up the variety of supported instructions from 20 to 49, enabling it to exert full command more than the compromised hosts.
Upcoming WEBINAR Zero Trust + Deception: Find out How to Outsmart Attackers!
Find how Deception can detect advanced threats, stop lateral movement, and increase your Zero Believe in technique. Be part of our insightful webinar!
Save My Seat!.ad-button,.advert-label,.advertisement-label:followingshow:inline-block.ad_two_webinarmargin:20px 10px 30px 0background:#f9fbffcolor:#160755padding: 5%border:2px reliable #d9deffborder-radius:10pxtext-align:leftbox-shadow:10px 10px #e2ebff-webkit-border-major-remaining-radius:25px-moz-border-radius-topleft:25px-webkit-border-base-suitable-radius:25px-moz-border-radius-bottomright:25px.ad-labelfont-measurement:13pxmargin:20px 0font-pounds:600letter-spacing:.6pxcolor:#596cec.advert-label:afterwidth:50pxheight:6pxcontent:”border-top:2px sound #d9deffmargin: 8px.advertisement-titlefont-measurement:21pxpadding:10px 0font-weight:900text-align:leftline-peak:33px.ad-descriptiontextual content-align:leftfont-measurement:15.6pxline-peak:26pxmargin:5px !importantcolor:#4e6a8d.advert-buttonpadding:6px 12pxborder-radius:5pxbackground-coloration:#4469f5font-dimensions:15pxcolor:#fff!importantborder:0line-top:inherittext-decoration:none!importantcursor:pointermargin:15px 20pxfloat:leftfont-weight:500letter-spacing:.2px
This also contains the ability to obtain extra payloads to take screenshots, grab crypto wallet knowledge, siphon chat messages and FTP credentials, and use a browser password stealer dubbed StealDeal.
An additional noteworthy aspect of the attacks is the use of certificates to lend reliability to the destructive software package installers, with samples signed by seemingly innocuous corporations dependent in the U.S. and Canada.
“The line is blurring between cybercrime pushed by money obtain and APT attacks inspired by geopolitics, espionage, disruption, and warfare,” the researchers said.
“Since the increase of Ransomware-as-a-Assistance (RaaS), cybercriminals are not using sophisticated ways and specific attacks that have been beforehand thought to be the domain of APT actors. Inversely, techniques and methods that were being previously made use of by economically inspired actors are more and more being utilized in attacks with geopolitical goals.”
Identified this posting exciting? Adhere to us on Twitter and LinkedIn to browse far more exclusive articles we submit.
Some components of this article are sourced from:
thehackernews.com

 Alert: Hackers Exploit Barracuda Email Security Gateway 0-Day Flaw for 7 Months
Alert: Hackers Exploit Barracuda Email Security Gateway 0-Day Flaw for 7 Months