A earlier undocumented Go-based mostly malware is targeting Redis servers with the aim of getting handle of the contaminated systems and probable building a botnet network.
The attacks entail taking benefit of a critical security vulnerability in the open source, in-memory, crucial-value shop that was disclosed previously this calendar year to deploy Redigo, in accordance to cloud security agency Aqua.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Tracked as CVE-2022-0543 (CVSS score: 10.), the weakness pertains to a situation of sandbox escape in the Lua scripting motor that could be leveraged to attain distant code execution.
This is not the initial time the flaw has arrive less than active exploitation, what with Juniper Threat Labs uncovering attacks perpetrated by the Muhstik botnet in March 2022 to execute arbitrary instructions.
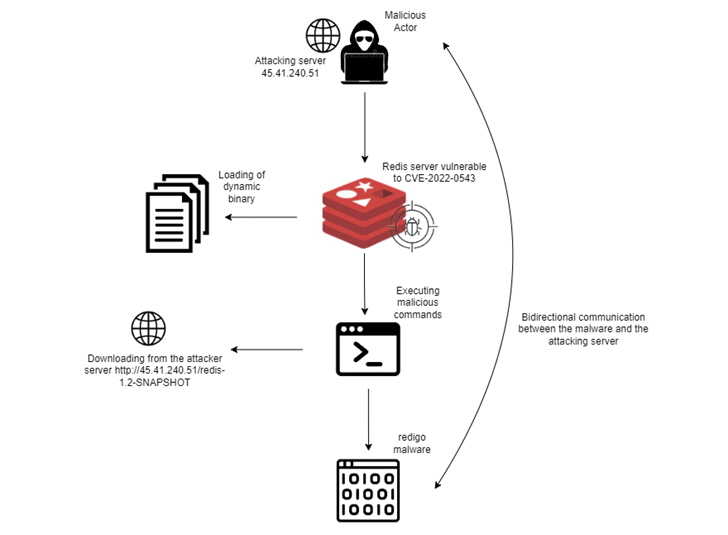
The Redigo infection chain is equivalent in that the adversaries scan for uncovered Redis servers on port 6379 to create original obtain, adhering to it up by downloading a shared library “exp_lin.so” from a remote server.
This library file comes with an exploit for CVE-2022-0543 to execute an arbitrary command in purchase to retrieve Redigo from the identical server, in addition to taking actions to mask their activity by simulating authentic Redis cluster conversation above port 6379.
“The dropped malware mimics the Redis server conversation which permitted the adversaries to conceal communications involving the qualified host and the C2 server,” Aqua researcher Nitzan Yaakov described.
It can be not known what the finish intention of the attacks are, but it really is suspected that the compromised hosts could be co-opted into a botnet to aid DDoS attacks or employed to steal delicate facts from the database server to even more lengthen their get to.
Located this posting exciting? Adhere to us on Twitter and LinkedIn to browse additional exclusive written content we publish.
Some components of this report are sourced from:
thehackernews.com


 NATO Launches Massive Cyber-Defense Exercise
NATO Launches Massive Cyber-Defense Exercise