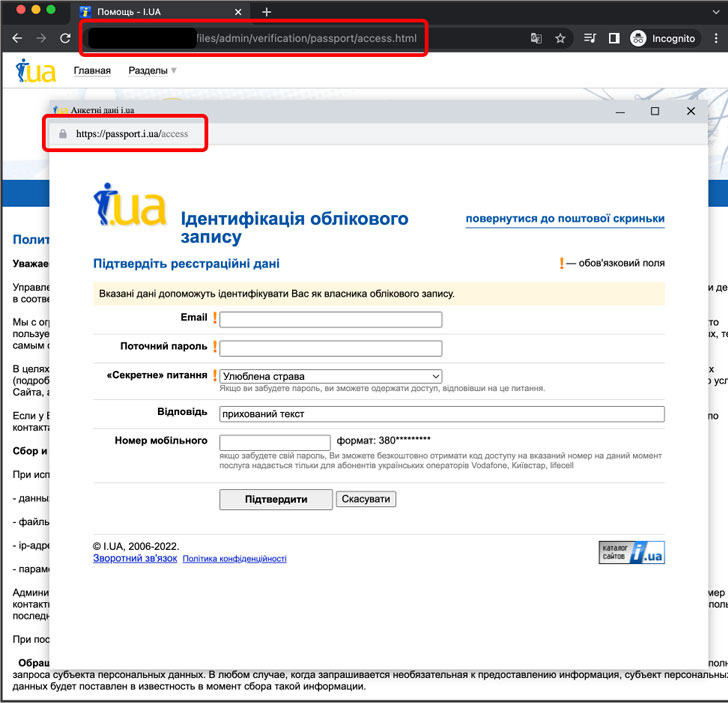
A Belarusian menace actor recognized as Ghostwriter (aka UNC1151) has been spotted leveraging the not too long ago disclosed browser-in-the-browser (BitB) technique as component of their credential phishing campaigns exploiting the ongoing Russo-Ukrainian conflict.
The strategy, which masquerades as a reputable domain by simulating a browser window inside the browser, helps make it probable to mount convincing social engineering strategies.
“Ghostwriter actors have swiftly adopted this new procedure, combining it with a formerly observed approach, hosting credential phishing landing webpages on compromised web-sites,” Google’s Danger Examination Team (TAG) reported in a new report, utilizing it to siphon credentials entered by unsuspected victims to a remote server.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Among the other teams working with the war as a lure in phishing and malware campaigns to deceive targets into opening fraudulent e-mail or one-way links involve Mustang Panda and Scarab as effectively as country-condition actors from Iran, North Korea, and Russia.
Also integrated in the record is Curious Gorge, a hacking crew that TAG has attributed to China’s People’s Liberation Military Strategic Assistance Force (PLASSF), which has orchestrated attacks in opposition to government and navy corporations in Ukraine, Russia, Kazakhstan, and Mongolia.
A 3rd established of attacks noticed over the earlier two-7 days time period originated from the Russia-based mostly hacking group regarded as COLDRIVER (aka Calisto). TAG said that the actor staged credential phishing strategies concentrating on various U.S.-primarily based NGOs and feel tanks, the army of a Balkans place, and an unnamed Ukrainian defense contractor.

“However, for the initial time, TAG has observed COLDRIVER campaigns targeting the army of a number of Japanese European countries, as well as a NATO Centre of Excellence,” TAG researcher Billy Leonard said. “These strategies were sent utilizing newly established Gmail accounts to non-Google accounts, so the results level of these campaigns is unfamiliar.”
Viasat breaks down February 24 Attack
The disclosure arrives as U.S.-centered telecommunications organization Viasat spilled facts of a “multifaceted and deliberate” cyberattack in opposition to its KA-SAT network on February 24, 2022, coinciding with Russia’s armed forces invasion of Ukraine.
The attack on the satellite broadband services disconnected tens of thousands of modems from the network, impacting many customers in Ukraine and throughout Europe and impacting the functions of 5,800 wind turbines belonging to the German organization Enercon in Central Europe.
“We imagine the purpose of the attack was to interrupt assistance,” the company described. “There is no proof that any stop-user info was accessed or compromised, nor consumer personalized gear (PCs, mobile units, etc.) was improperly accessed, nor is there any evidence that the KA-SAT satellite alone or its supporting satellite floor infrastructure alone have been directly concerned, impaired or compromised.”
Viasat linked the attack to a “floor-primarily based network intrusion” that exploited a misconfiguration in a VPN equipment to get distant accessibility to the KA-SAT network and execute destructive instructions on the modems that “overwrote key data in flash memory,” rendering them temporarily not able to entry the network.
Russian dissidents qualified with Cobalt Strike
The relentless attacks are the most recent in a very long checklist of malicious cyber pursuits that have emerged in the wake of the continuing conflict in Jap Europe, with federal government and professional networks struggling from a string of disruptive details wiper bacterial infections as nicely as a collection of ongoing distributed denial-of-services (DDoS) attacks.
This has also taken the variety of compromising genuine WordPress sites to inject rogue JavaScript code with the intention of carrying out DDoS attacks towards Ukrainian domains, according to scientists from the MalwareHunterTeam.
But it is not just Ukraine. Malwarebytes Labs this 7 days laid out specifics of a new spear-phishing marketing campaign focusing on Russian citizens and federal government entities in an endeavor to deploy pernicious payloads on compromised systems.
“The spear phishing emails are warning men and women that use web sites, social networks, quick messengers and VPN products and services that have been banned by the Russian Governing administration and that legal expenses will be laid,” Hossein Jazi stated. “Victims are lured to open a malicious attachment or website link to find out extra, only to be infected with Cobalt Strike.”
The malware-laced RTF documents incorporate an exploit for the commonly abused MSHTML remote code execution vulnerability (CVE-2021-40444), top to the execution of a JavaScript code that spawns a PowerShell command to download and execute a Cobalt Strike beacon retrieved from a remote server.
A further cluster of action possibly relates to a Russian risk actor tracked as Carbon Spider (aka FIN7), which has employed a identical maldocs entice that’s engineered to fall a PowerShell-dependent backdoor capable of fetching and working a following-stage executable.
Malwarebytes also explained it has detected a “considerable uptick in malware people staying made use of with the intent of stealing details or otherwise getting accessibility in Ukraine,” like Hacktool.LOIC, Ainslot Worm, FFDroider, Formbook, Remcos, and Quasar RAT.
“Even though these family members are all rather typical in the cybersecurity globe, the truth that we witnessed spikes almost just when Russian troops crossed the Ukrainian border would make these developments appealing and unusual,” Adam Kujawa, director of Malwarebytes Labs, claimed in a statement shared with The Hacker Information.
Uncovered this posting appealing? Observe THN on Facebook, Twitter and LinkedIn to read additional exclusive articles we submit.
Some pieces of this article are sourced from:
thehackernews.com


 Patch finally released for Spring4Shell zero-day after vulnerable businesses put on high alert
Patch finally released for Spring4Shell zero-day after vulnerable businesses put on high alert