Microsoft on Thursday took the wraps off an ongoing campaign impacting preferred web browsers that stealthily injects malware-infested adverts into lookup results to receive dollars by means of affiliate advertising and marketing.
“Adrozek,” as it is really termed by the Microsoft 365 Defender Investigation Crew, employs an “expansive, dynamic attacker infrastructure” consisting of 159 exclusive domains, every single of which hosts an typical of 17,300 unique URLs, which in switch host a lot more than 15,300 exclusive malware samples.
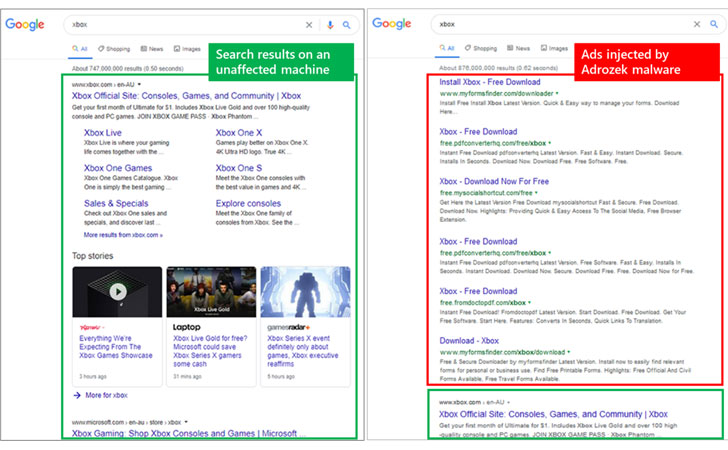
The marketing campaign — which impacts Microsoft Edge, Google Chrome, Yandex Browser, and Mozilla Firefox browsers on Windows — aims to insert supplemental, unauthorized advertisements on top of genuine advertisements shown on lookup engine success web pages, primary customers to click on these advertisements inadvertently.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Microsoft reported the browser modifier malware was noticed because Could this calendar year, with about 30,000 equipment each and every day at its peak in August.
“Cybercriminals abusing affiliate programs is not new—browser modifiers are some of the oldest kinds of threats,” the Windows maker claimed. “However, the fact that this marketing campaign utilizes a piece of malware that affects numerous browsers is an indication of how this threat style proceeds to be increasingly refined. In addition, the malware maintains persistence and exfiltrates site credentials, exposing influenced equipment to extra hazards.”
After dropped and mounted on goal methods by way of travel-by downloads, Adrozek proceeds to make a number of alterations to browser configurations and security controls so as to set up destructive insert-ons that masquerade as genuine by repurposing the IDs of respectable extensions.
While modern-day browsers have integrity checks to avert tampering, the malware cleverly disables the element, therefore enabling the attackers to circumvent security defenses and exploit the extensions to fetch extra scripts from remote servers to inject bogus advertisements and acquire revenue by driving targeted visitors to these fraudulent advert pages.
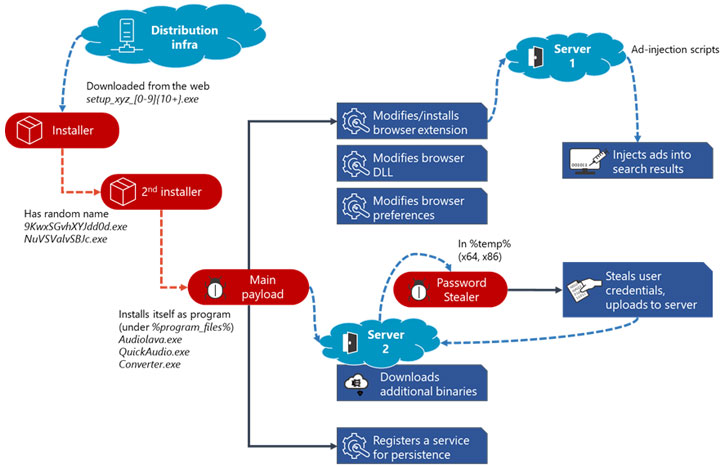
What’s a lot more, Adrozek goes just one stage even further on Mozilla Firefox to carry out credential theft and exfiltrate the facts to attacker-managed servers.
“Adrozek exhibits that even threats that are not thought of as urgent or critical are progressively getting to be additional complex,” the researchers said.
“And while the malware’s major intention is to inject ads and refer site visitors to certain sites, the attack chain will involve innovative habits that will allow attackers to acquire a strong foothold on a gadget. The addition of credential theft behavior reveals that attackers can extend their goals to acquire edge of the access they are ready to get.
Discovered this write-up appealing? Adhere to THN on Facebook, Twitter and LinkedIn to read through additional unique articles we post.
Some sections of this post are sourced from:
thehackernews.com


 Google, Intel, Zoom and others form Modern Computing Alliance
Google, Intel, Zoom and others form Modern Computing Alliance