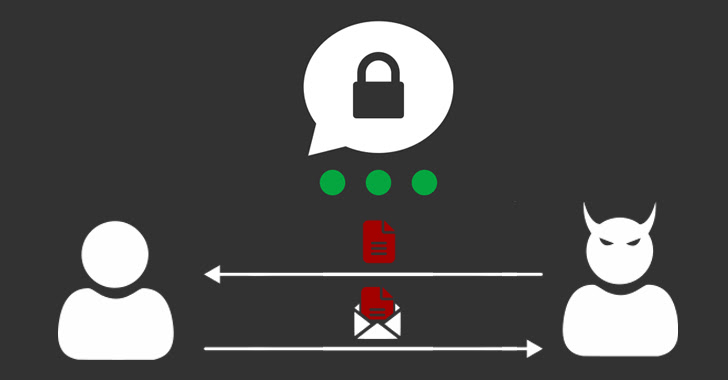
A extensive analysis of the cryptographic protocols applied in the Swiss encrypted messaging application Threema has unveiled a number of loopholes that could be exploited to break authentication protections and even recuperate users’ private keys.
The seven attacks span a few unique threat products, in accordance to ETH Zurich scientists Kenneth G. Paterson, Matteo Scarlata, and Kien Tuong Truong, who reported the issues to Threema on Oct 3, 2022. The weaknesses have since been resolved as portion of updates released by the company on November 29, 2022.
Threema is an encrypted messaging application that is used by additional than 11 million end users as of Oct 2022. “Security and privacy are deeply ingrained in Threema’s DNA,” the corporation statements on its site.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Officially employed by the Swiss Govt and the Swiss Military, it can be also marketed as a secure choice together with other providers such as Signal, Meta-owned WhatsApp, and Telegram.
Although Threema has been subjected to 3rd-party code audits at minimum twice – when in 2019 and a second time in 2020 – the hottest results present that they were not comprehensive more than enough to uncover the challenges current in the “cryptographic main of the software.”
“Ideally, any application working with novel cryptographic protocols must appear with its have formal security analyses (in the type of security proofs) in order to supply powerful security assurances,” the researchers explained.
In a nutshell, the attacks could pave the way for a broad range of exploitation scenarios, specifically making it possible for an attacker to impersonate a consumer, reorder the sequence of messages exchanged amongst two parties, clone the account of a victim user, and even leverage the backup mechanism to recuperate the user’s non-public essential.
The latter two attack pathways, which call for direct entry to a victim’s gadget, could have intense effects, as it allows the adversary to stealthily access the users’ foreseeable future messages with no their awareness.
Also uncovered is a case of replay and reflection attack linked to its Android app that takes place when end users reinstall the application or change equipment, granting a undesirable actor with entry to Threema servers to replay outdated messages. A very similar replay attack was identified in January 2018.
Final but not minimum, an adversary could also phase what is actually known as a Kompromat attack wherein a malicious server methods a shopper “into unwittingly encrypting a concept of the server’s selecting that can be delivered to a distinct person.”
It is worth noting that this attack was previously described to Threema by College of Erlangen-Nuremberg researcher Jonathan Krebs, prompting the firm to ship fixes in December 2021 (variation 4.62 for Android and edition 4.6.14 for iOS).
“Making use of contemporary, safe libraries for cryptographic primitives does not, on its personal, direct to a protected protocol structure,” the scientists explained. “Libraries these types of as NaCl or libsignal can be misused although making far more elaborate protocols and developers have to be cautious not to be lulled into a untrue perception of security.”
“While the mantra ‘don’t roll your very own crypto’ is now extensively regarded, it really should be prolonged to ‘don’t roll your personal cryptographic protocol’ (assuming 1 presently exists that fulfills the developer’s specifications),” they added. “In the case of Threema, the bespoke C2S protocol could be changed by TLS.”
When attained for comment, Threema instructed The Hacker Information that it has introduced a new conversation protocol termed Ibex that renders “some of the issues out of date,” including it “acted instantly to implement fixes for all results in weeks.”
“Even though some of the conclusions […] could be interesting from a theoretical standpoint, none of them ever experienced any considerable serious-entire world affect,” the enterprise further more mentioned. “Most believe substantial and unrealistic stipulations that would have much higher effects than the respective discovering by itself.”
It also pointed out that some of the attacks financial institution on owning bodily access to an unlocked cell device more than an prolonged time interval, at which position the “complete device ought to be deemed compromised.”
The analyze comes nearly six months after ETH Zurich scientists thorough critical shortcomings in the MEGA cloud storage provider that could be weaponized to crack the private keys and entirely compromise the privacy of the uploaded information.
Then in September 2022, a different group of researchers disclosed a host of security flaws in the Matrix decentralized, authentic-time interaction protocol that grant a malicious server operator the potential to read messages and impersonate customers, correctly undermining the confidentiality and authenticity of the company.
Observed this post intriguing? Observe us on Twitter and LinkedIn to read through extra exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com

 Italian Users Warned of Malware Attack Targeting Sensitive Information
Italian Users Warned of Malware Attack Targeting Sensitive Information