Newly found security vulnerabilities in ADT’s Blue (formerly LifeShield) home security cameras could have been exploited to hijack both of those audio and online video streams.
The vulnerabilities (tracked as CVE-2020-8101) ended up determined in the movie doorbell camera by Bitdefender scientists in February 2020 prior to they have been finally resolved on August 17, 2020.
LifeShield was acquired by Florida-based ADT Inc. in 2019, with Lifeshield’s Do-it-yourself household security answers rebranded as Blue as of January 2020. The company’s products and solutions had a 33.6% market place share in the U.S. last yr.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The security issues in the doorbell digital camera make it possible for an attacker to
- Obtain the administrator password of the digital camera by simply just figuring out its MAC address, which is applied to determine a machine uniquely
- Inject commands locally to achieve root obtain, and
- Accessibility audio and video feeds making use of an unprotected RTSP (Real-Time Streaming Protocol) server
The doorbell is built to periodically mail heartbeat messages to “cms.lifeshield.com,” made up of info these kinds of as the MAC deal with, SSID, regional IP deal with, and the wi-fi signal energy. The server, in return, responds with an authentication information that can be trivially bypassed by crafting a phony ask for by making use of the device’s MAC deal with.
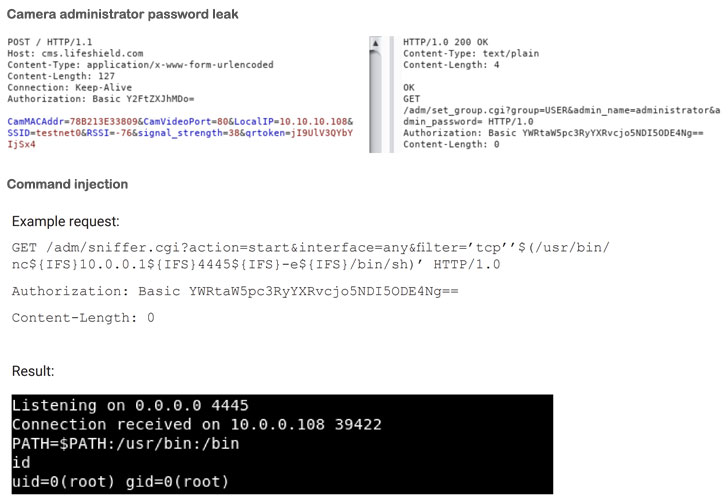
“The server appears to ignore the token and checks only the MAC deal with when sending a reaction,” the scientists mentioned, incorporating “the password for the administrator can be obtained by decoding the foundation64 authorization header obtained in this ask for.”
Armed with this admin entry to the camera’s web interface, the attacker can leverage an HTTP interface that is susceptible to command injection and acquire root obtain.
Lastly, the researchers also discovered that an unsecured RTSP server sans any credentials could be exploited to access the video stream at “rtsp://10…108:554/img/media.sav” applying any media player this sort of as VLC.
Although patches have been utilized to the production servers and all the 1,500 afflicted gadgets, with no simple way to confirm if the camera consumers set up the firmware updates, Bitdefender chose to hold off general public disclosure by a lot more than five months.
“Clients have security decisions when it comes to securing their intelligent houses or smaller corporations,” the researchers mentioned.
“Thoroughly researching IoT suppliers for security update insurance policies to their solutions, switching default passwords, separating IoTs into various subnetworks, and even routinely checking for firmware updates are only a handful of practical and arms-on security strategies that any person can adhere to.”
Discovered this article interesting? Follow THN on Fb, Twitter and LinkedIn to read additional exclusive content we article.
Some parts of this posting are sourced from:
thehackernews.com


 Growing Digital Adoption Providing Extra Opportunities for Cyber-Criminals
Growing Digital Adoption Providing Extra Opportunities for Cyber-Criminals