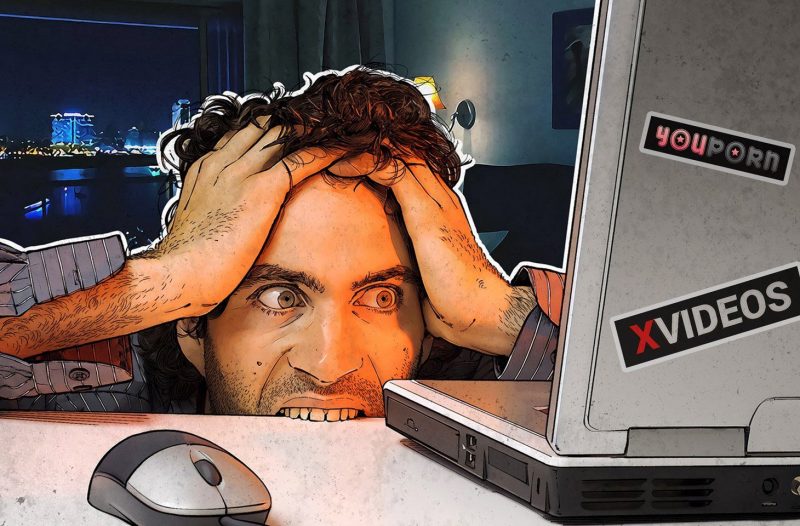
A comment spammer flooded Babuk’s new ransomware discussion board with homosexual orgy porn GIFs and demanded $5K in bitcoin.
The Babuk ransomware gang’s new rebrand is not heading so very well. It looks the cybercriminal team has been a target of a ransomware attack of its own.
Babuk’s newest endeavor, a Dark Web ransomware forum identified as RAMP, was crippled by a spammer over the weekend who overloaded the site with very same-intercourse pornographic GIFs, in accordance to Recorded Upcoming.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The attacker informed Babuk they desired $5,000. Babuk informed them to pound sand, refused to pay and deleted the initial post. But even after wiping the forum several moments, Recorded Potential explained the attacker was however in a position to bombard the forum with pornographic GIFs.
Malware supply code detector vx-underground also picked up on the feud, calling it “Ransomware team drama.”
“RAMP, the discussion board commenced by Babuk ransomware group, has found a surge of flooding and spamming. An mysterious particular person is stating they have 24 hours to spend $5,000 or else,” vx underground posted. “Ransomware actors are ransoming other ransomware actors.”
Ransomware team drama.
RAMP, the forum started out by Babuk ransomware group, has found a surge of flooding and spamming. An not known specific is stating they have 24 hours to fork out $5,000 or else.
Ransomware actors are ransoming other ransomware actors. pic.twitter.com/Iu1vfQtBLL
— vx-underground (@vxunderground) July 23, 2021
Babuk’s Reboot Stalls
Babuk has had a rough number of months.
Following hitting the Washington D.C. law enforcement division in April with a ransomware attack, the group vowed to retire in a quick goodbye observe. If they did retire, it was short-lived. In May possibly, Babuk started off leaking data from the D.C. law enforcement breach.
By early this month, the group had uploaded its ransomware supply code to VirusTotal and renamed its leak website Payload.bin in what appeared like a start of a ransomware-as-a-assistance (RaaS) business enterprise.
Then the operators had a new business enterprise plan: to hop on the chance remaining by malware discussions finding shushed in the wake of the Colonial Pipeline attack. In late May well, the XSS underground discussion board experienced banned ransomware advertisements. The Exploit forum adopted match in a day, and a handful of hrs later on, the operators guiding the RAID forum rounded it out a trio of ransomware-chat bans.
Then, two weeks back, Babuk introduced RAMP: a new forum in which menace actors could connect and brazenly explore their ransomware organization.
It is however to be determined what impact this newest spammer attack will have on Babuk’s ability to court cybercriminals in the gang’s corner of the dark web.
At the time when Maze declared its retirement, Adam Kujawa, director of Malwarebytes Labs, warned from trying to go through far too considerably into anything these cybercrime groups say. “Ransom actors are expert liars and scammers to feel nearly anything they say is a oversight,” he reportedly mentioned.
Now that ransomware actors have turned on a single yet another, items might be about to get even a lot more attention-grabbing.
Some pieces of this article are sourced from:
threatpost.com

 Microsoft Rushes Fix for ‘PetitPotam’ Attack PoC
Microsoft Rushes Fix for ‘PetitPotam’ Attack PoC