Amazon has addressed a quantity of flaws in its Kindle e-reader platform that could have allowed an attacker to get management of victims’ equipment by only sending them a malicious e-guide.
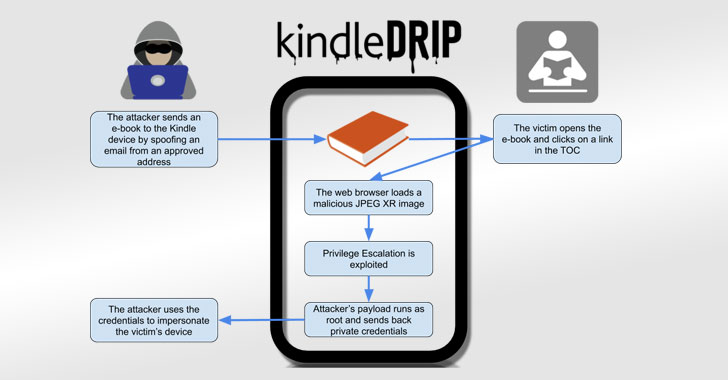
Dubbed “KindleDrip,” the exploit chain will take edge of a function known as “Ship to Kindle” to send a malware-laced doc to a Kindle gadget that, when opened, could be leveraged to remotely execute arbitrary code on the gadget and make unauthorized buys.
“The code runs as root, and the attacker only desires to know the email tackle assigned to the victim’s machine,” mentioned Yogev Bar-On, a security researcher for Readlmode Labs, in a specialized compose-up on Thursday.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The first vulnerability lets a poor actor send an e-e book to a Kindle, the next flaw permits for distant code execution though the e-ebook is parsed, and a 3rd issue will make it achievable to escalate privileges and run the code as the “root” person.
When joined alongside one another, these weaknesses could be abused to swipe unit qualifications and make buys on e-textbooks bought by the attackers by themselves on the Kindle retail store working with the target’s credit score card.
Amazon mounted the flaws on December 10, 2020, for all Kindle types produced after 2014 adhering to Bar-On’s accountable disclosure on Oct 17. He was also awarded $18,000 as component of the Amazon Vulnerability Investigation Software.
Sending a Destructive e-guide from a Spoofed Tackle
An significant element of the Mail to Kindle aspect is that it only operates when a doc is despatched as an attachment to a “kindle.com” email handle ([name]@kindle.com) from email accounts that have been earlier added to an “Authorized Personalized Doc E-mail Listing.”
Or which is how it ideally should really. What Bar-On as an alternative found was that Amazon not only did not validate the authenticity of the email sender, an e-guide that was despatched from an permitted-but-spoofed handle mechanically appeared on the library with no indication that it was gained from an email message.
But pulling this off effectively demands know-how of the location Kindle email tackle, a one of a kind “[name]@kindle.com” handle that is assigned to each and every Kindle unit or application upon registration. Whilst, in some situations, the title is suffixed by a random string, Bar-On argues that the entropy on most of the addresses is lower sufficient to be trivially guessed applying a brute-power method.
Having said that, the moment the e-ebook is sent to a target system, the attack moves to the up coming phase. It exploits a buffer overflow flaw in the JPEG XR impression format library as well as a privilege escalation bug in one particular of the root procedures (“stackdumpd”) to inject arbitrary commands and run the code as root.
Thus when an unsuspecting person opens the e-e book and faucets on a person of the hyperlinks in the table of contents, the Kindle would open up an HTML page in the browser that contained a specifically-crafted JPEG XR impression and parse the graphic file to operate the attack code — thus letting the adversary to steal the user’s qualifications, just take handle around the device, and virtually obtain private data related with the sufferer.
Amazon has now remediated the security holes by sending buyers a verification hyperlink to a pre-accredited handle in eventualities in which a document is sent from an unrecognized email address.
Software updates on Kindle gadgets are by default downloaded and mounted when linked wirelessly. Users can head to Configurations → Menu → Unit Facts to look at if their firmware is up-to-day, and if not, manually obtain and put in the 5.13.4 update to mitigate the flaws.
Identified this report fascinating? Observe THN on Facebook, Twitter and LinkedIn to read far more special articles we post.
Some areas of this short article are sourced from:
thehackernews.com

 QNAP urges users to secure against Dovecat crypto-mining malware
QNAP urges users to secure against Dovecat crypto-mining malware