Microsoft has unveiled emergency patches to handle four previously undisclosed security flaws in Trade Server that it states are being actively exploited by a new Chinese point out-sponsored menace actor with the target of perpetrating knowledge theft.
Describing the attacks as “limited and specific,” Microsoft Risk Intelligence Heart (MSTIC) mentioned the menace actor made use of these vulnerabilities to accessibility on-premises Trade servers, in transform granting entry to email accounts and paving the way for the installation of additional malware to facilitate prolonged-time period accessibility to target environments.
The tech large largely attributed the marketing campaign with superior self-assurance to a danger actor it phone calls HAFNIUM, a point out-sponsored hacker collective running out of China, though it suspects other groups may possibly also be included.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Discussing the practices, tactics, and strategies (TTPs) of the group for the initial time, Microsoft paints HAFNIUM as a “extremely proficient and innovative actor” that mostly singles out entities in the U.S. for exfiltrating delicate facts from an array of market sectors, such as infectious disease researchers, law corporations, greater instruction institutions, defense contractors, coverage assume tanks and NGOs.
HAFNIUM is believed to orchestrate its attacks by leveraging leased virtual non-public servers in the U.S. in an try to cloak its destructive exercise.
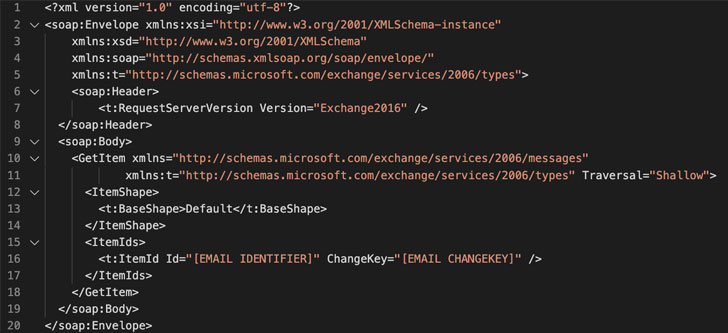
The 3-stage attack will involve attaining obtain to an Exchange Server both with stolen passwords or by working with beforehand undiscovered vulnerabilities, adopted by deploying a web shell to command the compromised server remotely. The past backlink in the attack chain makes use of distant accessibility to plunder mailboxes from an organization’s network and export the collected information to file sharing sites like MEGA.
To attain this, as numerous as 4 zero-working day vulnerabilities identified by researchers from Volexity and Dubex are employed as component of the attack chain —
- CVE-2021-26855: A server-facet ask for forgery (SSRF) vulnerability in Trade Server
- CVE-2021-26857: An insecure deserialization vulnerability in the Unified Messaging assistance
- CVE-2021-26858: A publish-authentication arbitrary file write vulnerability in Trade, and
- CVE-2021-27065: A publish-authentication arbitrary file generate vulnerability in Exchange
Though the vulnerabilities impact Microsoft Exchange Server 2013, Microsoft Trade Server 2016, and Microsoft Trade Server 2019, Microsoft mentioned it’s updating Trade Server 2010 for “Protection in Depth” needs.
Additionally, considering that the first attack necessitates an untrusted connection to Exchange server port 443, the company notes that businesses can mitigate the issue by proscribing untrusted connections or by using a VPN to individual the Trade server from external accessibility.
Microsoft, apart from stressing that the exploits have been not linked to the SolarWinds-relevant breaches, stated it has briefed correct U.S. government businesses about the new wave of attacks. But the corporation did not elaborate on how numerous businesses were specific and whether or not the attacks had been profitable.
Stating that the intrusion campaigns appeared to have commenced about January 6, 2021, Volexity cautioned its detected active in-the-wild exploitation of multiple Microsoft Exchange vulnerabilities utilised to steal email and compromise networks.
“When the attackers seem to have in the beginning flown largely less than the radar by basically thieving e-mails, they recently pivoted to launching exploits to acquire a foothold,” Volexity scientists Josh Grunzweig, Matthew Meltzer, Sean Koessel, Steven Adair, and Thomas Lancaster described in a create-up.
“From Volexity’s perspective, this exploitation seems to involve multiple operators making use of a vast wide range of tools and procedures for dumping qualifications, going laterally, and more backdooring methods.”
Microsoft Senior Menace Intelligence Analyst Kevin Beaumont has also produced a nmap plugin that can be employed to scan a network for potentially susceptible Microsoft Exchange servers.
“Even nevertheless we’ve worked quickly to deploy an update for the Hafnium exploits, we know that quite a few country-point out actors and felony teams will go speedily to take benefit of any unpatched units,” Microsoft’s Corporate Vice President of Customer Security, Tom Burt, said. “Instantly implementing modern patches is the greatest safety towards this attack.”
Provided the severity of the flaws, it is really no shock that patches have been rolled out a week forward of the firm’s Patch Tuesday plan, which is usually reserved for the next Tuesday of each individual thirty day period. Prospects employing a vulnerable edition of Trade Server are advised to install the updates right away to thwart these attacks.
Discovered this posting appealing? Abide by THN on Facebook, Twitter and LinkedIn to read through additional exceptional information we write-up.
Some areas of this article are sourced from:
thehackernews.com


 New Chrome 0-day Bug Under Active Attacks – Update Your Browser ASAP!
New Chrome 0-day Bug Under Active Attacks – Update Your Browser ASAP!