Cybersecurity researchers on Tuesday disclosed information of an unpatched vulnerability in macOS Finder that could be abused by distant adversaries to trick customers into jogging arbitrary instructions on the machines.
“A vulnerability in macOS Finder permits documents whose extension is inetloc to execute arbitrary commands, these documents can be embedded within e-mail which if the consumer clicks on them will execute the commands embedded within them without giving a prompt or warning to the user,” SSD Secure Disclosure said in a produce-up printed right now.
Park Minchan, an impartial security researcher, has been credited with reporting the vulnerability which impacts macOS versions of Huge Sur and prior.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The weakness arises owing to the manner macOS procedures INETLOC files — shortcuts to internet locations these types of as RSS feeds or Telnet connections that contains username and password for SSH — resulting in a state of affairs that makes it possible for commands embedded in individuals information to be executed devoid of any warning.

“The case here INETLOC is referring to a ‘file://’ protocol which enables operating regionally (on the user’s personal computer) saved information,” SSD reported. “If the INETLOC file is connected to an email, clicking on the attachment will induce the vulnerability without having warning.”
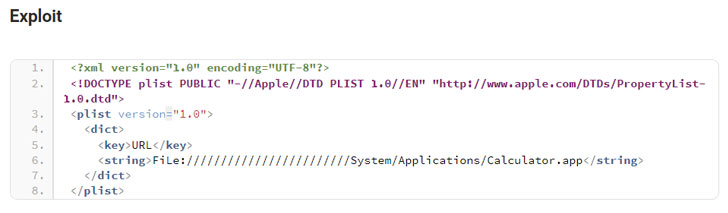
Despite the fact that newer variations of macOS have blocked the ‘file://’ prefix, making use of ‘File://’ or ‘fIle://’ has been observed to circumvent the check correctly. We have reached out to Apple, and we will update the tale if we hear back.
Identified this posting interesting? Stick to THN on Facebook, Twitter and LinkedIn to browse much more unique content we article.
Some pieces of this short article are sourced from:
thehackernews.com


 Turla APT Plants Novel Backdoor In Wake of Afghan Unrest
Turla APT Plants Novel Backdoor In Wake of Afghan Unrest