Threat actors have been found out distributing a new credential stealer published in AutoHotkey (AHK) scripting language as part of an ongoing marketing campaign that started off early 2020.
Shoppers of financial establishments in the US and Canada are amid the most important targets for credential exfiltration, with a particular emphasis on banks these as Scotiabank, Royal Lender of Canada, HSBC, Alterna Financial institution, Cash 1, Manulife, and EQ Financial institution. Also incorporated in the list is an Indian banking business ICICI Lender.
AutoHotkey is an open-resource tailor made scripting language for Microsoft Windows aimed at supplying quick hotkeys for macro-creation and software automation that enables consumers to automate repetitive tasks in any Windows software.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
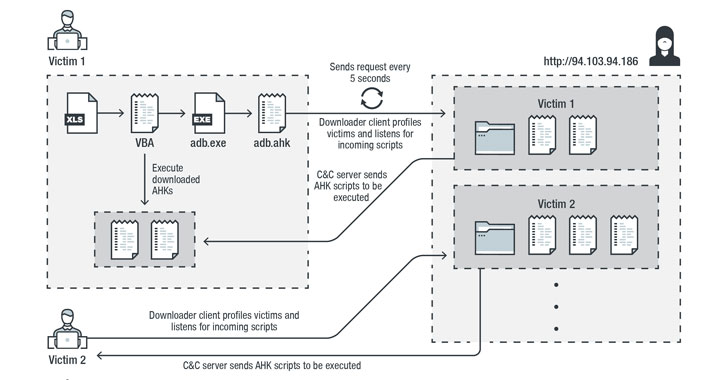
The multi-phase infection chain commences with a malware-laced Excel file that’s embedded with a Visible Essential for Purposes (VBA) AutoOpen macro, which is subsequently utilised to drop and execute the downloader shopper script (“adb.ahk”) via a reputable moveable AHK script compiler executable (“adb.exe”).
The downloader client script is also dependable for accomplishing persistence, profiling victims, and downloading and running further AHK scripts from command-and-management (C&C) servers positioned in the US, the Netherlands, and Sweden.
What makes this malware different is that as a substitute of obtaining instructions specifically from the C&C server, it downloads and executes AHK scripts to accomplish diverse jobs.
“By accomplishing this, the attacker can come to a decision to add a specific script to realize custom-made jobs for each and every person or group of customers,” Pattern Micro researchers reported in an evaluation. “This also helps prevent the main parts from getting uncovered publicly, especially to other scientists or to sandboxes.”
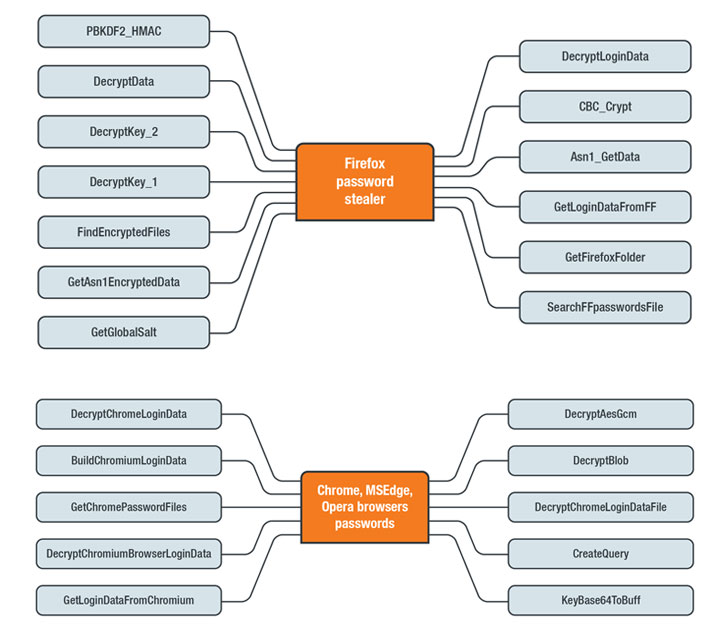
Main among the them is a credential stealer that targets various browsers these as Google Chrome, Opera, Microsoft Edge, and much more. The moment mounted, the stealer also tries to down load an SQLite module (“sqlite3.dll”) on the infected machine, applying it to accomplish SQL queries from the SQLite databases inside browsers’ app folders.
In the final stage, the stealer collects and decrypts qualifications from browsers and exfiltrates the information to the C&C server in plaintext by using an HTTP Post request.
Noting that the malware factors are “well organized at the code amount,” the researchers counsel the inclusion of usage guidelines (written in Russian) could imply a “hack-for-use” group that is behind the attack chain’s creation and is supplying it to others as a support.
“By using a scripting language that lacks a developed-in compiler inside of a victim’s working program, loading malicious factors to achieve several responsibilities individually, and transforming the C&C server routinely, the attacker has been ready to conceal their intention from sandboxes,” the researchers concluded.
Located this short article interesting? Follow THN on Facebook, Twitter and LinkedIn to go through a lot more exceptional information we publish.
Some parts of this posting are sourced from:
thehackernews.com

 Data questions remain as UK exits EU
Data questions remain as UK exits EU