The SOVA Android banking trojan is continuing to be actively created with upgraded capabilities to concentrate on no much less than 200 cellular programs, which includes banking applications and crypto exchanges and wallets, up from 90 apps when it started out.
That’s according to the hottest findings from Italian cybersecurity firm Cleafy, which observed newer variations of the malware sporting features to intercept two-factor authentication (2FA) codes, steal cookies, and broaden its concentrating on to address Australia, Brazil, China, India, the Philippines, and the U.K.
SOVA, that means Owl in Russian, arrived to mild in September 2021 when it was noticed hanging money and procuring apps from the U.S. and Spain for harvesting qualifications by means of overlay attacks by taking edge of Android’s Accessibility services.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

In less than a 12 months, the trojan has also acted as a foundation for a different Android malware named MaliBot that’s designed to focus on online banking and cryptocurrency wallet prospects in Spain and Italy.
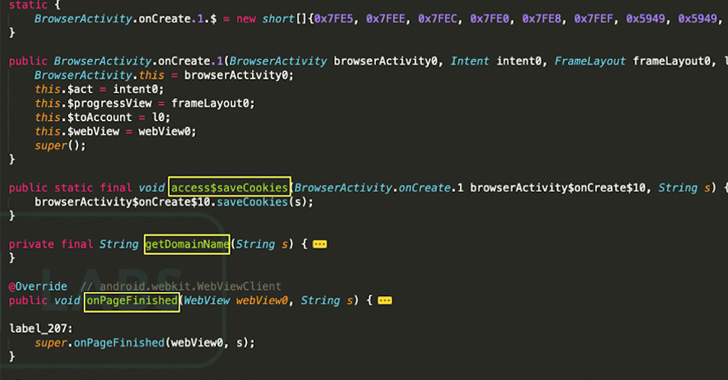
The most recent variant of SOVA, dubbed v4 by Cleafy, conceals by itself within just faux purposes that feature logos of authentic applications like Amazon and Google Chrome to deceive customers into setting up them. Other noteworthy enhancements incorporate capturing screenshots and recording the system screens.
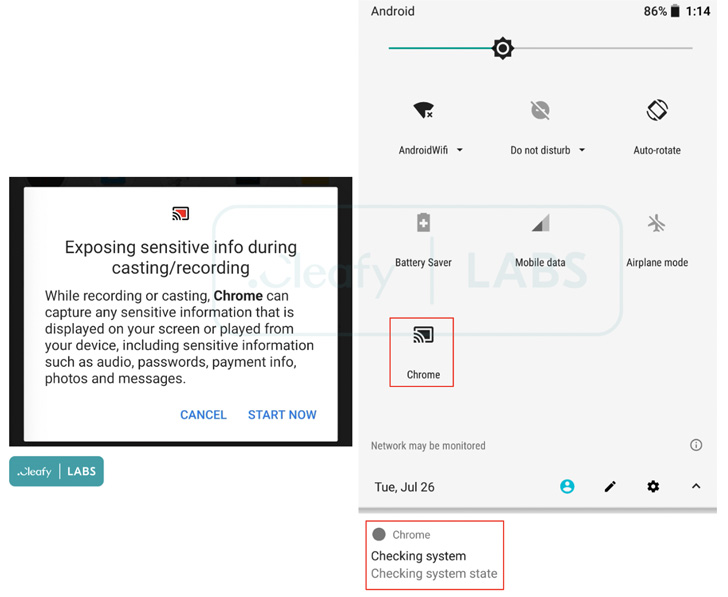
“These attributes, blended with Accessibility expert services, permit [threat actors] to carry out gestures and, consequently, fraudulent actions from the infected unit, as we have by now found in other Android Banking Trojans (e.g. Oscorp or BRATA),” Cleafy scientists Francesco Iubatti and Federico Valentini reported.
SOVA v4 is also notable for its hard work to gather sensitive facts from Binance and Have faith in Wallet, these as account balances and seed phrases. What is actually a lot more, all the 13 Russian and Ukraine-dependent banking apps that have been specific by the malware have considering that been eliminated from the variation.

To make issues even worse, the update enables the malware to leverage its huge-ranging permissions to deflect uninstallation makes an attempt by redirecting the sufferer to the residence monitor and displaying the toast information “This app is secured.”
The banking trojan, characteristic-wealthy as it is, is also predicted to integrate a ransomware ingredient in the future iteration, which is at the moment under growth and aims to encrypt all documents stored in the contaminated device using AES and rename them with the extension “.enc.”
The improvement is also most likely to make SOVA a formidable danger in the cellular risk landscape.
“The ransomware feature is very intriguing as it truly is nevertheless not a frequent one particular in the Android banking trojans landscape,” the scientists said. “It strongly leverages on the possibility that has arisen in new yrs, as cellular gadgets turned for most people the central storage for particular and business details.”
Identified this posting appealing? Comply with THN on Facebook, Twitter and LinkedIn to read through a lot more special information we article.
Some components of this posting are sourced from:
thehackernews.com

 #DEFCON: CISA Director Praises Congress and International Cybersecurity Cooperation
#DEFCON: CISA Director Praises Congress and International Cybersecurity Cooperation