Cybersecurity researchers took the wraps off a novel offer chain attack in South Korea that abuses reputable security program and stolen electronic certificates to distribute distant administration tools (RATs) on target devices.
Attributing the operation to the Lazarus Group, also known as Hidden Cobra, Slovak internet security corporation ESET said the point out-sponsored threat actor leveraged the obligatory prerequisite that internet buyers in the country must put in more security software program in purchase to avail Internet banking and critical federal government solutions.
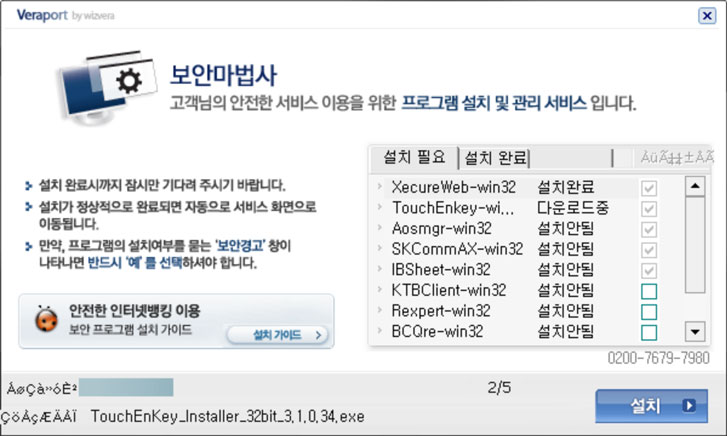
The attack, even though confined in scope, exploits WIZVERA VeraPort, which is billed as a “program developed to integrate and take care of internet banking-linked set up applications,” these kinds of as digital certificates issued by the banking companies to persons and firms to secure all transactions and system payments.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The improvement is the latest in a long history of espionage attacks from victims in South Korea, together with Procedure Troy, DDoS attacks in 2011, and in opposition to banking establishments and cryptocurrency exchanges around the final 10 years.
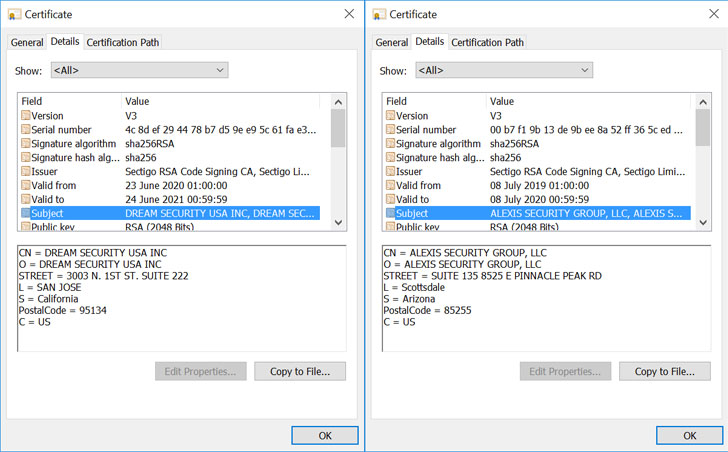
Aside from employing the aforementioned technique of installing security software package in buy to produce the malware from a reputable but compromised website, the attackers applied illegally attained code-signing certificates in buy to signal the malware samples, one of which was issued to the US department of a South Korean security company named Dream Security United states of america.
“The attackers camouflaged the Lazarus malware samples as authentic computer software. These samples have very similar file names, icons and resources as legit South Korean program,” ESET researcher Peter Kálnai claimed. “It is really the combination of compromised web-sites with WIZVERA VeraPort aid and distinct VeraPort configuration possibilities that will allow attackers to execute this attack.”
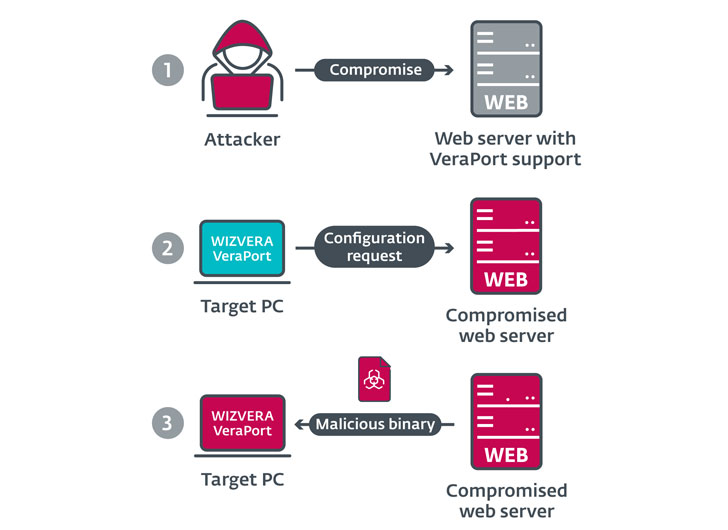
Stating that the attacks concentrate on web sites that use VeraPort — which also arrives with a base64-encoded XML configuration file made up of a checklist of computer software to put in and their related download URLs — ESET researchers claimed the adversaries changed the software to be delivered to VeraPort consumers by compromising a authentic web-site with malicious binaries that had been then signed with illicitly acquired code-signing certificates to supply the payloads.
“WIZVERA VeraPort configurations consist of an alternative to validate the electronic signature of downloaded binaries in advance of they are executed, and in most instances this selection is enabled by default,” the scientists noted. “Having said that, VeraPort only verifies that the electronic signature is valid, with no examining to whom it belongs.”
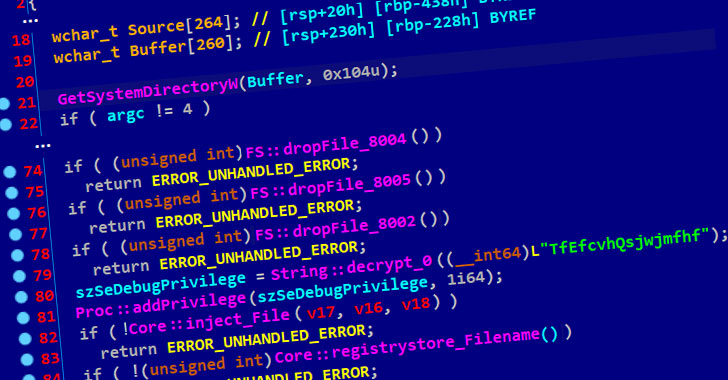
The binary then proceeds to obtain a malware dropper that extracts two more components — a loader and a downloader — the latter of which is injected into a single of the Windows processes (“svchost.exe”) by the loader. The closing-phase payload fetched by the downloader normally takes the type of a RAT that arrives geared up with instructions letting the malware to complete functions on the victim’s filesystem and down load and execute auxiliary resources from the attacker’s arsenal.
What is actually additional, the campaign seems to be what’s a continuation of a further Lazarus-mounted attack identified as Procedure BookCodes thorough by the Korea Internet & Security Agency before this April, with substantial overlaps in TTPs and command-and-manage (C2) infrastructure.
“Attackers are especially intrigued in offer-chain attacks, due to the fact they allow for them to covertly deploy malware on a lot of computers at the identical time,” the researchers concluded.
“Owners of [websites with VeraPort support] could minimize the likelihood of this kind of attacks, even if their internet sites are compromised, by enabling distinct choices (e.g. by specifying hashes of binaries in the VeraPort configuration).”
Identified this short article appealing? Follow THN on Fb, Twitter and LinkedIn to study a lot more exclusive content we publish.
Some components of this write-up are sourced from:
thehackernews.com