Cybersecurity scientists have disclosed a critical unpatched vulnerability influencing Pling-primarily based totally free and open up-resource software program (FOSS) marketplaces for Linux platform that could be probably abused to phase offer chain attacks and achieve remote code execution (RCE).
“Linux marketplaces that are based mostly on the Pling platform are vulnerable to a wormable [cross-site scripting] with potential for a source chain attack,” Favourable Security co-founder Fabian Bräunlein reported in a technological create-up published now. “The indigenous PlingStore application is afflicted by an RCE vulnerability, which can be induced from any internet site although the app is working.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The Pling-centered application suppliers impacted by the flaw consist of —
- appimagehub.com
- retail store.kde.org
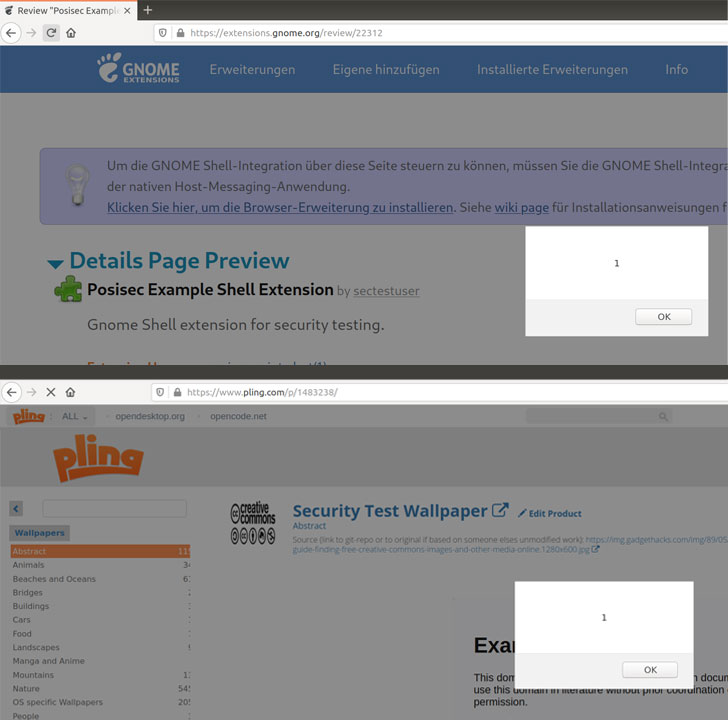
- gnome-appear.org
- xfce-look.org
- pling.com
PlingStore makes it possible for end users to research and install Linux software package, themes, icons, and other add-ons that may possibly not be accessible for down load as a result of the distribution’s software program center.
The vulnerability stems from the manner the store’s item listings page parses HTML or embedded media fields, therefore potentially permitting an attacker to inject malicious JavaScript code that could result in arbitrary code execution.
“This stored XSS could be utilized to modify active listings, or write-up new listings on the Pling store in the context of other end users, resulting in a wormable XSS,” Bräunlein mentioned.
More troublingly, this could let for a source-chain attack XSS worm whereby a JavaScript payload could be exploited by an adversary to add trojanized versions of application and tweak the metadata of a victim’s listing to contain and propagate the attack code.
With the PlingStore application acting as a single electronic storefront for all the aforementioned app suppliers, Beneficial Security famous that the XSS exploit can be activated from in just the app that, when coupled with a sandbox bypass, could guide to remote code execution.

“As the software can put in other purposes, it has a different developed-in system to execute code on the [operating system] level,” Bräunlein described. “As it turns out, that mechanism can be exploited by any web page to operate arbitrary indigenous code even though the PlingStore application is open up in the qualifications.”
Place in another way, when a consumer visits a malicious web-site through the browser, the XSS is activated within the Pling app while it’s jogging in the track record. Not only can the JavaScript code in the web-site create a relationship to the area WebSocket server which is utilised to pay attention to messages from the application, it also takes advantage of it to mail messages to execute arbitrary indigenous code by downloading and executing an .AppImage package deal file.
What is extra, a similar XSS flaw uncovered in the GNOME Shell Extensions marketplace could be leveraged to focus on the victim’s pc by issuing destructive instructions to the Gnome Shell Integration browser extension and even backdoor published extensions.
The Berlin-centered cybersecurity agency observed that the flaws have been documented to the respective job maintainers on Feb. 24, with KDE Undertaking and GNOME Security issuing patches for the flaws next disclosure. In mild of the truth that the RCE flaw related with the PlingStore stays unaddressed as yet, it truly is recommended not to operate the Electron software until finally a deal with is in put.
The report arrives considerably less than a month soon after intense security weaknesses ended up uncovered in several common Visible Studio Code extensions that could enable attackers to compromise regional equipment as nicely as construct and deployment methods by a developer’s built-in progress setting, eventually paving the way for supply chain attacks.
“[The flaws] display the more risk connected with this kind of marketplaces,” Bräunlein reported. “In this ecosystem, even comparatively compact vulnerabilities (e.g. a missing origin examine) can direct to extreme implications (push-by RCE from any browser with the susceptible software operating in history). Developers of this sort of purposes have to place in a high level of scrutiny to guarantee their security.”
Observed this article appealing? Abide by THN on Fb, Twitter and LinkedIn to study much more exclusive information we put up.
Some areas of this posting are sourced from:
thehackernews.com


 SEC Probes SolarWinds Breach Disclosure Failures
SEC Probes SolarWinds Breach Disclosure Failures