Ransomware is just one of the major cyber security threats experiencing firms currently. It’s a form of malware that attackers can use to lock a unit or encrypt its contents in order to extort dollars from the operator or operator.
Specified its possible to provide a superior return on expenditure, and the relative simplicity at which it can spread, this type of attack has become really well-known between cyber criminals. It was lately named the largest menace facing modest-to-medium-sized businesses (SMBs) as attackers get benefit of the COVID-19 pandemic to attack personnel exterior of the place of work.
In accordance to figures from cloud cyber security corporation Datto, 59% of MSPs claimed a change to distant doing the job experienced resulted in increased ransomware attacks, and 60% reported that their SMB consumers experienced been strike by ransomware in the third quarter of 2020.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
How ransomware is effective
Substantially like other malware styles, ransomware is typically spread by tricking victims into downloading malicious email attachments, which prompt scripts to instantly run on their system. On the other hand, it’s also possible for ransomware to be unfold wherever you can find an option to disguise malicious scripts.
Ransomware normally starts an attack by seeking to stay undetected, bit by bit encrypting files a single after a different to steer clear of suspicion. However, not like other variants, ransomware then helps make its existence recognised to the consumer as soon as it has encrypted more than enough information, usually by way of a ransom observe or splash display screen.
It truly is from this splash monitor that consumers are to start with told that their data files are locked and that in buy to retrieve their information they are demanded to pay back a monetary sum. The exact wording of the demands differ involving ransomware strains, but most desire some form of payment within a specified timeframe.
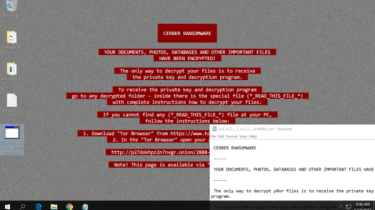
The splash monitor involved with the Cerber ransomware
Some messages are intense in the hopes of scaring the person into a quick payment, while many others endeavor to masquerade as respectable organisations, this kind of as the FBI. For illustration, the Jigsaw ransomware pressure makes an attempt to rush the consumer into paying out its payment by deleting a file for every single hour that the need is disregarded, and will normally delete close to 1,000 files if the person attempts to reboot their technique.
The to start with instance of ransomware was the relatively unsuccessful ‘AIDS Trojan’ which struck in 1989, encrypting the identify of information, relatively than the written content of the information, while the decryption crucial was hidden inside the malware’s code. Despite these problems in deployment, the attack was the initial circumstance of a hacker demanding dollars in trade for the secure return of stolen details.
Attackers continue to operate underneath the identical main principles, but are ordinarily far much more effective, and far more frequently than not desire payment not in physical currency, but in cryptocurrencies. Most attackers favour Bitcoin or Monero, which are inherently tough to trace.
Ransomware in 2020
There are hundreds of ransomware strains functioning throughout the earth, and which certain menace you are possible to facial area can depend on the continent, the nation, or even the city in which you operate. For case in point, we a short while ago examined the most recent strains attacking companies working throughout the UK, but the photograph can change wildly from location to area.
Ryuk is just one of the most common ransomware strains across the entire world, and the latest figures clearly show it accounted for a 3rd of all ransomware attacks in 2020. The ransomware, which has strike higher-profile providers including French IT companies big Sopra Steria, was recorded in 67 million attacks in 2020, compared to just 5,123 attacks ended up recorded through the first three quarters of 2019, when compared to 67 million for the duration of 2020, in accordance to study by SonicWall.
Maze is a different. This ransomware pressure has been very lively above the previous 12 months and a 50 percent, most not too long ago crippling the systems of several massive businesses, including Canon in August and Xerox in July. Even so, in November 2020, the Maze ransomware gang announced that it’s shutting down its operations for great.
What is actually also common is a find selection of strains which are being presented up for use. Known as ransomware as a support, this product entails criminals paying founded hacker groups to coordinate a ransomware marketing campaign from wanted targets. This will make it doable for criminals to attack a target devoid of the risk of remaining recognized and without the require for in-depth coding knowledge.
This has also appreciably decreased the obstacles to entry, indicating that anybody, furnished they have the hard cash and inclination to do so, can start a coordinated and detailed ransomware attack.
In accordance to the Beazley Breach Reaction group, there was a 105% 12 months-about-calendar year enhance in the range of ransomware attacks from firms in Q1 of 2019. The identical report identified that the normal ransomware need has also improved by 93% to $224,871, even though this has been skewed considerably by a small number of large payouts.
However, large payouts are immediately starting to be ordinary, as ransomware has started off to shift its concentration to larger organisations or critical community services. For case in point, two cities in Florida agreed to spend collectively $1.1 million to regain obtain to their devices next a popular community sector ransomware attack.
Really should I fork out the ransom?
By layout, ransomware is amazingly disruptive for companies, and it can be tempting to take the fast way out and submit to requires – after all, every single minute your small business is offline, the larger the financial and reputational problems may well be.
Nonetheless, most industry experts concur that having to pay a ransomware demand is the worst factor you can do. Ransomware has grow to be exceptionally lucrative, with 121 million attacks recorded in the initially 50 % of 2020 alone, up 20% about the prior year. This is totally fuelled by the shakedown of its victims, and the far more that organizations give in to requires, even if the cost is fairly very low, the a lot more hackers are going to use this tactic.
Even if you never purchase into that strategy of the greater great, there’s finally no guarantee that hackers will uphold their stop of the bargain. Of training course, it is in a hacker’s possess pursuits to do so, as victims will be unwilling to hand over their funds if they think their attackers will split and operate, but there is almost nothing to protect against them from deleting facts the moment they get their money.
However, in a lot of instances, data encrypted by ransomware is very best assumed of as misplaced. How harmful that will be for your business will count on how sturdy your information backups and recovery processes are. With a strong catastrophe recovery plan in area, it’s attainable to choose the sting out of a ransomware attack as before long as it begins.
2017 NHS ransomware attack
Most likely the most famous ransomware attack to hit the UK occurred on 11 May perhaps 2017, when the NHS and a quantity of big organisations in England and Scotland have been hit by WannaCry. This pressure is believed to have quietly spread across Europe, infecting key organisations together with Telefonica in Spain, Deutsche Bahn in Germany, Renault and FedEx, before activating. It truly is thought hundreds of thousands of personal computer techniques throughout 99 nations ended up afflicted.
The an infection spread via three vectors. The first payload (i.e. the ransomware application recognised as WannaCry or WannaCrypt) was introduced into the organisations’ network by using a phishing email, with a user clicking on a malicious url or downloading a destructive file.
The infection then unfold speedily by the network making use of two tools believed to have been designed by the NSA the EternalBlue exploit and DoublePulsar backdoor which had been unveiled into the wild by the ShadowBrokers hacking group alongside with a amount of other cyber weapons.
All the contaminated pcs on the network for that reason had their files encrypted with a ransom message shown on their display screen demanding of all-around $300 in Bitcoin to be compensated inside 3 days or $600 in just 7 days. It’s unclear how numerous organisations paid out, but by Monday 15 May, the cyber criminals had designed around $40,000 in accordance to the URLs involved with the ransom demands.
Microsoft had released a patch for the vulnerability, which affected all Windows working programs from Windows 7 by means of to 8.1, again in March. Even so, it hadn’t been utilized to all components of the afflicted organisations’ network. There are numerous reasons this may perhaps have occurred, which includes the have to have for organisations to have out a staged roll-out and potential conflicts with other critical systems and software program.
An additional cause is that lots of organisations nevertheless operate Windows XP, the moment once again ordinarily owing to compatibility issues. As XP is out of guidance, no patch for it was released in March, leaving all devices managing it susceptible to this attack. 90% of the NHS’ IT estate was regarded to be managing Windows XP at the starting of 2017, with its custom help contract owning been terminated in 2015.
Offered the magnitude of the attack, nevertheless, Microsoft did create and issue a patch for XP, but recommended that organisations and persons really should constantly utilize the most up-to-date software package updates as shortly as achievable to secure in opposition to threats of this kind.
Some pieces of this post are sourced from:
www.itpro.co.uk


 How to wipe a laptop easily and securely
How to wipe a laptop easily and securely