A 1st-of-its-kind malware concentrating on Amazon Web Services’ (AWS) Lambda serverless computing system has been learned in the wild.
Dubbed “Denonia” right after the name of the domain it communicates with, “the malware uses more recent tackle resolution approaches for command and control website traffic to evade regular detection measures and virtual network access controls,” Cado Labs researcher Matt Muir explained.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The artifact analyzed by the cybersecurity organization was uploaded to the VirusTotal database on February 25, 2022, sporting the identify “python” and packaged as a 64-little bit ELF executable.
Nonetheless, the filename is a misnomer, as Denonia is programmed in Go and harbors a custom-made variant of the XMRig cryptocurrency mining computer software. That said, the manner of preliminary obtain is not known, while it is suspected it may possibly have involved the compromise of AWS Entry and Solution Keys.
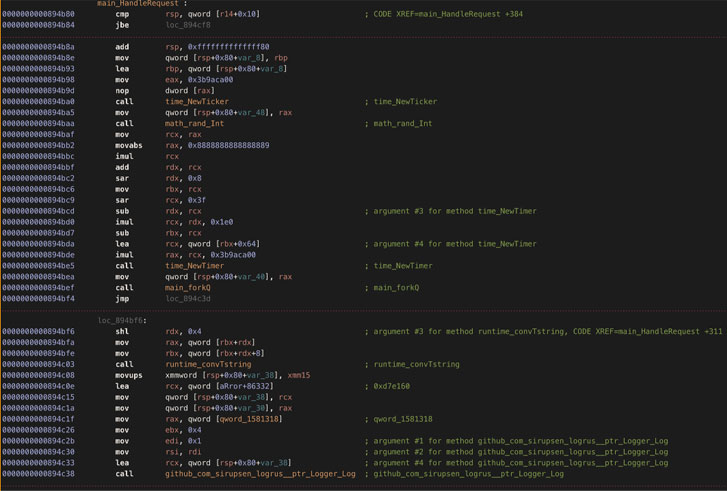
One more noteworthy attribute of the malware is its use of DNS over HTTPS (DoH) for communicating with its command-and-control server (“gw.denonia[.]xyz”) by concealing the site visitors inside encrypted DNS queries.
Even so, “python” is not the only sample of Denonia unearthed so considerably, what with Cado Labs obtaining a 2nd sample (named “bc50541af8fe6239f0faa7c57a44d119.virus”) that was uploaded to VirusTotal on January 3, 2022.
“Whilst this initially sample is pretty innocuous in that it only runs crypto-mining computer software, it demonstrates how attackers are employing advanced cloud-particular expertise to exploit intricate cloud infrastructure, and is indicative of likely long run, far more nefarious attacks,” Muir mentioned.
Identified this short article appealing? Abide by THN on Facebook, Twitter and LinkedIn to read a lot more distinctive content material we publish.
Some elements of this write-up are sourced from:
thehackernews.com




 Hamas-linked Hackers Targeting High-Ranking Israelis Using ‘Catfish’ Lures
Hamas-linked Hackers Targeting High-Ranking Israelis Using ‘Catfish’ Lures