Just as Colonial Pipeline restored all of its devices to operational standing in the wake of a crippling ransomware incident a week back, DarkSide, the cybercrime syndicate guiding the attack, claimed it shed regulate of its infrastructure, citing a legislation enforcement seizure.
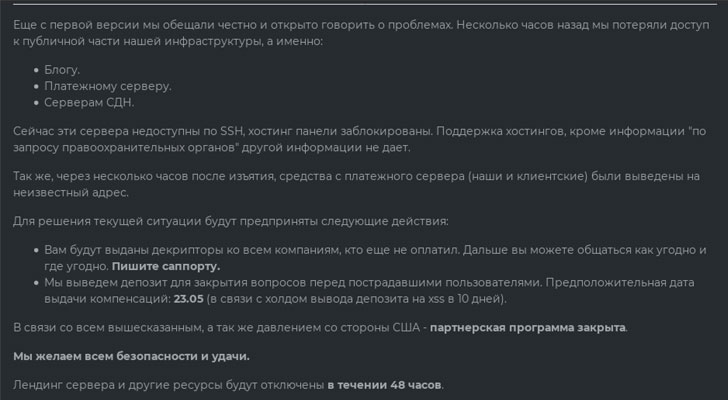
All the dark internet websites operated by the gang, which includes its DarkSide Leaks blog, ransom collection web site, and breach data articles shipping network (CDN) servers, have absent dark and continue being inaccessible as of producing. In addition, the funds from their cryptocurrency wallets ended up allegedly exfiltrated to an not known account, according to a note handed by DarkSide operators to its affiliate marketers.
“At the minute, these servers simply cannot be accessed by way of SSH, and the hosting panels have been blocked,” the announcement acquired by Intel 471 examine.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The growth will come as DarkSide closed its Ransomware-as-a-Assistance (RaaS) affiliate plan for good, with the team stating that they would issue decryptors to all their affiliate marketers for the companies that have been attacked, together with a assure to compensate all outstanding economical obligations by May 23.
While the takedowns mark a surprise twist in the Colonial Pipeline saga, it really is well worth noting that you can find no proof to publicly corroborate these promises, boosting considerations that this may possibly be an exit scam, an underhanded tactic that has plagued unlawful darknet markets in new decades, or that the gang is giving the effect that it really is retreating from the spotlight only to rebrand and stealthily proceed its operations in a further structure with no attracting unwanted consideration.
According to blockchain analytics company Elliptic, the bitcoin wallet utilized by the DarkSide ransomware group received a payment of 75 BTC ($3.2 million) on May perhaps 8 built by Colonial Pipeline, adhering to which the wallet was emptied of $5 million in bitcoin on May well 13. The wallet, which has been active due to the fact March 4, has been given a whole of 57 payments amounting to $17.5 million from 21 diverse wallets.
“There has been speculation that the bitcoins were being seized by the US federal government — if that is the case they failed to in fact seize most of Colonial Pipeline’s ransom payment — the bulk of that was moved out of the wallet on the May 9,” Elliptic co-founder Tom Robinson claimed.
By tracing the earlier cryptocurrency outflows from the wallet, Elliptic claimed 18% of the bitcoin was despatched to a small team of exchanges, with an further 4% despatched to Hydra, the world’s premier darknet bazaar which serves consumers in Russia and Japanese Europe. Hydra accounts for more than 75% of darknet market profits all over the world in 2020, positioning it as a significant player in the crypto crime landscape, for each Chainalysis.
DarkSide’s operational setbacks and the heightened scrutiny of the Colonial Pipeline attack have also set in motion a wave of RaaS bans on illicit cybercrime boards these as XSS and Exploit, posing a key limited-term disruption of the ransomware economic climate. REvil, of the prolific ransomware teams, has considering that released new restrictions that prohibit the use of its software package in opposition to wellbeing care, educational, and governing administration entities belonging to any nation.
Considered in this context, XSS, Exploit, and REvil’s steps can be interpreted as a “ripple effect” of a series of large-profile ransomware incidents in the earlier 7 days, which include that of Babuk’s on the Metropolitan Law enforcement Section, more and more landing cybercrime teams in the crosshairs of regulation enforcement.
“Needless to say, nonetheless, it’s all but selected that ransomware will stay a persistent menace for the foreseeable upcoming provided their popularity and acceptance among the cybercriminal communities,” Flashpoint mentioned. “If anything at all, ransomware attacks will most likely keep on to expand in the two scale and frequency. Soon after the closure of DarkSide, the ransomware landscape is dominated by 4 main collectives: REvil, LockBit, Avaddon, and Conti.”
In mild of XSS and Exploit refusal to host RaaS operations on their platforms, ransomware collectives are predicted to go private and publicize recruitment for new affiliates by using their possess leak web-sites.
Found this report appealing? Comply with THN on Facebook, Twitter and LinkedIn to study additional unique written content we article.
Some parts of this article are sourced from:
thehackernews.com


 RevengeRAT and AysncRAT target aerospace and travel sectors
RevengeRAT and AysncRAT target aerospace and travel sectors